This week’s cybersecurity and dark web news stories discuss RansomHouse hack on cybersecurity firm, the hackers caught using AI to find and exploit vulnerabilities, and Checkmarx plugin compromise.
Cybersecurity Giant Trellix Gets Hacked
Trellix, the cybersecurity firm formed from the merger of FireEye and McAfee Enterprise has confirmed that attackers gained unauthorised access to a portion of its source code repository. The breach appears to have occurred on April 17, and the company went public about it in early May.
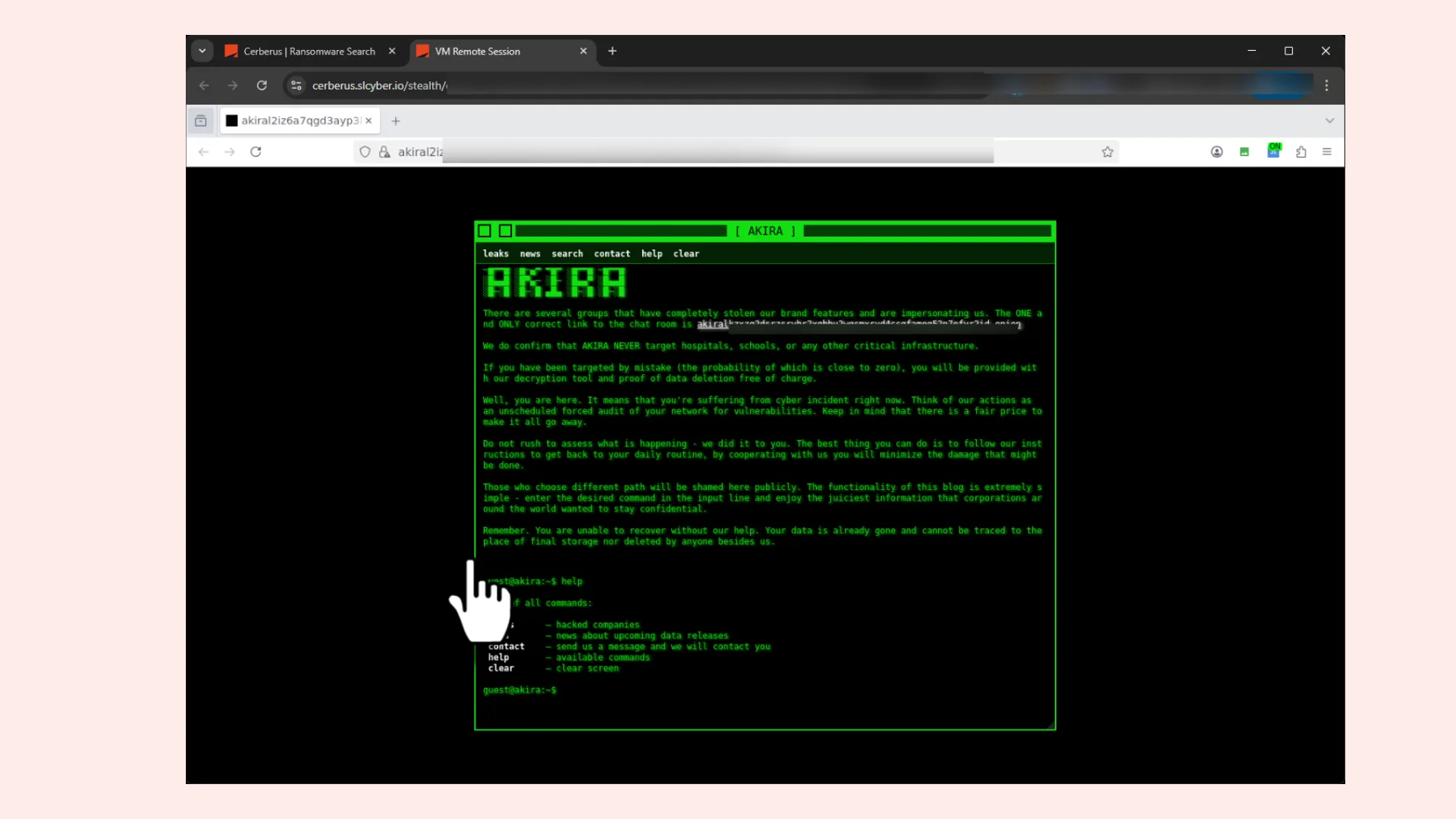
Now RansomHouse has stepped forward to claim responsibility, publishing screenshots on their dark web leak site that purportedly show access to Trellix’s internal infrastructure, including appliance management systems and dashboards tied to VMware, Rubrik, and Dell EMC environments.
