This week’s cybersecurity and dark web news stories discuss the seized domains associated with the Ministry of Iran, Crunchyroll data breach, and PureLog stealer malware targeting critical infrastructure.
U.S. Dismantles Iranian-Backed Cyber-Terror Network
The Department of Justice has seized four domains used by Iran’s Ministry of Intelligence and Security (MOIS) to conduct cyber-attacks, psychological operations, and transnational repression. The move targets a network responsible for doxing journalists, inciting violence against Jewish communities, and threatening dissidents on American soil.
At the center of the disruption are the domains associated with the “Handala Hack” persona. Investigators found these sites were used to leak sensitive data stolen from a U.S. medical firm and the Israeli Defense Force. Most disturbingly, the network used an Outlook email account to issue death threats against journalists, even claiming to offer $250,000 bounties to criminal cartels for the execution of regime critics.
“Terrorist propaganda online can incite real-world violence,” said Attorney General Pamela Bondi. “This network of Iranian-backed sites will no longer broadcast anti-American hate.”
The seizure also included domains like Justicehomeland[.]org, which was previously used to harass the Albanian government for its support of Iranian dissident groups. FBI Director Kash Patel emphasized that the bureau is “not done” pursuing the actors behind these keyboard threats.
“We will hunt down every actor behind these cowardly death threats and cyberattacks,” Patel said. “This FBI will bring the full force of American law enforcement down on them.”
Crunchyroll Investigates Alleged 100GB Data Breach Linked to Third-Party Partner
