In this blog we discuss why it’s critical for financial institutions to understand the threats they’re facing from the dark web and how early visibility using threat intelligence can help to preempt cyberattacks.
Financial institutions operate in one of the most targeted sectors by threat actors and ransomware gangs. From credential theft and account takeovers to ransomware and supply chain compromise, adversaries continuously adapt their tactics to exploit high value financial data. In this environment, traditional reactive security controls are no longer sufficient. Real-time dark web threat intelligence has become critical for enabling truly preemptive cybersecurity strategies.
For cybersecurity teams, the value of threat intelligence is not in raw data collection, it’s in contextualized, actionable insight that reduces dwell time, prioritizes risk, and enables disruption before impact.
The role of real-time threat intelligence
Threat intelligence, when collected in real time from dark web forums, encrypted messaging channels, underground marketplaces, and leak sites, provides early visibility into adversarial intent. Unlike surface-level monitoring or generic threat feeds, dark web intelligence exposes planning discussions, tool development, credential sales, and data monetization strategies long before attacks happen.
For financial institutions, this early warning translates directly into:
- Reduced fraud losses.
- Faster incident response.
- Improved risk modeling.
- Stronger regulatory compliance posture.
- More accurate threat actor attribution.
Rather than waiting for indicators of compromise (IOCs) to appear in logs, security teams can proactively identify when their organizations are being discussed or targeted.
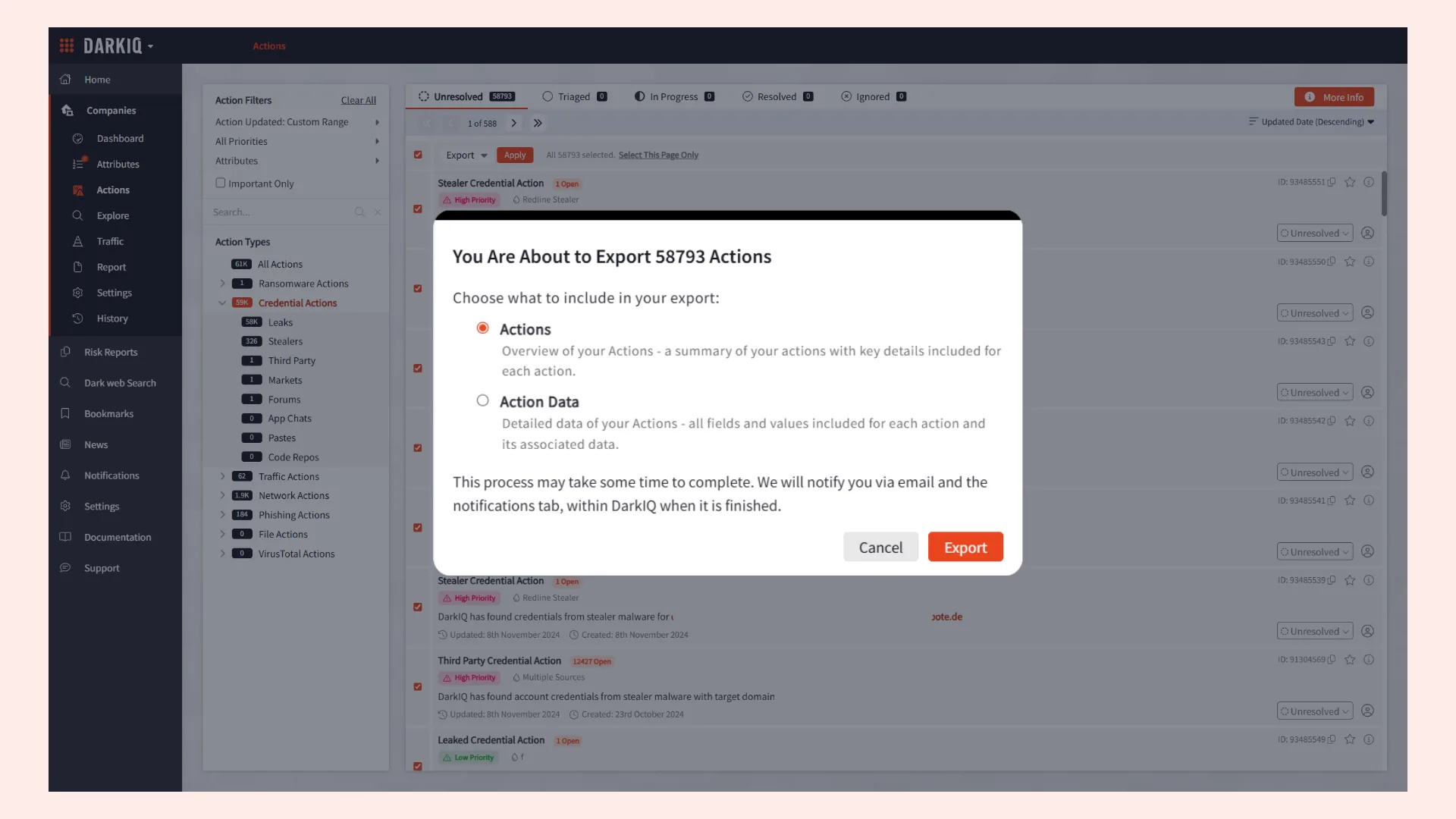
Early detection of stolen credentials and access
Credential-based attacks remain one of the most common entry points for financial fraud and network intrusion. Real-time dark web monitoring enables institutions to detect:
- Stolen employee credentials.
