This week’s cybersecurity and dark web news stories discuss A Threat actor leveraging generative AI services, the 0APT bluff campaign, and the cyberattack on Deutsche Bahn.
AI-Augmented Threat Actor Compromises 600+ FortiGate Devices
A recent investigation by Amazon Threat Intelligence revealed a Russian-speaking, financially motivated threat actor leveraging multiple commercial generative AI services to compromise over 600 FortiGate devices across more than 55 countries between January 11 and February 18, 2026.
This campaign did not rely on exploiting FortiGate vulnerabilities. Instead, the actor succeeded by exploiting basic security gaps – exposed management ports and weak credentials with single-factor authentication – that AI helped them find and exploit at scale.
This activity highlights how commercial AI services are significantly lowering the technical barrier for offensive cyber capabilities. The actor, assessed as having low-to-medium baseline technical skills, used AI augmentation to achieve an operational scale that would typically require a larger, more skilled team.
AI was used extensively for:
- Initial Access: Systematic scanning for exposed FortiGate management interfaces and mass credential abuse.
- Tool Development: Generating custom scripts for parsing stolen FortiGate configurations, credential extraction, and automating reconnaissance.
- Attack Planning: Creating comprehensive, step-by-step exploitation instructions and prioritized task trees.
The actor’s post-exploitation activities included compromising Active Directory environments, extracting complete credential databases, and specifically targeting Veeam Backup & Replication servers – a potential precursor to a ransomware attack.
Notably, the threat actor demonstrated limited technical depth. When they encountered hardened environments, they simply moved on to softer targets, confirming their advantage lies in AI-augmented efficiency and scale, not in deep technical skill or creative problem-solving during live operations.
0APT Ransomware: Bluff Campaign Reveals Real, Functioning Threat
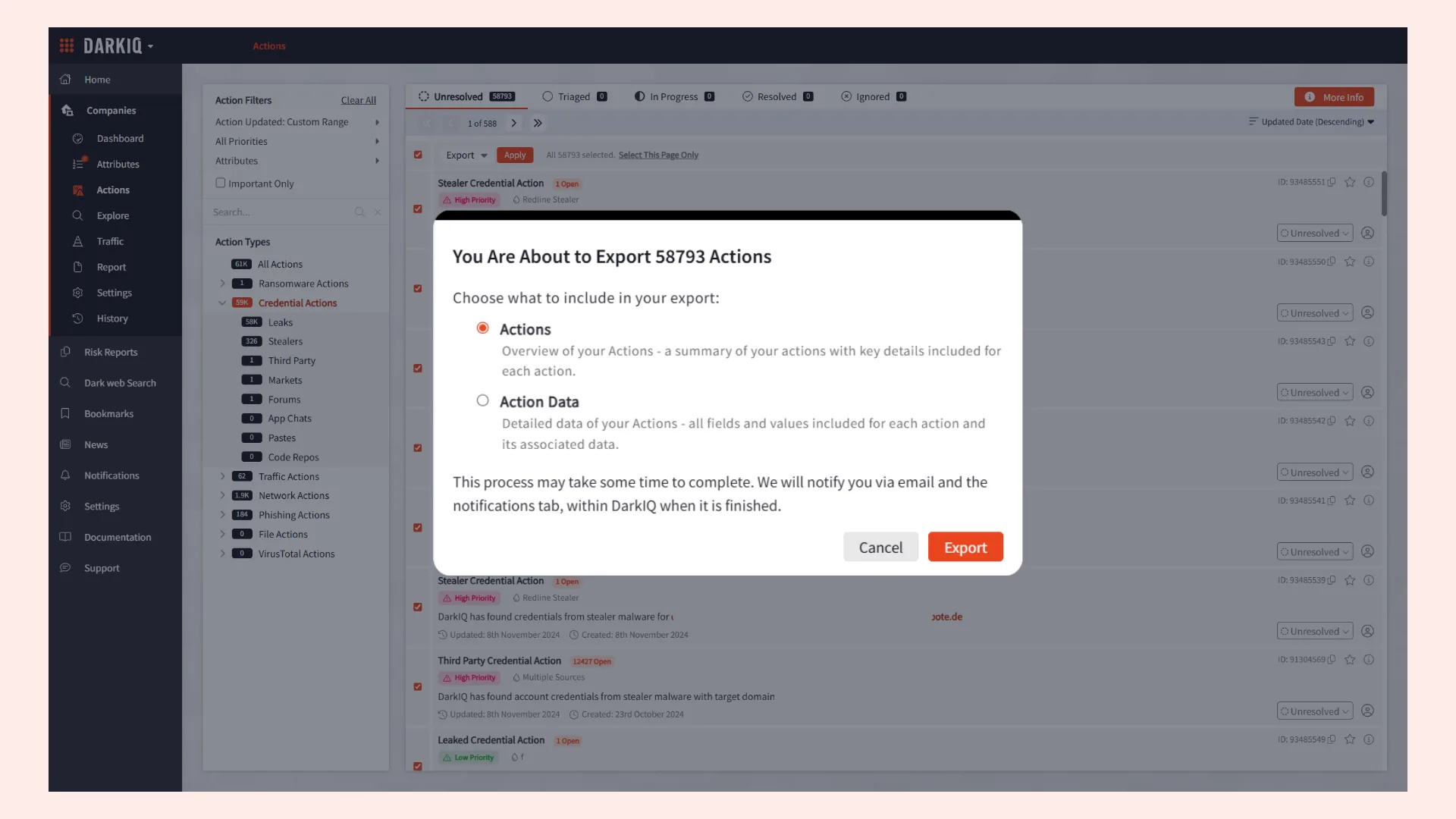
The 0APT campaign began with aggressive public claims of compromising over 200 organizations, but initial analysis by the Howler Cell Threat Research Team found no verifiable evidence of intrusions. The group’s onion-based data leak site eventually went offline, and attempts to download the advertised “oversized GB’s” of data failed to complete, suggesting the leaks were a staged bluff to create the impression of large-scale theft and damage.
