Drastically reduce the time and effort required for reverse engineering and security auditing of large enterprise applications.
As part of our mission to support the cybersecurity community, we’ve added Hyoketsu, a new open-source research tool, to the Searchlight Cyber Tools Site. Using this new tool, security teams can drastically reduce the time and effort required for reverse engineering and security auditing of large enterprise applications.
“It’s extremely fast, because we’ve already done the hard work in computing the 13GB database of hashes and filenames, but we also baked that database generation into the tool itself, in case you ever want to rebuild it yourself. Unlike other vendors in the Attack Surface Management space, we continue to push our tradecraft further and share our proprietary tooling with the world, for free.”
– Shubham Shah, SVP Engineering & Research, Searchlight Cyber
You can read the full technical write-up on the Security Research blog.
Addressing the challenge of scouring vendor code
Developed by Searchlight’s security research team, Hyoketsu was created to use in our own investigations to solve the challenge of manually scouring thousands of vendor code files across major enterprise applications. Hyoketsu automatically filters out vendor code that doesn’t contribute to the exposed attack surface of an application, cross-referencing against a database of known filenames and hashes, allowing researchers to focus only on the custom code that could contain security issues.
Where to access Hyoketsu
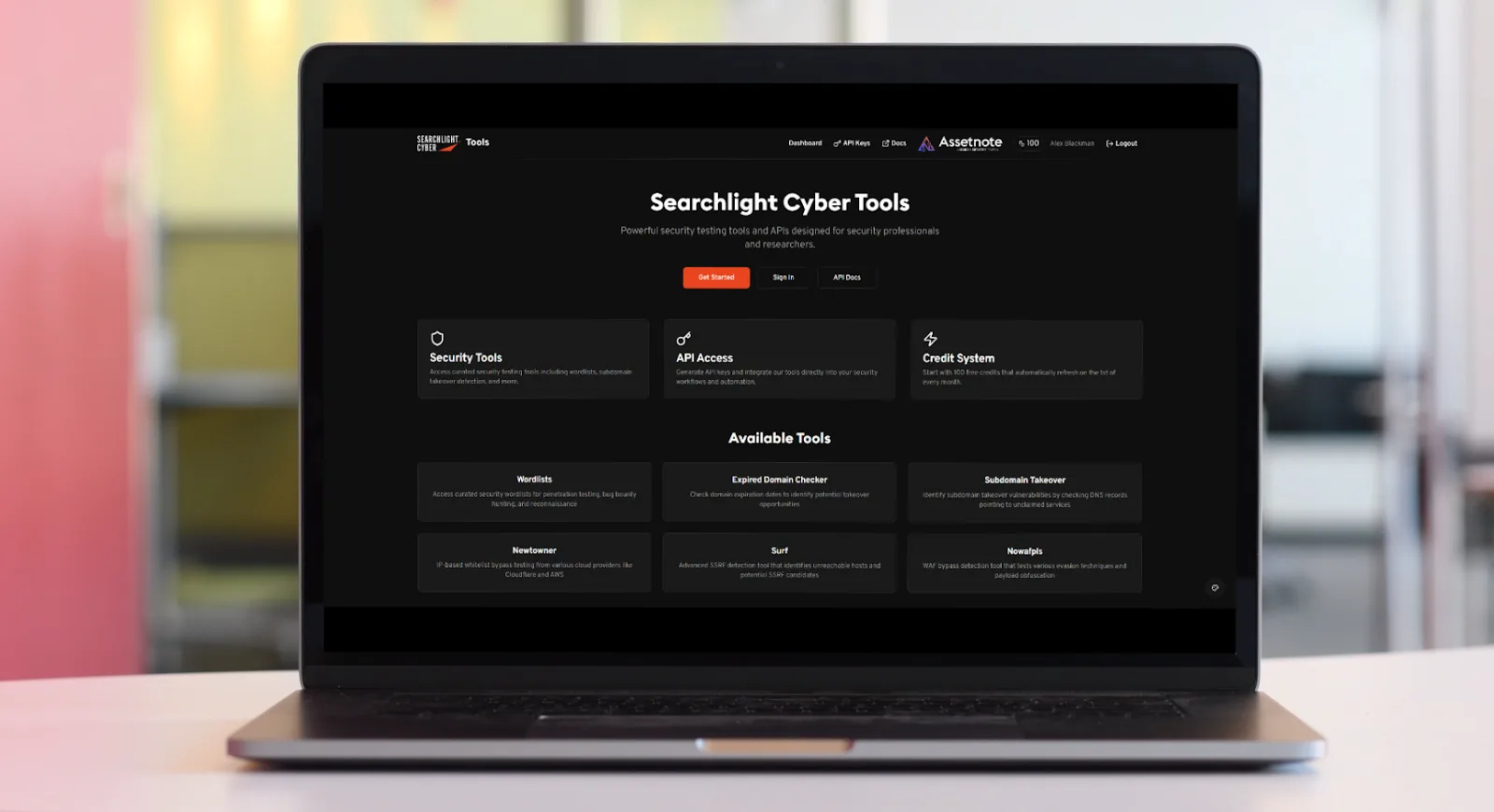
Hyoketsu is available to security professionals on the Searchlight Cyber Tools Site, in the Open Source Tools section, alongside a multitude of other publicly available offensive security resources, including Wordlists, Newtowner, and Surf (free registration required). Alternatively, you can also access the tool via our GitHub repo: https://github.com/assetnote/hyoketsu
Visit our solution page to learn more about our ASM platform or book a demo today.
Bio
Alex Blackman is the Head of Product Marketing at Searchlight Cyber, where he leads the go-to-market strategy for the company’s Preemptive Threat Exposure Management suite. With over a decade of experience serving global brands like Unilever and Allianz, Alex focuses on bridging the gap between deep technical intelligence and strategic business value. He is the voice behind Searchlight’s webinar series, helping MSSPs, enterprises, and public sector organizations identify threats before they become attacks.