- Customer banking logins for sale.
- Session tokens and MFA bypass kits.
- Initial access broker listings.
When these artifacts surface, teams can initiate forced password resets, revoke tokens, trigger step-up authentication, or monitor affected accounts for suspicious behavior. This dramatically reduces the window between credential exposure and exploitation.
Disruption of fraud campaigns before scale
Financial institutions are frequent targets of email phishing, SMS phishing, and identity fraud services.
Real-time visibility into emerging tactics targeting a specific bank’s brand allows cybersecurity teams to:
- Preemptively block malicious domains.
- Notify customers before widespread phishing waves.
- Collaborate with takedown providers.
- Update fraud detection models.
This supports a preemptive cybersecurity posture detecting cyberattacks during the reconnaissance phase rather than after escalation.
Ransomware and extortion intelligence
Ransomware groups frequently advertise victims, sell stolen data, and recruit affiliates on dark web marketplaces. For financial institutions, real-time tracking of these ecosystems offers multiple advantages:
- Early warning if the institution or a third-party vendor is listed.
- Insight into tooling (e.g., new encryption strains or data exfiltration).
- Understanding of targeting patterns across regions and the wider financial industry.
Proactive monitoring also enables institutions to assess supply chain risk. If a core banking software provider or payment processor is discussed in underground forums, security teams can immediately evaluate exposure. This transforms threat intelligence from a reactive feed of malware hashes into important insights about adversary behavior.
Enhanced third-party and supply chain risk management
Financial ecosystems are deeply interconnected. Open banking APIs, fintech integrations, and outsourced service providers expand the attack surface beyond traditional perimeters.
Intelligence from the dark web can reveal:
- Data leaks from fintech partners.
- Compromised credentials tied to third-party vendors.
- Exploits circulating for specific financial platforms.
- Insider access being advertised for sale.
By identifying these signals, institutions can prioritize assessments and remediation activities based on active threat signals rather than static risk scoring alone.
This capability aligns directly with regulatory requirements around operational resilience and third-party oversight.
Acceleration of incident response and containment
Time is the most critical variable in cyber defense. The faster an organization detects exposure, the lower the potential loss.
Real-time dark web threat intelligence reduces mean time to detect (MTTD) by showing external indicators that internal reporting may not yet reveal. For example:
- Stolen database samples posted before extortion contact.
- Insider selling access prior to misuse.
- Customer data appearing in aggregated breach collections.
With early detection, incident response teams can:
- Conduct targeted forensic analysis.
- Activate customer notification workflows.
- Engage legal and compliance teams sooner.
- Coordinate with law enforcement where appropriate.
This shifts response from crisis management to controlled containment.
Strengthening Preemptive Cybersecurity Architecture
Preemptive cybersecurity is fundamentally about shifting upstream in the attack lifecycle and identifying and neutralizing risk before operational disruption. Real-time dark web intelligence strengthens this model by integrating predictive signals and defensive systems.
For financial institutions operating under strict regulatory scrutiny, this preemptive approach also demonstrates due diligence. Regulators increasingly expect institutions to understand not only internal vulnerabilities but also the external threat landscape targeting their sector.
Investing in dark web intelligence
Financial institutions that invest in dark web intelligence capabilities can start to outpace cybercriminals. By transforming dark web signals into actionable insight, it enables cybersecurity teams to anticipate, disrupt, and contain threats before they escalate.
In a sector where trust is currency and downtime carries consequences, threat intelligence is not a supplementary capability, but a critical part of preemptive cybersecurity strategy.