The early bluff, while damaging to their credibility, was a distraction from their genuine, evolving capability. Investigation confirms:
Active RaaS Platform: 0APT is running a fully operational Ransomware-as-a-Service platform with a working affiliate model.
Viable Malware: Reverse engineering of generated ransomware samples showed the Rust-based malware is “operationally viable,” featuring a focus on reliability, strong cryptography, and customized builds for each affiliate.
Attack Profile: The malware lacks advanced features like network propagation, suggesting it is currently intended for targeted, manually controlled intrusions where the operator has already gained initial access.
Linguistic Clue: Embedded Hindi language strings were found in the debug logs, suggesting a possible Indian linguistic influence associated with at least one developer (though this is not definitive attribution).
Though the initial victim claims were inflated, 0APT is now clearly moving to establish a legitimate cybercriminal operation. Continued monitoring is recommended, especially for the introduction of features that enable persistence or automated network spread.
German Rail Hit by Major Cyberattack
Deutsche Bahn (DB), Germany’s national rail operator, confirmed a “considerable” distributed denial of service (DDoS) attack this week, which severely disrupted its digital ticketing and information services.
The DDoS attack, which effectively bombarded DB’s IT systems and caused outages on its website and Navigator app, occurred in waves starting midday Tuesday. While the company implemented defensive measures and reported largely stable systems by Wednesday morning, the incident underscores the heightened risk to Germany’s transport infrastructure.
DB has declined to comment on the attack’s origin, stating its top priority is protecting customer data and maintaining system availability.
The cyberattack follows warnings from German security agencies that transport infrastructure is a prime target for threats, including those potentially linked to Russia.
This latest digital attack adds to a recent pattern of security issues. Last year, DB reported “nearly-daily attacks,” including physical sabotage of crucial rail lines between major cities like Hamburg/Berlin and Cologne/Düsseldorf. These physical acts, which involved cut cables and the detonation of an explosive, led lawmakers and investigators to openly question a possible link to Russia.