What should you look for in an attack surface management solution?
Selecting the right Attack Surface Management solution requires evaluating discovery scope, validation methods, prioritization logic, workflow integration, automation capabilities, and asset coverage. Your chosen platform should discover assets without manual input, verify exploitability with proof, and route findings to responsible teams [20].
Continuous external asset discovery capabilities
The tool must discover all assets in on-premises, cloud, third-party, shadow IT, and ephemeral services without relying on manually provided inputs [20]. Look for platforms providing persistent, live visibility rather than periodic scans [20]. Searchlight Cyber’s hourly scanning delivers the fastest discovery cadence available and surfaces dynamic changes as they occur.
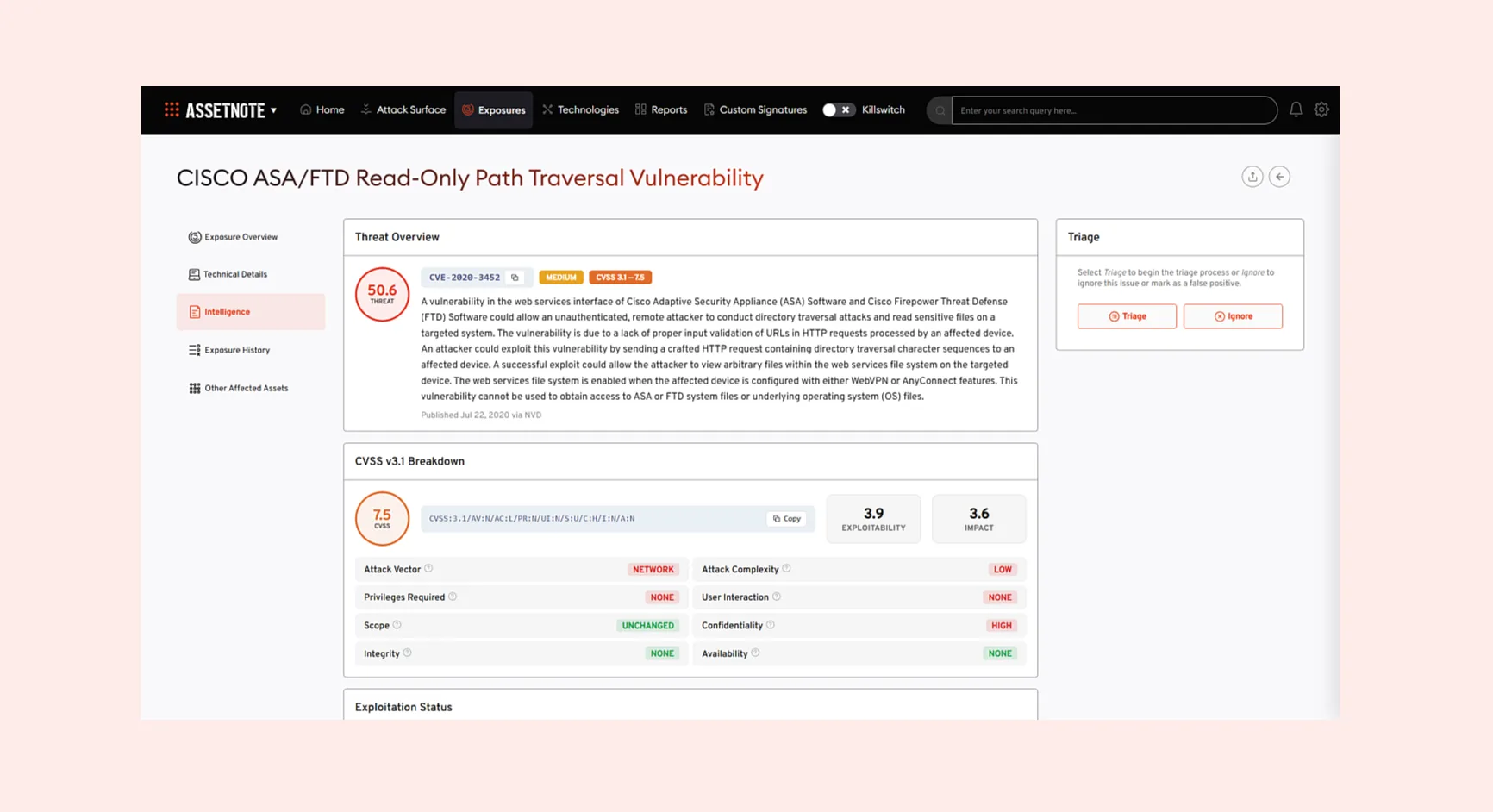
Exploit-based validation not just scanning
You just need evidence of actual exploitability, not theoretical vulnerability reports. Validation should include safe screenshots, clear reproduction steps, and controlled testing that avoids production impact [21].
Risk-based prioritization with business context
The platform should prioritize based on exploitability, asset value, business impact, and exposure context, not just CVSS scores [20]. Integrating business context, threat intelligence, and asset importance produces applicable risk rankings [5].
Integration with existing security workflows
Check for native integrations with SIEM, SOAR, vulnerability scanners, and ticketing systems to automate response [20]. Integration makes live data sharing and coordinated threat responses possible [8].
Automated alerting and remediation workflows
Automated routine tasks should reduce operational load [20]. Automated tools detect outdated or unpatched systems and help teams manage resources [8].
Coverage of cloud, on-premise, and third-party assets
Solutions must extend visibility into vendors, subsidiaries, and external dependencies [20]. Attack Surface Management uncovers risks associated with internet-facing assets connected to third-party vendors [8].