In the space of a few years, Telegram has gone from a convenient messaging app to a core piece of infrastructure in the cybercrime economy.
In 2026, we’ve continued to observe its development into a primary operational front line for the distribution of stealer logs: the credential and session data siphoned from infected endpoints that are sold and used in account takeover and fraud attacks.
This article outlines the mechanics of stealer logs, examining why cybercriminals are leveraging Telegram’s architecture for infostealer operations. We will explore the layered stealer log ecosystem on the platform, illustrate the industrial scale of the activity, and detail the four core characteristics that define effective threat intelligence and monitoring of Telegram threats.
How do stealer logs work – and why Telegram fits
What are stealer logs?
Stealer logs are the output of information‑stealer (also known as infostealer) malware that runs on a victim’s device and quietly harvests credentials (usernames, passwords, cookies), saved browser sessions, autofill data, crypto wallets, and often files and screenshots. A single log usually represents one infected machine, but one machine can expose dozens of personal and corporate accounts, from SaaS tools and VPNs to banking and social media. In addition to single logs, we also frequently see multiple stealer logs bundled together and sold in the form of ‘combo lists’: massive files containing URL, username and password details, matching up the credentials with the relevant website they were used for.
Example of files that make a single stealer log
Why do cybercriminals use Telegram?
Telegram is attractive to stealer operators for two reasons:
As an exfiltration channel: malware families increasingly send stolen data back to operators via Telegram bots or private chats, abusing the Bot API as a cheap, resilient C2 and data‑theft channel.
As a marketplace: the same ecosystem then republishes or resells these logs at scale through “log clouds” and specialist stealer‑log channels where actors trade, dump, or search logs for specific targets.
Recent breaches have shown how large these stealer log collections can be. In mid‑2024, for example, stealer logs collated from malicious Telegram channels exposed about 26 million unique email addresses in roughly 22GB of data, including the passwords and the sites they were used on. Another 2024 dataset pulled from Telegram channels contained 122GB of combo lists with 361 million unique email addresses, blending traditional credential lists with stealer‑derived data. For defenders, this illustrates two points: the volume is enormous, and Telegram is central to how these logs are aggregated and weaponized.
Telegram post with downloadable stealer logs. Note the requirement of a password to decompress content – this is common
The stealer log ecosystem on Telegram
Private vs public environments
From a threat‑intelligence perspective, not all Telegram sources are equal. The most operationally useful stealer log content tends to live in a layered ecosystem:
- Public “log cloud” channels that repost huge volumes of credentials, often including older or already‑traded logs.
- Semi‑private stealer‑as‑a‑service communities where operators sell access to fresh infections, offer subscriptions, or run automated bots to deliver logs on demand.
- Fully closed, invite‑only groups where high‑value stealer logs and tailored access (for specific organisations, sectors, geographies) are brokered to trusted buyers.
Open channels are useful for broad exposure monitoring; such as detecting when your brand or domains appear in large public log dumps, but the most time‑sensitive, targeted material is usually traded in gated groups. That’s where you’re more likely to see logs curated for specific sectors, regions, or enterprises, rather than generic spillover from mass malware campaigns.
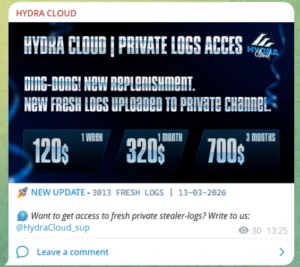
Example of an advert for private logs
Example post advertising private cloud access. Note how the group advertize a free section and that they also provide sample logs that are password protected. The samples are used to show the quality of the content and can be fresh.
Stealer operators using Telegram for exfiltration
Many modern stealers are designed with Telegram integration baked in. Recent malware families have shown a typical pattern: harvesting browser‑stored credentials, session cookies, files and screenshots, packaging them into an archive, and sending that archive via the Telegram Bot API to a hard‑coded chat ID controlled by the operator. The bot caption often includes a simple victim fingerprint (username, country, IP, infection ID), making it easy for actors to prioritise valuable logs.
This use of Telegram as both transport and triage layer lowers the barrier to entry for actors who lack their own C2 infrastructure. It also means that defenders who only monitor traditional dark‑web forums will miss the earliest phase of log circulation, where the freshest and most impactful data is often traded.