Trellix’s official line is measured but cautious: there is currently no evidence that source code was exploited or that the software distribution pipeline was tampered with. The company has engaged forensic experts and notified law enforcement, and has promised further details once the investigation concludes.
RansomHouse, active since 2022, is a ransomware-as-a-service operation known for targeting large enterprises and leaking data to increase pressure on victims. Their toolkit includes a ransomware variant called Mario ESXi, built on leaked Babuk source code, and a tool called MrAgent designed to automate attacks on VMware hypervisor environments.
The deeper concern here goes beyond Trellix itself. A cybersecurity vendor’s source code is a potential roadmap for attackers, a way to understand how defences work and, potentially, how to evade them. Whether that risk materialises remains to be seen, but the incident adds fresh urgency to the question of how security firms secure themselves.
Google Warns That AI-Powered Hacking Has Arrived
For years, cybersecurity researchers warned that AI would eventually be weaponised by hackers to discover and exploit software vulnerabilities faster than any human could. This week, Google confirmed that moment has come.
Google’s threat intelligence team announced it had disrupted a criminal group that used an AI large language model to identify a previously unknown vulnerability in a popular system administration tool. The flaw would have allowed attackers to bypass two-factor authentication. Google notified the affected company and law enforcement, and says the operation was stopped before damage was done.
“It’s here,” said John Hultquist, chief analyst at Google’s threat intelligence arm. “The era of AI-driven vulnerability and exploitation is already here.”
Google declined to name the affected company or identify which AI model was used, noting only that it was likely neither Google’s Gemini nor Anthropic’s Claude Mythos. No government-linked threat actor was identified, though the company noted that groups connected to China and North Korea have been exploring similar techniques.
The timing is significant. Anthropic recently announced a new model called Mythos, described as so capable in cybersecurity and hacking tasks that the company limited its release to a small group of trusted organisations. Anthropic also launched Project Glasswing, a coalition including Amazon, Apple, Google, Microsoft, and JPMorgan Chase, aimed at hardening critical software against the threats such models could enable. OpenAI, meanwhile, announced a specialised cybersecurity version of ChatGPT restricted to defenders protecting critical infrastructure.
The consensus among experts is double-edged: AI will ultimately help defenders patch vulnerabilities faster, but in the near term, the sheer volume of exploitable legacy code means the world may face a dangerous transitional period before the tools of defence catch up with the tools of attack.
Checkmarx’s Supply Chain Nightmare: A Breach That Kept Coming Back
If a single cybersecurity incident can illustrate how relentless and sophisticated modern supply chain attacks have become, the ongoing Checkmarx breach is it.
What began as a targeted attack on specific developer tools has since expanded into a saga of compromised artefacts, stolen data, and repeated attacker persistence, with the hacker group LAPSUS$ ultimately publishing stolen Checkmarx data on the dark web in late April.
The initial attack is believed to have stemmed from the so-called Trivy supply chain attack, in which the threat actor group TeamPCP compromised the open-source Trivy security scanner and used it to harvest credentials from downstream users. Those stolen credentials appear to have given attackers a foothold in Checkmarx’s GitHub repositories, where they injected malicious code into developer tools used by thousands of organisations worldwide.
The compromised artefacts included VS Code extensions, GitHub Actions workflows, a Docker Hub KICS image, and a modified version of the Checkmarx Jenkins plugin published to the Jenkins Marketplace. In each wave, the malicious code was designed primarily to exfiltrate secrets and credentials from CI/CD pipelines and developer workstations.
Checkmarx has responded at each step: removing malicious artefacts, rotating credentials, engaging Mandiant for forensic support, notifying law enforcement, and locking down affected repositories. The company is emphatic that its Checkmarx One SaaS platform and customer production environments were not directly compromised, though customers who ran the tainted artefacts in their own pipelines may have exposed their own secrets.
The key lesson is one the industry keeps relearning: your security posture is only as strong as the software supply chain you depend on. If a tool you trust gets poisoned upstream, it doesn’t matter how well you’ve locked your own doors.
Checkmarx has committed to publishing a full post-incident report and continues to update its security advisory page as the investigation progresses.