In this blog Luke Donovan, Head of Threat Intelligence discusses why ransomware defense starts by closing critical gaps long before an attack is launched.
Ransomware doesn’t begin with encryption, it begins with exposure. Long before a ransom note appears on screen and files are encrypted, ransomware gangs are scanning, investigating, and identifying vulnerable, misconfigured, or forgotten assets across an organization’s digital footprint. By the time an attack is executed, threat actors already have persistence, privileged access, and sensitive data ready for exfiltration.
In 2025 we saw victims reach an all time high, more than doubling year on year. Traditional approaches aren’t working, so stopping ransomware requires a shift in mindset. It means moving from reacting to incidents to preempting them, reducing exposure before attackers can exploit it. Organizations that get ahead of ransomware don’t just respond faster, they prevent attacks from escalating in the first place.
Why ransomware is no longer a point-in-time threat
Ransomware is often thought of as a single event where systems are encrypted, operations halted, ransom demanded. In reality, it is the final stage of a much longer lifecycle.
Modern ransomware groups operate like mature enterprises. Initial access brokers sell footholds, affiliates deploy payloads, and data theft precedes encryption to enable double extortion. In many cases, attackers dwell in environments for days or weeks before triggering the attack.
Organizations that only focus on backup and recovery planning are unfortunately fighting a losing battle. While resilience is critical, it does not address the multiple extortion methods ransomware groups employ, and does very little to address the exposure or vulnerability that allowed the attackers in.
Stopping ransomware requires visibility into the full attack chain, from reconnaissance and initial access to lateral movement and data exfiltration.
How do ransomware groups gain access?
Ransomware groups exploit the same weaknesses again and again. The difference is their scale, automation, and persistence.
Common access vectors include:
- Exposed remote access services.
- Unpatched vulnerabilities in internet-facing applications.
- Misconfigured cloud storage.
- Compromised credentials from phishing or infostealers.
- Third-party or supply chain access.
Attackers continuously scan the internet for exposed services and weak configuration. Sophisticated zero-days can prove devastating, but simple mismanaged assets provide a simpler route.
Crucially, many of these exposures exist outside the visibility of traditional security tools. Shadow IT, forgotten subdomains, test environments, or legacy systems often sit unmonitored – yet fully accessible to threat actors.
Understanding how ransomware groups gain entry means understanding your true attack surface, not just the assets you believe you own, but the ones attackers can see and exploit.
