CVE threat intelligence context, exploitation data, and history all embedded into Searchlight’s ASM to support analysts with faster response.
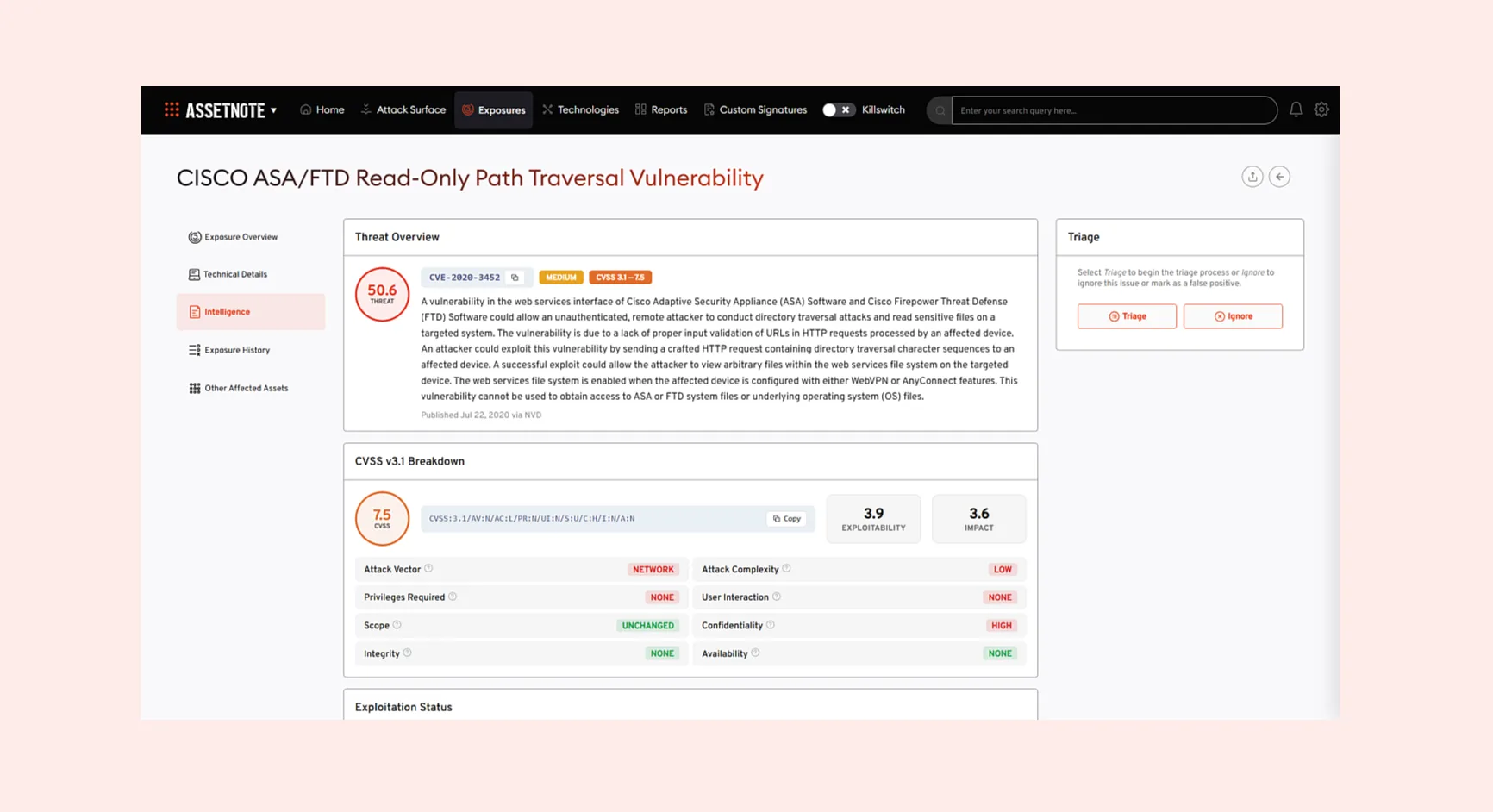
Searchlight’s Attack Surface Management platform has been updated with a new Intelligence tab on the Exposure detail page. Now, when an exposure is linked to a CVE, users can find the relevant threat context in the Intelligence tab, without having to leave the platform.
From the new tab, analysts can access detailed CVE data on the severity, exploitability, and real-world impact of an exposure.
