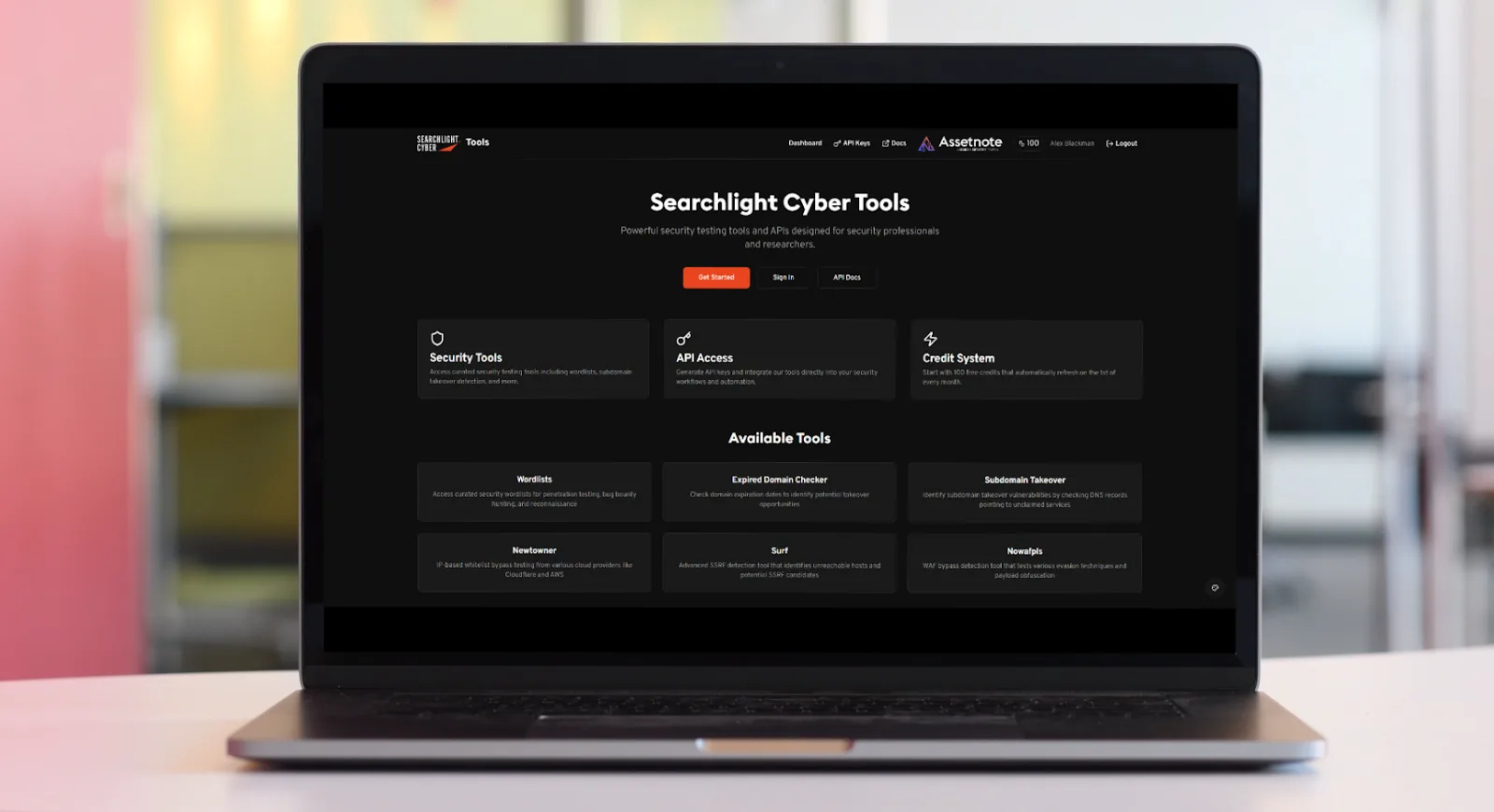

The Searchlight advantage
As time-to-exploit for vulnerabilities and leaked credentials continues to shrink, it’s more important than ever that security teams have complete visibility of their attack surface – covering internal, external, and hidden assets. Searchlight continuously identifies and prioritizes critical exposures, helping teams remediate risk and prevent attacks before they escalate.
