On March 11, 2026, Stryker Corporation, a $25bn global medical technology company, suffered one of the most operationally destructive cyberattacks in healthcare history.
An Iran-linked hacktivist group named Handala took responsibility, citing geopolitical retaliation as their motive. The attack remotely wiped more than 200,000 devices across 79 countries. 50 terabytes of data were exfiltrated. Operations shut down globally.
Could this state-aligned attack have been foreseen and possibly prevented?
In this post, we look at how the attack unfolded, what observed attacker behavior tells us about Stryker’s breach risk in the months leading up to the attack, and what security and risk teams can do to preempt and prevent similar attacks.
What we know about the attack
The Stryker breach is significant not because of its technical sophistication, but because of its apparent simplicity. Based on public reporting in March 2026, the attack appears to have unfolded in three stages:
- Initial access: Attackers authenticated into Stryker’s Microsoft Entra ID environment, with access believed to have been established well before the destructive phase. Check Point Research documented hundreds of logon and brute-force attempts against Stryker’s VPN infrastructure in the months preceding the attack, linked to Handala-associated infrastructure.
- Lateral movement: Once inside Entra ID, the attackers pivoted into Microsoft Intune, Stryker’s Mobile Device Management (MDM) platform, giving them the ability to issue commands to every enrolled endpoint globally. Early investigations suggested a pure “living off the land” attack using only Intune’s built‑in wipe functionality and no malware. However, Stryker has since disclosed that a malicious file was identified during its investigation, indicating that some malware was involved in the operation, even though the destructive effect still appears to have been delivered primarily through legitimate MDM capabilities rather than traditional ransomware or widespread wiper deployment.
- Impact: A mass remote wipe was issued against Windows devices connected to Stryker’s environment, erasing tens of thousands of laptops and mobile devices and disrupting operations in 79 countries.
A Note on Initial Access
It is important to be clear: the precise initial access vector has not been publicly confirmed with certainty. However, a plausible theory as of the drafting of this blog is that compromised credentials, likely sourced from months-old infostealer malware logs and the dark web, could have been used to gain entry.
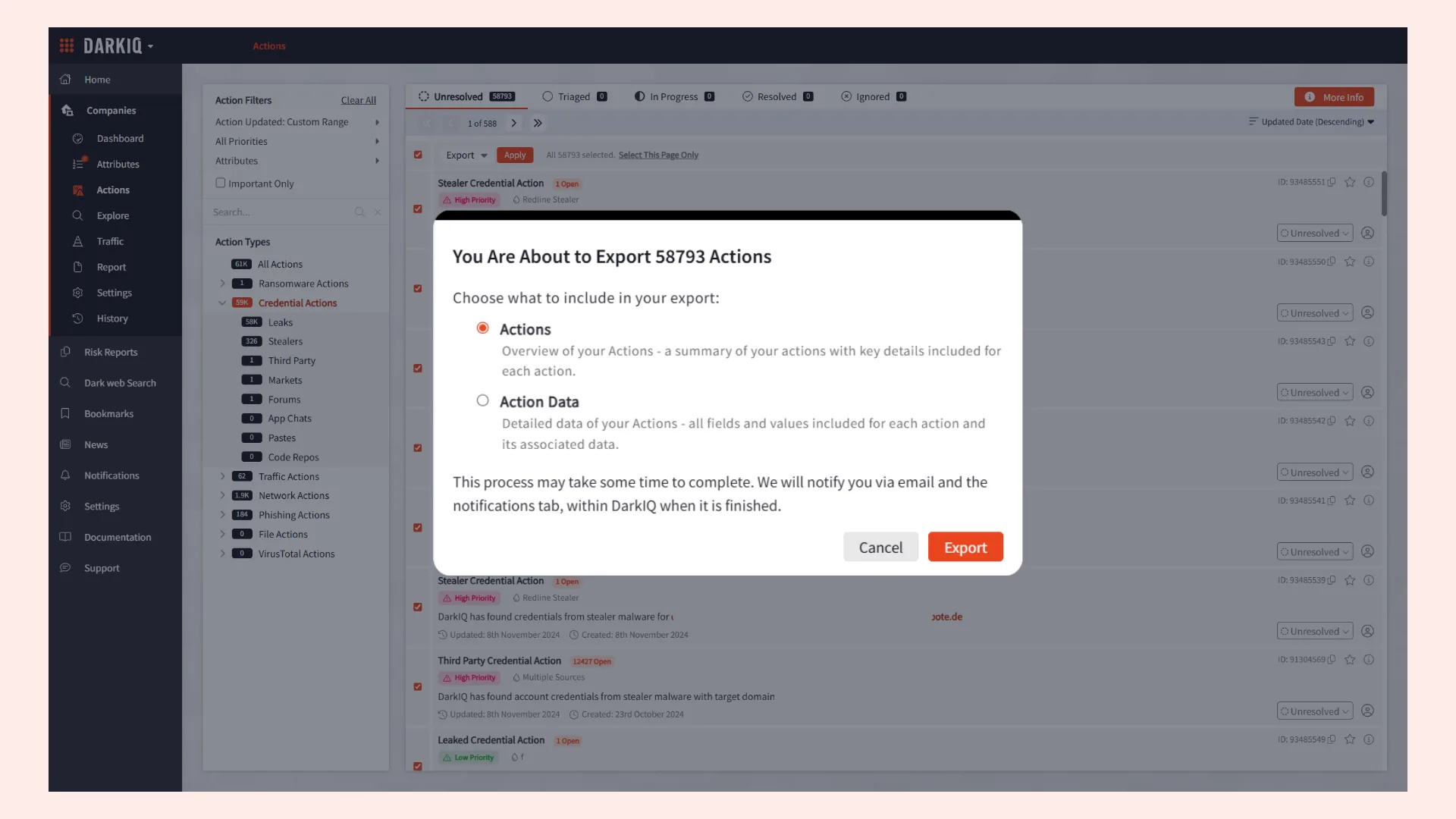
Searchlight Cyber’s infostealer log data, shown in the screenshots below, shows that credentials for admindev@stryker.com and adminqa@stryker.com were compromised across multiple stealer log leaks as far back as mid 2024. Notably, we observed the reuse of weak passwords across both of the email addresses and other accounts, increasing the likelihood that these breached credentials could have been used on Stryker systems and acted as an entry point for threat actors.