Threat context and scoring
- Advisories – Microsoft MSRC advisories with KB articles and fixed builds, alongside GitHub advisories and ENISA/EUVD entries
- Affected Products – vendor and product breakdown with version ranges extracted from CPE data
- CVSS v3.1 Breakdown – full metric-by-metric breakdown including exploitability and impact scores
- Threat Overview – CVE description, threat score, and CVSS severity rating
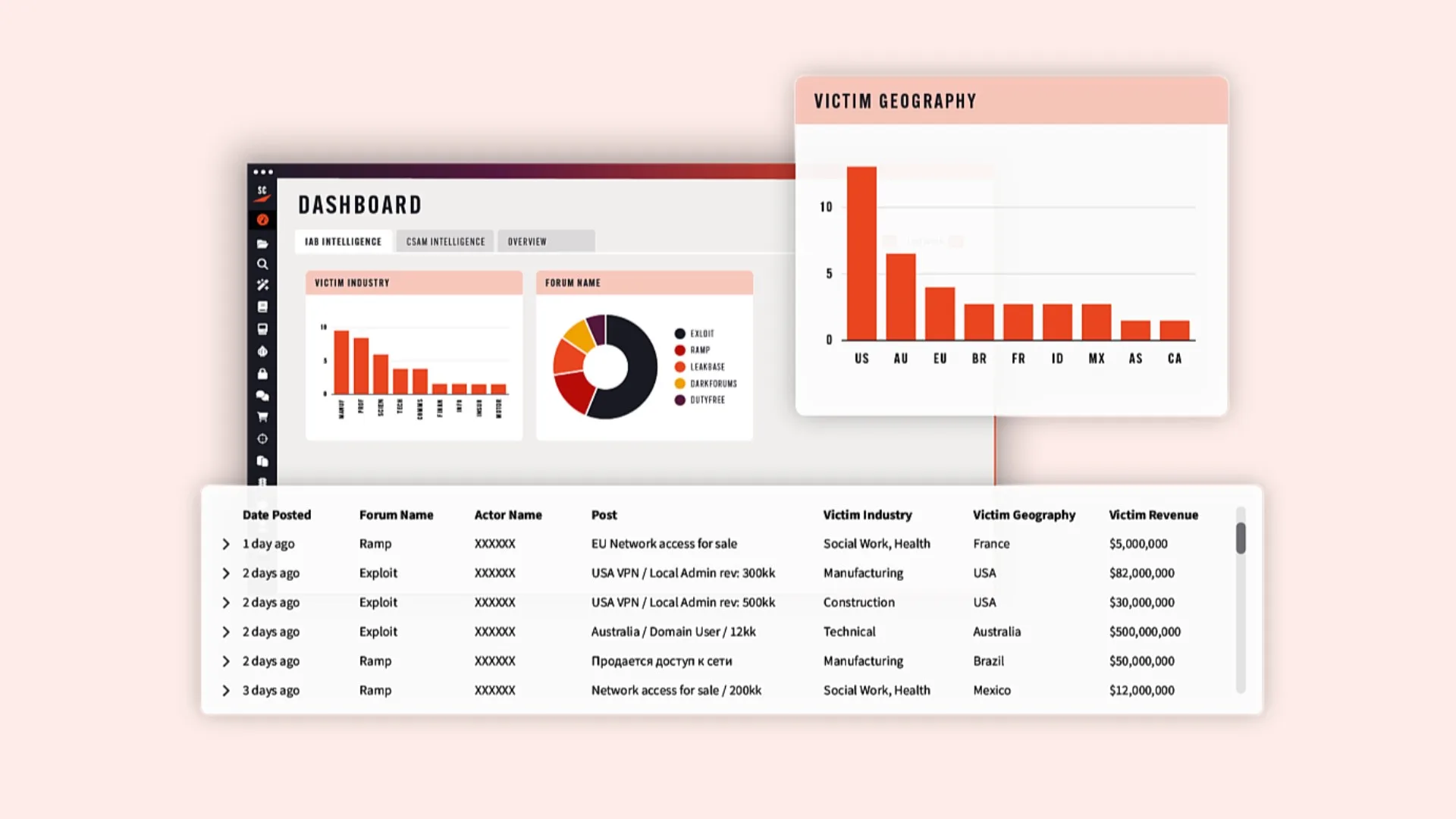
Exploitation and detection
- Detection Templates – scanning templates, Sigma rules, and YARA rules with severity scores, author attribution, and direct links
- Exploitation Status – EPSS exploit probability with percentile ranking, CISA KEV catalog status, known ransomware campaign associations, and public exploit availability
Bio
Alex Blackman is the Head of Product Marketing at Searchlight Cyber, where he leads the go-to-market strategy for the company’s Preemptive Threat Exposure Management suite. With over a decade of experience serving global brands like Unilever and Allianz, Alex focuses on bridging the gap between deep technical intelligence and strategic business value. He is the voice behind Searchlight’s webinar series, helping MSSPs, enterprises, and public sector organizations identify threats before they become attacks.