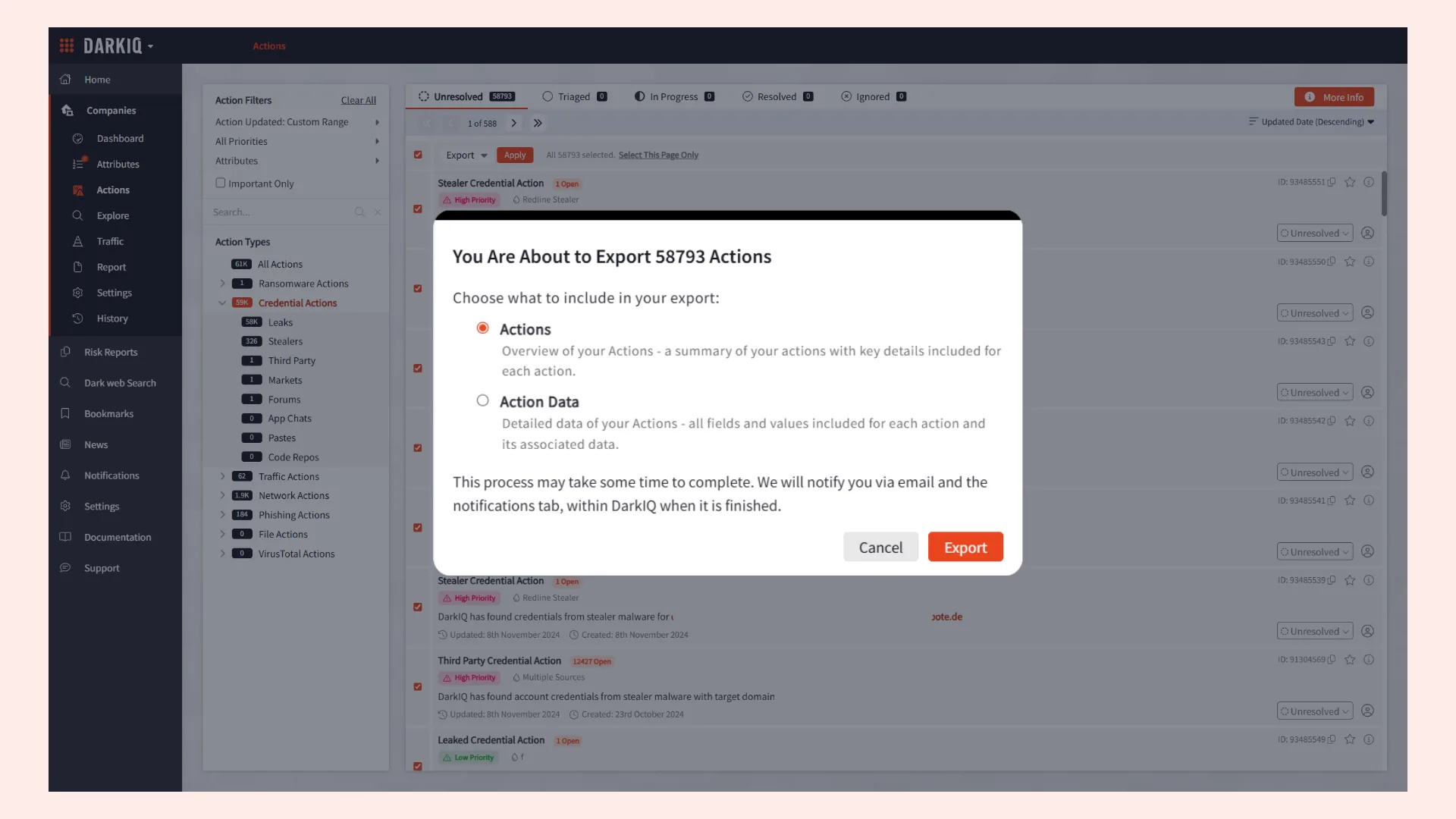
Crunchyroll, the Sony-owned anime streaming giant, is reportedly investigating a significant security incident after threat actors claimed to have exfiltrated 100GB of sensitive user data.
The breach, which allegedly occurred on March 12, 2026, reportedly targeted internal systems and customer support tools. Preliminary reports suggest that the hackers gained access through a compromised employee account at Telus, a third-party outsourcing firm providing business services to the platform. The attacker reportedly used malware to infiltrate the employee’s system and move laterally into Crunchyroll’s operational infrastructure.
Cybersecurity researchers indicate that the stolen information includes user IP addresses, email IDs, and credit card details. While the attackers were reportedly detected and removed within 24 hours, the scale of the extraction suggests a highly coordinated operation. If confirmed, the exposure of financial and personal data could leave millions of users vulnerable to identity theft and sophisticated phishing campaigns.
As of now, Crunchyroll has not issued a formal statement or notified its user base. Security experts advise subscribers to monitor their financial statements and remain vigilant against suspicious communications while the company works to verify the extent of the claim.
Critical Infrastructure Being Targeted by PureLog Stealer Malware
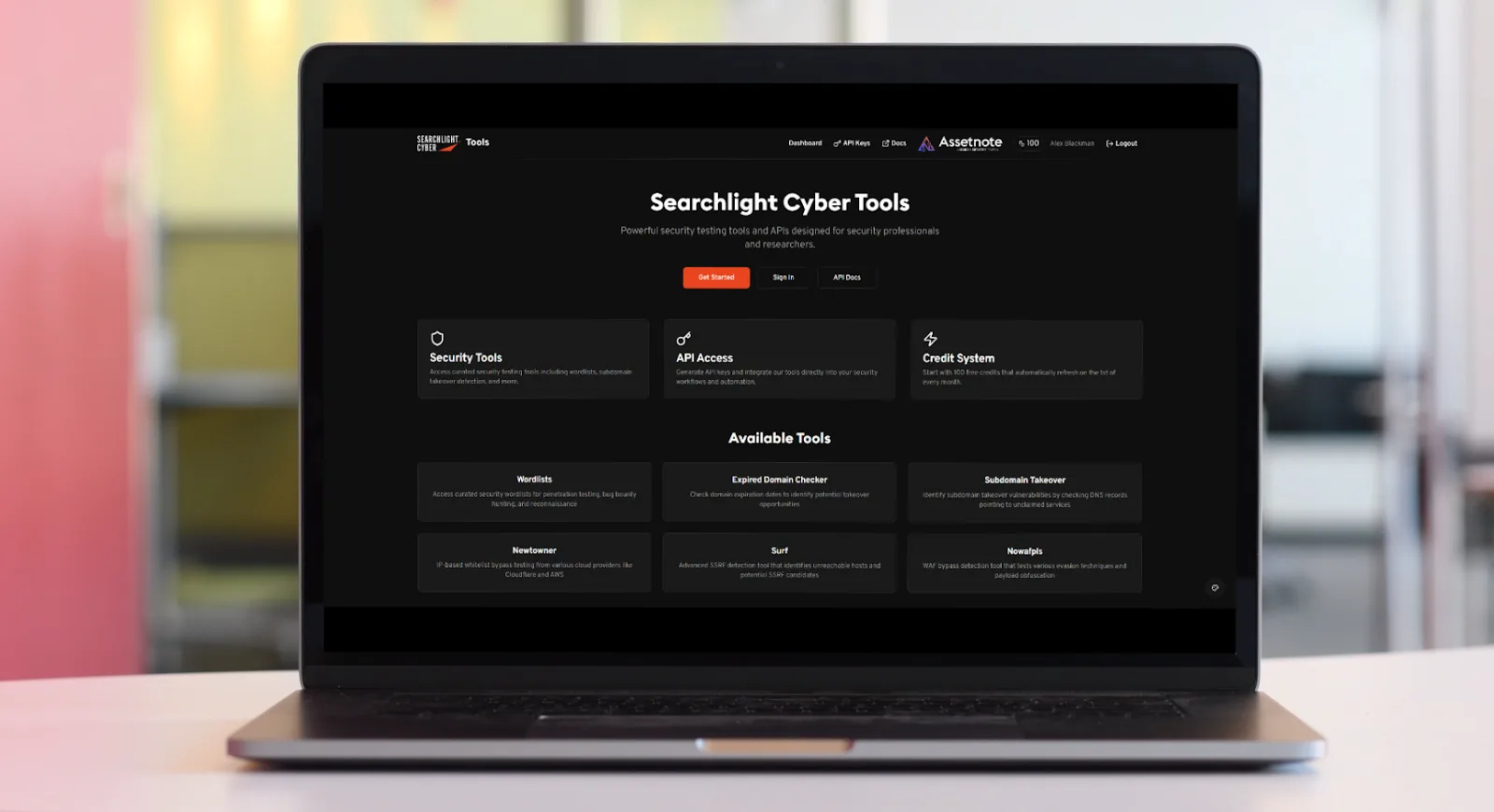
A sophisticated phishing campaign is currently targeting organizations across critical infrastructure sectors, including healthcare, government, hospitality, and education. According to a recent report from Trend Micro, threat actors are leveraging fraudulent copyright-infringement notices to deliver the PureLog Stealer, a low-cost but highly effective data-stealing malware.
The attackers gain initial access by exploiting a sense of urgency. Victims receive phishing emails that appear to be formal legal notices regarding copyright violations. These emails are often tailored to the victim’s local language, significantly enhancing the perceived authenticity of the lure. Organizations in Germany, Canada, the US, and Australia have been identified as primary targets, suggesting a selective and structured approach to victimology rather than simple mass distribution.
What distinguishes this campaign is its heavy reliance on in-memory execution to bypass traditional security defenses. Once a user executes what appears to be a benign PDF attachment, a multistage infection chain begins. This process utilizes Python-based and .NET loaders that perform environmental checks for sandboxes or virtual machines to evade analysis.
To further minimize their footprint, the malware retrieves decryption keys from a remote server at runtime, ensuring payloads remain encrypted until they are active in memory. The campaign also features a bypass for Windows Defender’s Antimalware Scan Interface (AMSI) and heavy code obfuscation, leaving scarcely any forensic trail for security researchers to follow.
Once successfully deployed, PureLog Stealer establishes persistence through registry modifications. The malware is capable of capturing screenshots, profiling the infected system, and harvesting sensitive data. Targeted information includes Chrome browser credentials, cryptocurrency wallets, and various system details, posing a significant threat to the data integrity of the targeted sectors.