How organizations can get ahead
Getting ahead of ransomware is about shifting upstream in the attack lifecycle, addressing the exposure before it becomes exploitation.
This begins with comprehensive asset discovery. Organizations must identify every internet-facing asset, across subsidiaries, cloud environments, third parties, and remote infrastructure. If you don’t know it exists, you can’t secure it.
From there, continuous monitoring becomes critical because the attack surface isn’t static. New services are deployed, cloud configurations change, employees create new accounts, and vendors integrate systems on an hourly basis. Cybersecurity teams must operate at the same pace.
Proactive ransomware defense includes:
- Continuous attack surface monitoring.
- Quick remediation of exposed vulnerabilities.
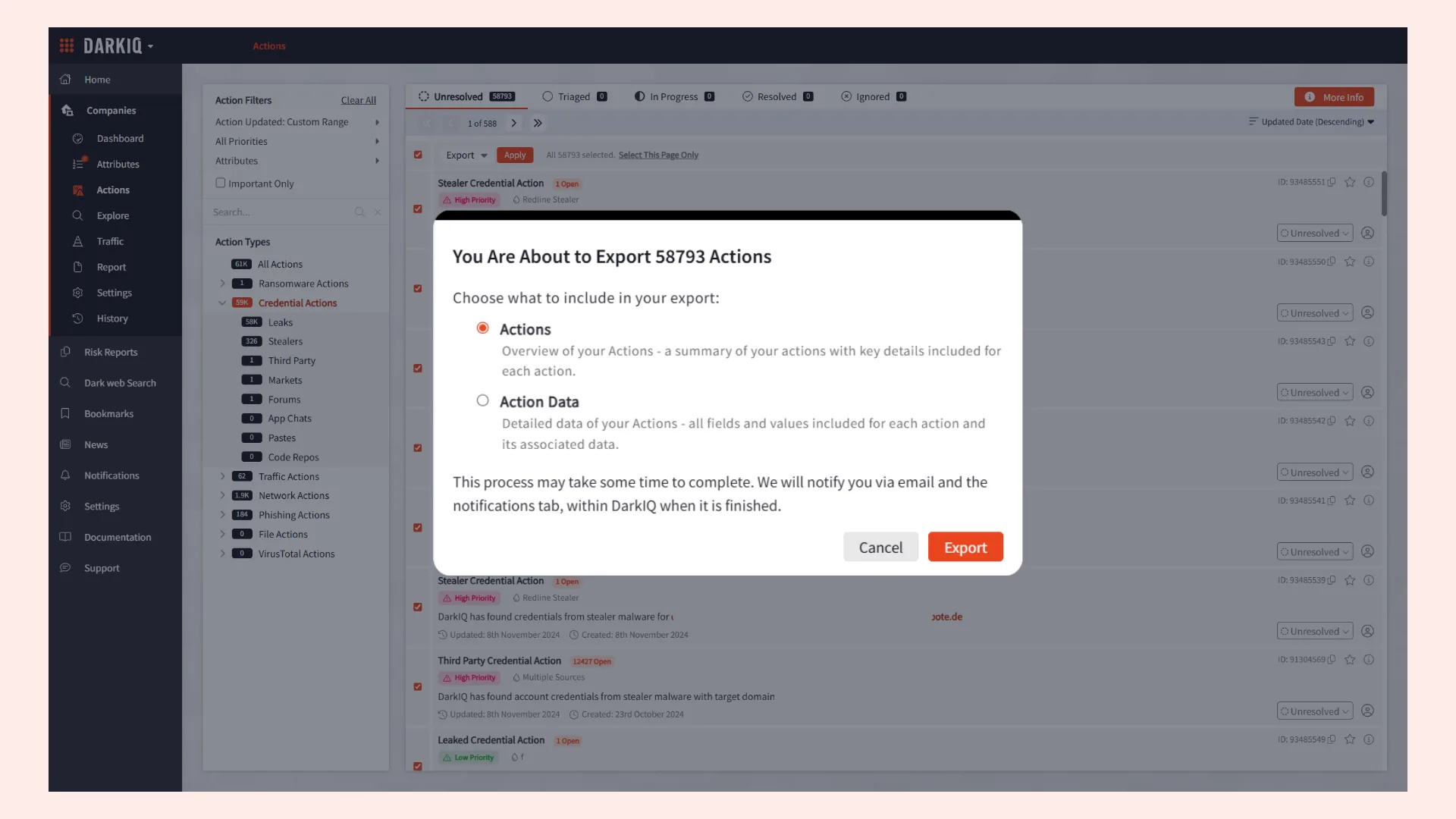
- Monitoring the dark web of exposed credentials.
- Threat intelligence to track active ransomware groups.
- Detection of early warning signs such as suspicious access patterns.
This approach reduces the window of opportunity for attackers. Instead of discovering an attack after encryption, organizations can detect and disrupt activity during reconnaissance or initial access.
The goal is not to just recover faster, it’s to prevent attackers from reaching the encryption stage at all.
Why Attack Surface Management is critical to ransomware prevention
Attack Surface Management (ASM) plays an important role in stopping ransomware.
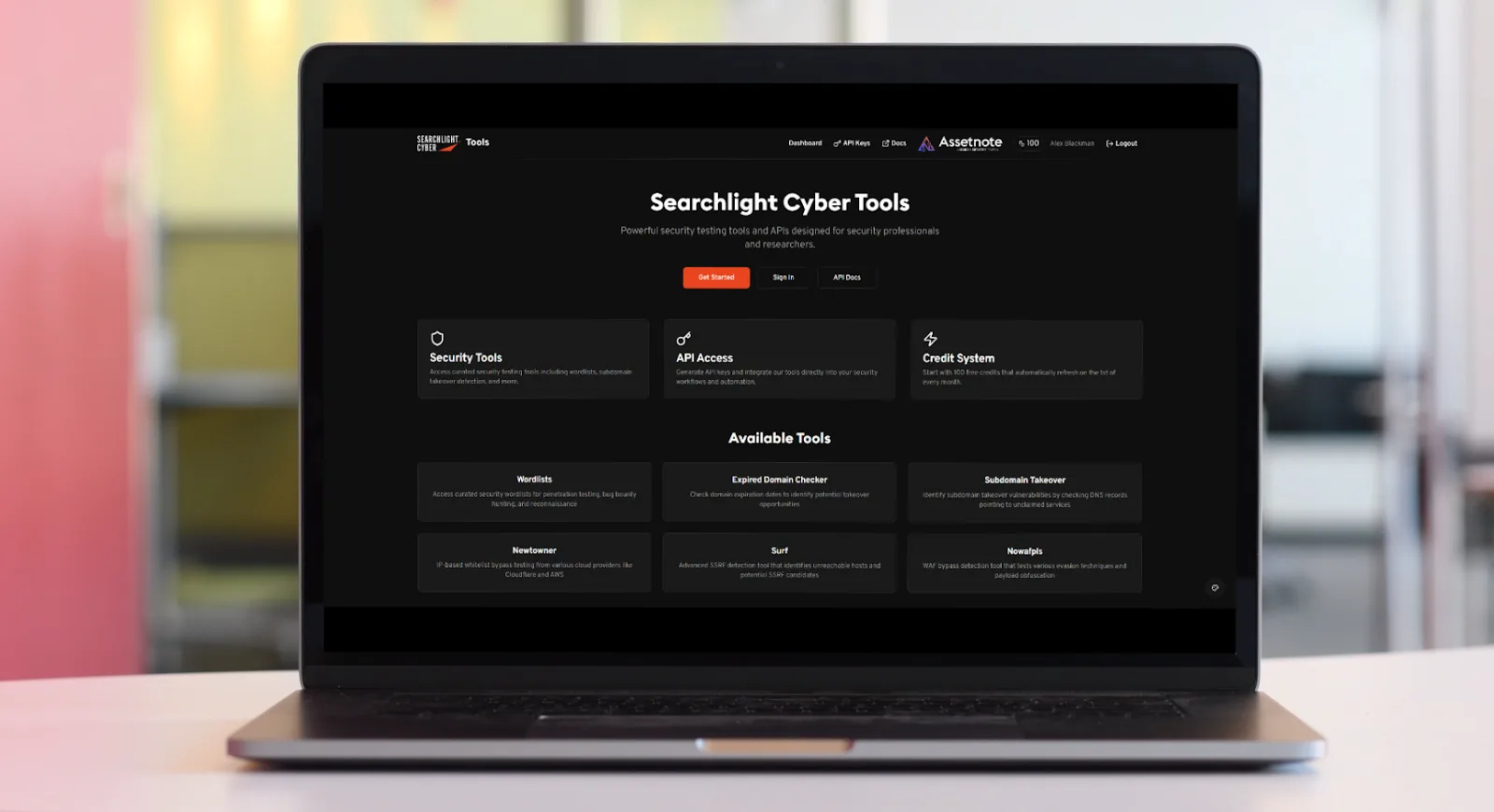
ASM provides an outside-in perspective, mirroring how attackers see your organization. It continuously discovers, maps, and monitors exposed assets and vulnerabilities across the external environment, addressing one of the primary drivers of ransomware success.
Without ASM, organizations rely on internal asset inventories that are often incomplete or outdated. Meanwhile, ransomware gangs rely on real-time scanning and automated reconnaissance.
Effective ASM enables organizations to:
- Identify misconfigured or exposed services before attackers do.
- Detect vulnerable software versions on internet-facing systems.
- Uncover shadow IT and forgotten infrastructure.
- Prioritize remediation based on exploitability and threat activity.
By shrinking the external attack surface, organizations reduce the number of potential entry points available to ransomware groups. Critically, ASM should not operate in isolation, but integrate with vulnerability management, threat intelligence, and incident response processes. When external exposure is contextualized with active threat actor behavior, organizations can prioritize the risks most likely to lead to ransomware incidents.
Prevention begins with visibility, which also begins with ASM.
Understanding ransomware TTPs
