Thank you for joining us at
Get instant access to our most read content
Searchlight is used by some of the world’s largest enterprises, government and law enforcement agencies, and the MSSPs at the forefront of protecting customers from external threats. Click below to read expert resources. You can also contact us if you need anything else.
Ransomware’s Record Year: H2 2025
Ransomware Groups Claimed Record Number of Victims in 2025, while the Number of Ransomware Groups Reached All-Time Highs.
Sign up to Beacon
Get the latest Cybersecurity news, insights, and intelligence straight to your inbox
ASM in the age of CTEM
This ebook is essential for security practitioners and anyone responsible for protecting digital assets.
Partner Success Brochure
Unlock best-in-breed attack surface management, dark web intelligence, and proactive security research your clients deserve.
Infostealer Identified
A real life example of an infostealer infection in an international professional services firm to demonstrate how this malware can be overcome with dark web monitoring.
Government Agency Targeted on the Dark Web
This use case looks at how dark web intelligence was used by the government agency to remediate the vulnerability before it was exploited – effectively stopping the attack before it could begin.
NCC Group Partners for Dark Web Intelligence
NCC Group has been a Searchlight Cyber partner for more than four years, utilizing its dark web intelligence and monitoring for its global customer base.
Technology Company Secures Attack Surface and Prioritizes Exposures
With Searchlight Cyber’s ASM solution, this technology company can prioritize exposures and preemptively tackle threats without being overwhelmed by noise
With Searchlight, you can gain the upper hand on bad actors and stay ahead of external threats.
Your visible surface
Everything beyond it
// Attack Surface Management
The only ASM that scans and validates exposures across your entire attack surface every hour – backed by expert researchers who uncover vulnerabilities in the third-party tools your teams rely on. The ones legacy vendors can’t reach.
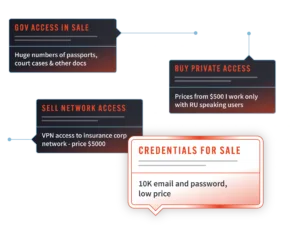
// Pre-attack Monitoring
Monitor for indicators of future compromise before they become breaches – infostealer-infected devices, leaked credentials, phishing infrastructure, and dark web chatter that signals your organization is in an attacker’s sights.
// Cyber Investigations
Give your team the investigative edge that 475 billion recaptured dark web data points deliver. Track current and emerging threats across the clear, deep, and dark web – securely, and without exposing your identity – across both security and business-critical investigations.

// Risk quantification
Quantify cyber risk based on real-time attacker behavior – not assumptions. Benchmark your exposure against peers, and take action early enough to move the needle before the board asks why you didn’t.
Searchlight Cyber was founded in 2017 with a mission to stop criminals from acting with impunity.