A unified platform for preemptive security
From attack surface management to dark web monitoring and investigations.
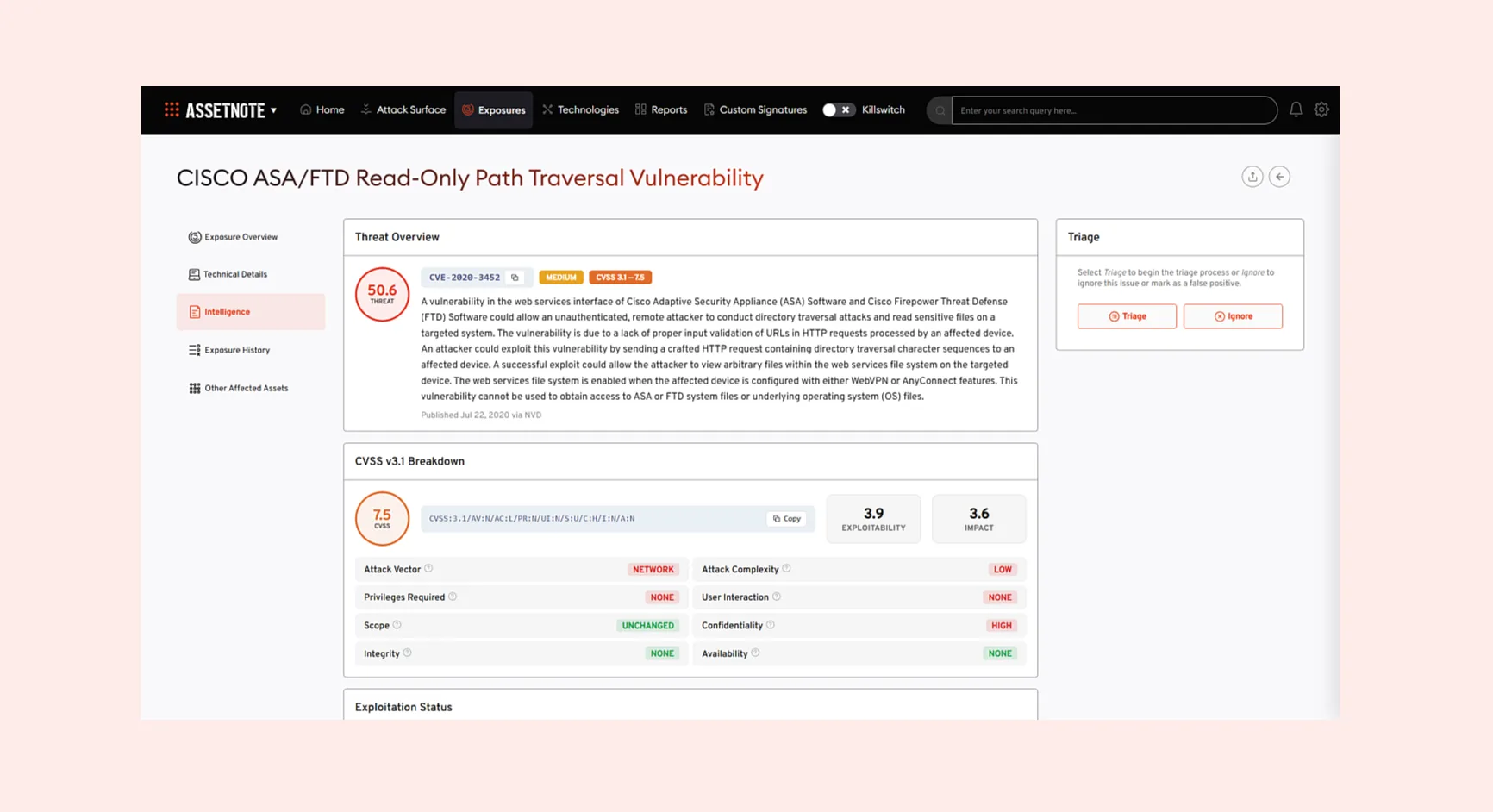
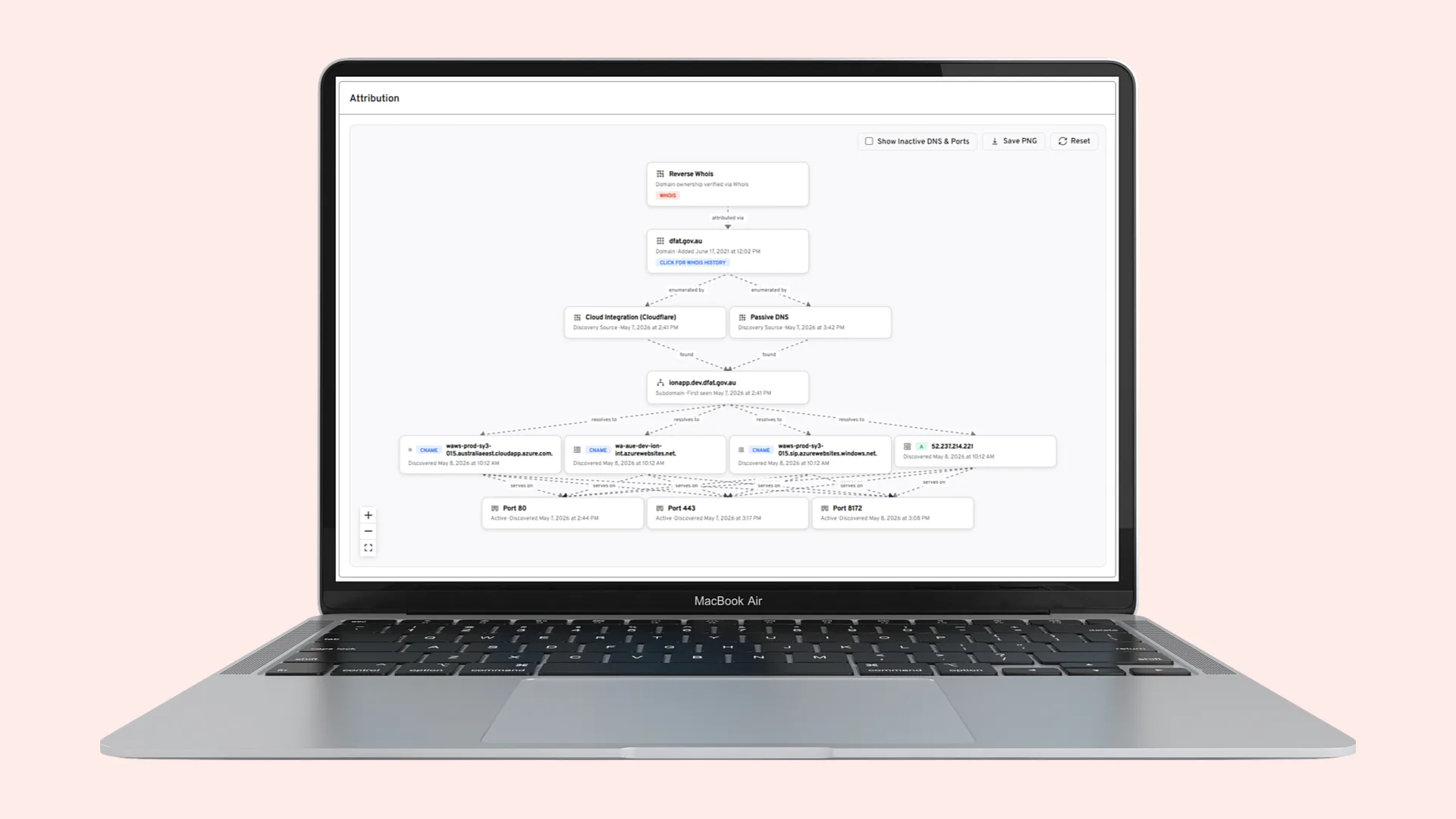
Assetnote
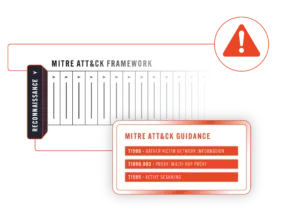
Attack Surface Management
Assetnote continuously maps and monitors your external attack surface, delivering hyper-personalized, actionable alerts without the noise – so your team can mitigate risks faster.