Source: Evidence of credential compromise identified in Searchlight’s investigation platform, Cerberus
What the Data Shows:
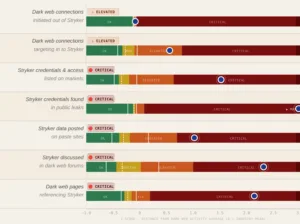
Searchlight Cyber’s Intangic platform tracks observable attacker behavior; units of activity on the dark web directed at or surrounding a target, across seven distinct signal categories. In the 12 months before the Stryker breach, the platform ranked the company in the riskiest top ~10% of peers: the “High Risk” tier of our risk ranking. A deeper look into the specific factors behind the rank showed the five Critical-rated signals and two Elevated signals.
Stryker’s credential-in-public-leaks signal is particularly significant, as it was higher than any other comparable company in the cohort, and this was the single signal most directly correlated with the theorized attack vector.
This overall “High Risk” tier rank is one of five we use to help customers differentiate their risk levels between companies of similar size and sector. The ranks are derived from the volume and combination of attacker-behavior signals. We then validate these risk ranks against breaches to ensure the companies placed in higher the risk ranks correlate with the companies that experience more frequent breaches. Our recent frequency study of breaches across approximately 6,000 publicly listed companies found that those in the High Risk tier are approximately 8x more likely to suffer a material breach than Low Risk peers in the subsequent 90-day window.
Stryker occupied this tier continuously for 12 months before the breach.
What does this mean? It means that the early warning signs of an attack were visible months in advance, and the categorization of Stryker as significantly higher risk of breach relative to peers, was accurate.
What Can Security and Risk Teams Learn from Stryker’s Case?
The Stryker breach, and the signals that preceded it, point to several concrete actions that security teams should be taking, regardless of industry or size.
- Monitor credential exposure as an ongoing process: Infostealer logs and dark web markets are updated continuously. A credential that appears clean today may be listed tomorrow: you need continuous visibility into whether your accounts are circulating in attacker communities.
- Treat old leaked credentials as potential threats: Credentials from breaches and infostealer dumps that are months or years old could still be actively weaponised. If an account appears in historical data, it could still represent an active threat and proactive action should be taken.
- Assume password reuse until proven otherwise: If credentials for any account appear in infostealer logs, assume that password has been reused across other services, including business-critical systems. Cross-reference against active accounts and enforce rotation immediately.
- Protect your MDM and identity infrastructure as crown jewels: Platforms like Microsoft Intune, Microsoft Entra ID, and similar endpoint management tools represent enormous leverage for an attacker. Compromise of one privileged account with access to your MDM can have immediate and catastrophic impacts. These platforms warrant their own specific access controls, MFA enforcement, conditional access policies, and anomaly monitoring.
- Ask whether your risk scoring reflects attacker intent: If your organization’s cyber risk posture is assessed purely through firmographic measurements, you may be missing the most important signals entirely. Visibility into real attacker behavior provides early warning and far more accurate breach prediction than traditional industry-standard methods.
For insurance carriers and managed service providers, this visibility and forewarning is a critical opportunity to identify when a customer is at high or critical risk, alert them, and take further action.
The Stryker breach illustrates what’s at stake when the signals are there but go unacted upon. While we may not know for sure whether leaked credentials served as the initial access vector, the fact that Stryker’s credentials were circulating, while the company was simultaneously being discussed and probed by threat actors, represented a material, measurable risk that warranted urgent action. Without visibility into these external threat signals, organizations may be operating with an inaccurate view of the true risk facing them, and miss a critical opportunity to stop a major breach before it happens.