To stop ransomware, organizations must understand how ransomware groups operate. Threat actors operate in different ways, so value can be unlocked by understanding the tactics, techniques, and procedures (TTPs) they use.
One of the main takeaways from the report and the tactics employed by the most prolific ransomware groups, is the victimology. Victims continue to be sporadic, geographically diverse, and comprise both large multinationals and small businesses. We are not seeing any indication of ‘Big Game Hunting’, meaning that in theory, any and all organizations are a target. Ransomware groups are playing a numbers game at scale, automatically scanning for vulnerabilities in third party software and using AI to speed up their processes, weeding out the weakest defences.
Common ransomware TTPs can include:
- Scanning for exposed services and brute-forcing credentials.
- Exploiting known vulnerabilities shortly after public disclosure.
- Deploying commodity tools for lateral movement e.g. remote administration tools.
- Disabling security controls before encryption.
- Exfiltration of sensitive data.
- Leveraging double or triple extortion tactics.
Tracking these behaviors allows organizations to detect activity earlier in the attack chain.
For example monitoring credential leaks linked to corporate domains can reveal potential access before it’s weaponized. Observing ransomware groups targeting specific technologies or geographies enables proactive remediation of relevant vulnerabilities.
Threat intelligence transforms ransomware defense from reactive to an attack they can preempt. Instead of asking “What happened?” organizations can ask “What are attackers likely to do next?”
Why the best ransomware defense strategy is preemptive
The financial and operational impacts of ransomware are well known – downtime, reputational damage, regulatory scrutiny, and recovery costs that can actually extend beyond the ransom itself.
But the strategic impact is equally significant. Organizations that repeatedly respond to ransomware incidents remain trapped in a reactive cycle. Each attack takes up resources, diminishes trust, and exposes weaknesses. Proactive defense changes that dynamic.
By continuously identifying exposure, monitoring attack surfaces, and aligning defenses with real-world threat actor behavior, organizations can get a step ahead.
Importantly, preemptive ransomware defense is not about eliminating all risk, which is impossible. It’s about becoming a less attractive target by closing the door to easy entry points and detecting malicious activity before it escalates.
Ransomware will continue to evolve. Groups will rebrand, techniques will adapt, and new vulnerabilities will emerge. But the fundamentals remain – ransomware gangs exploit exposure. Stopping ransomware begins with finding, prioritizing and fixing that exposure first.