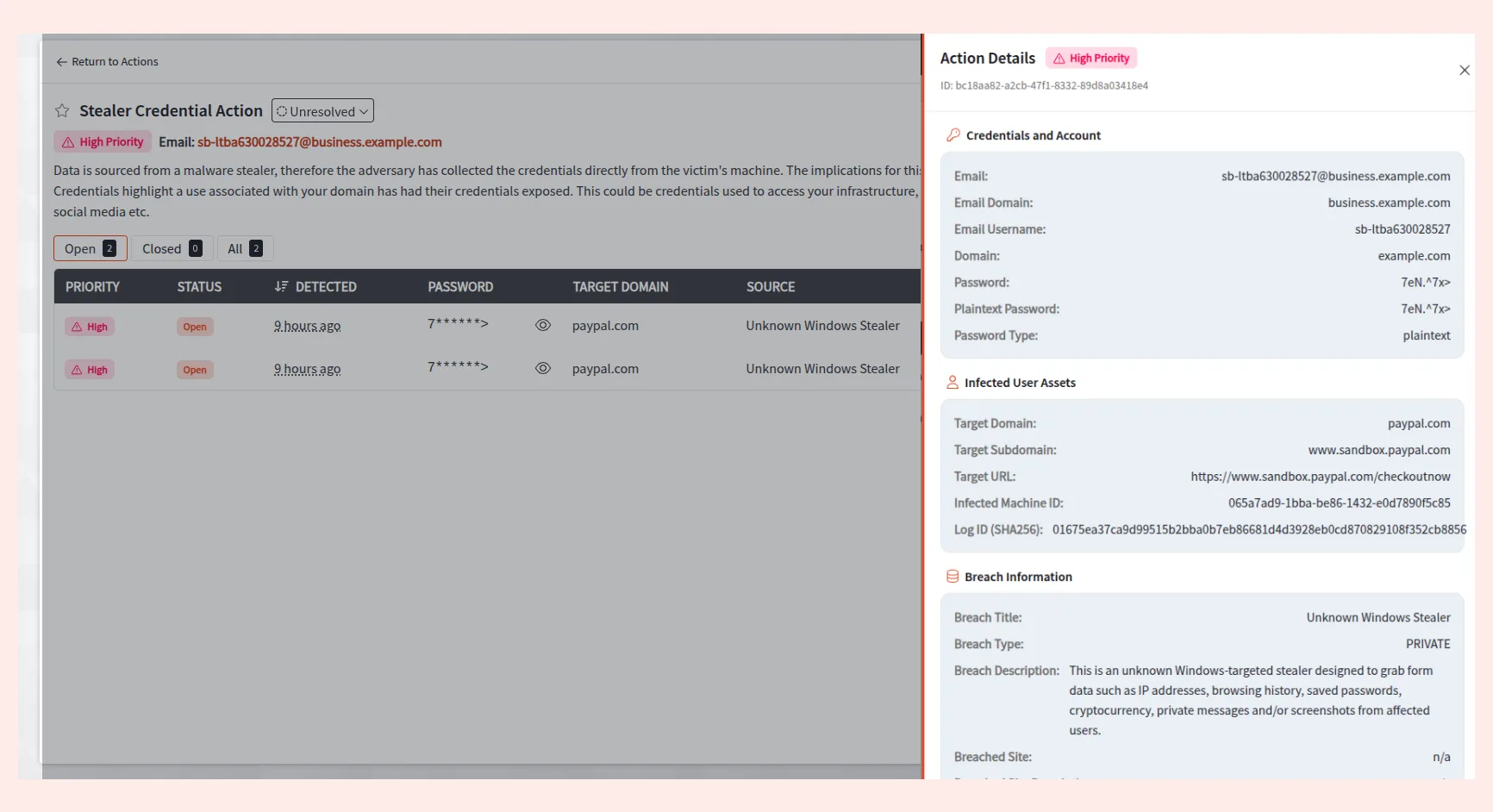
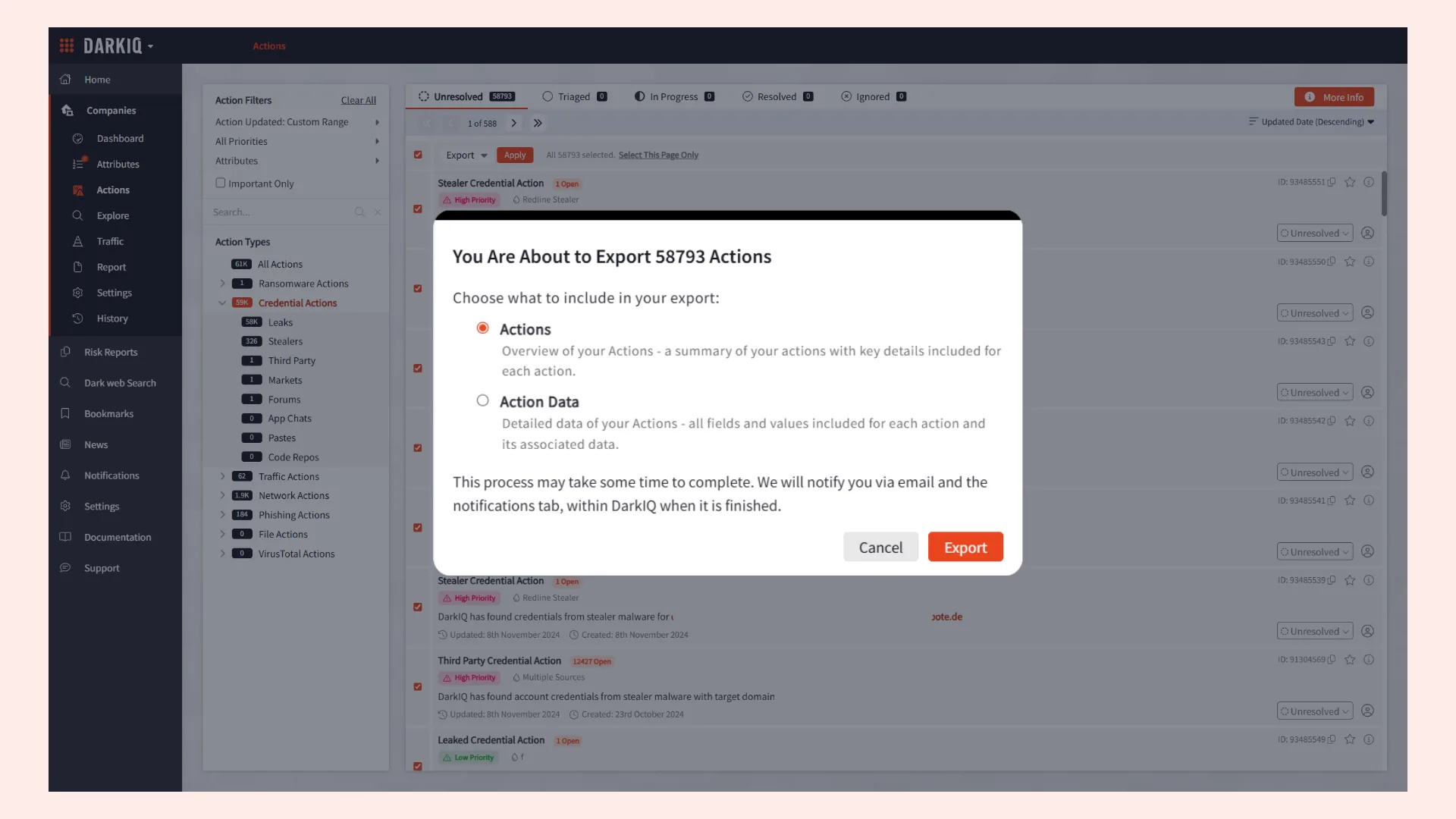
DarkIQ
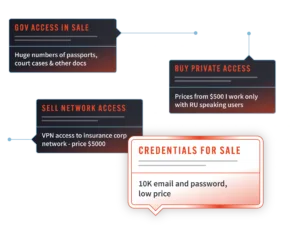
Dark web monitoring
Gain real-time visibility into adversaries targeting your personnel, sensitive data, and critical infrastructure on the dark web with DarkIQ’s dark web monitoring.
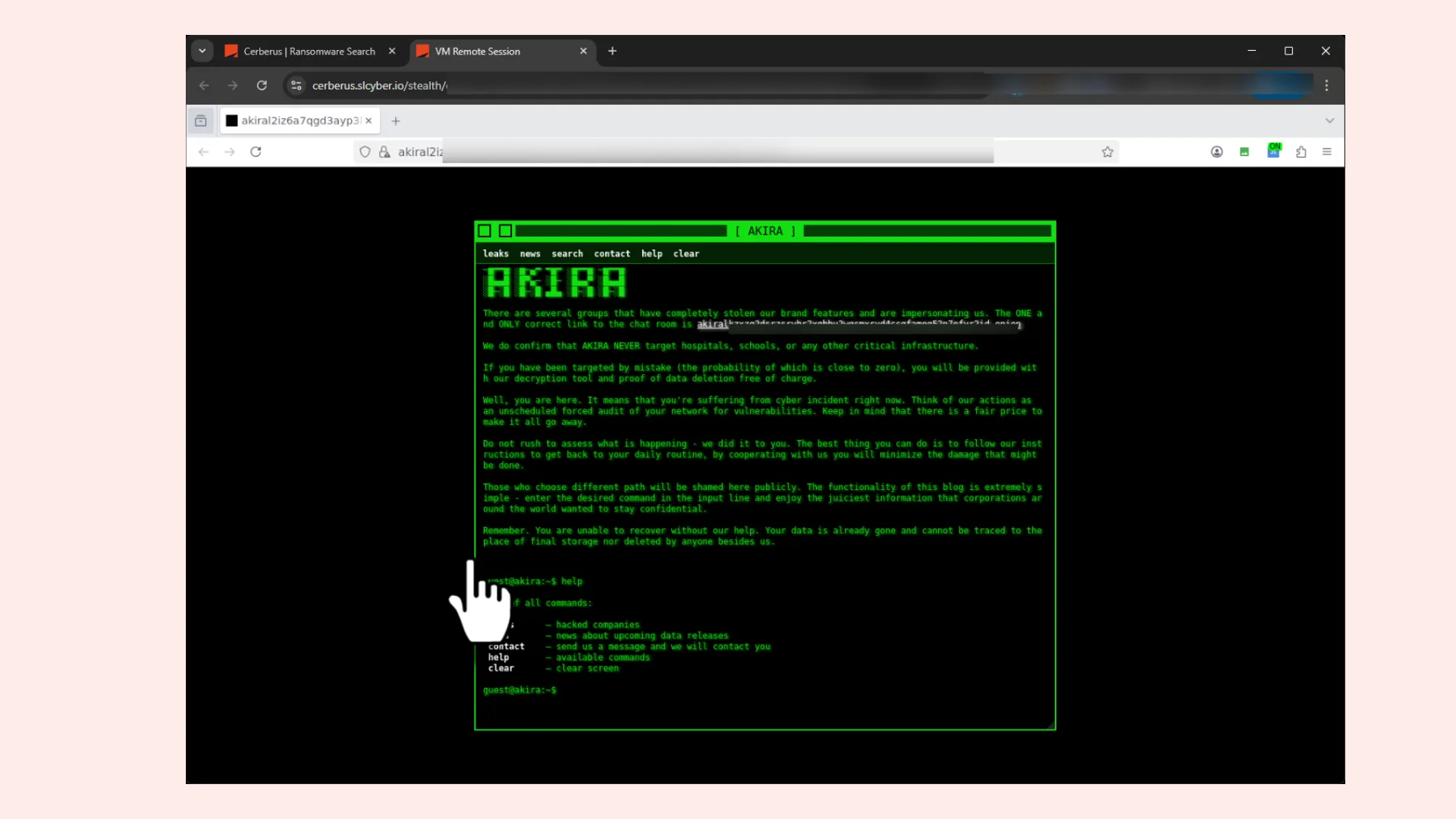
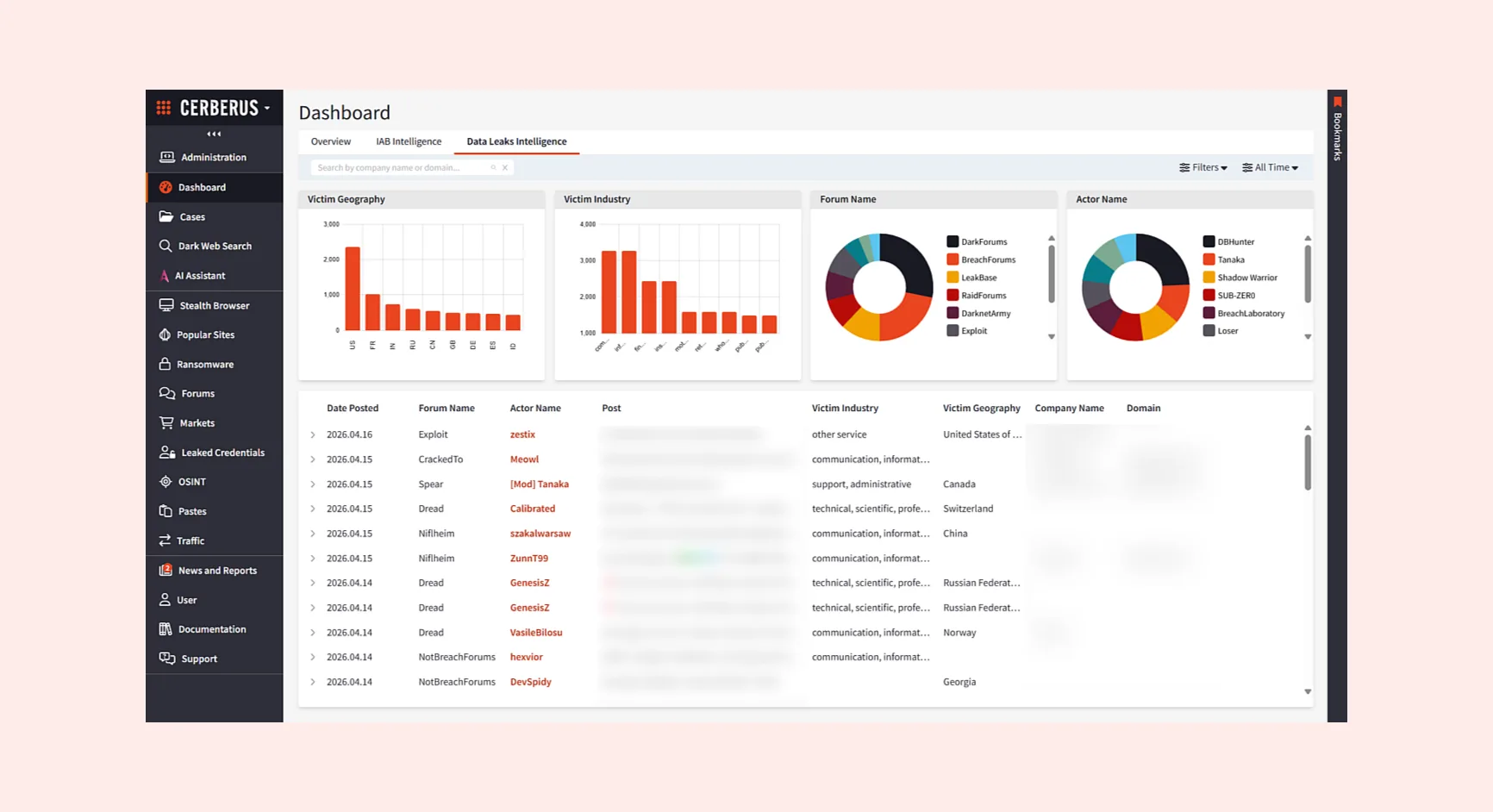
Cerberus
Dark web investigations
Securely investigate the dark web. Access live and archived intelligence to surface threats, collect evidence, and deliver measurable security and enforcement outcomes.

Intangic:
Quantify and prioritize cyber risk
Using Intangic, you can measure exposure based on real-time attacker behavior, benchmark your organization’s risk against peers, and take earlier action to demonstrably reduce risk.
Trusted by leading companies worldwide