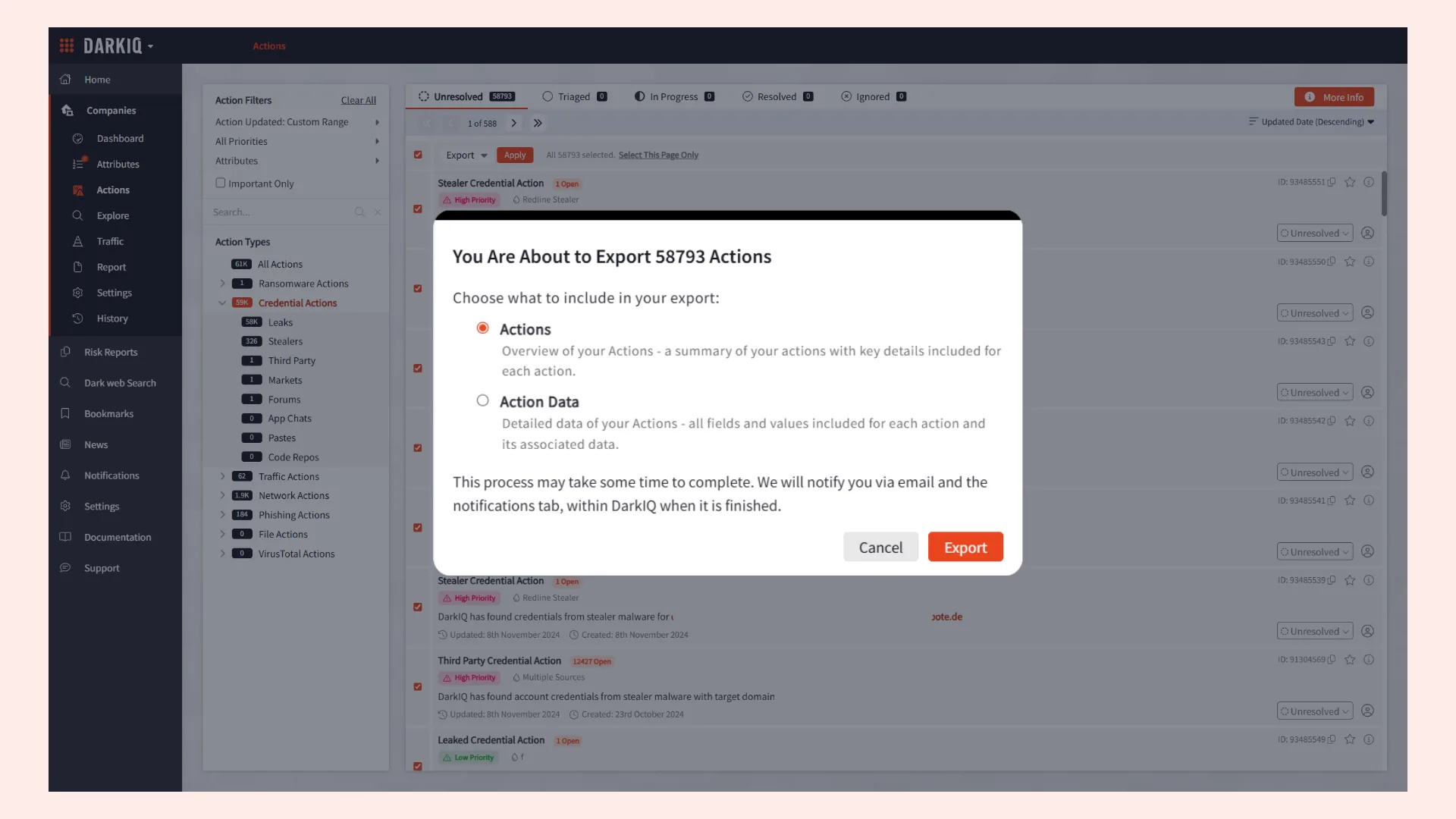
How to monitor cyber threats on Telegram
The key challenge for defenders is separating low‑value noise; commodity logs already scraped into multiple breach repositories, from high‑risk, high‑freshness material that indicates active compromise of your users or infrastructure. Telegram’s structure, combined with the speed at which posts are edited or deleted, makes that difficult without purpose‑built collection, scraping, and archiving.
While stealer logs are a prominent threat on Telegram, they are not the only reason defenders need visibility into the platform. Research shows that illicit Telegram groups and channels are used to:
- Advertise and coordinate fraud services, including cash‑out and forged documents
- Distribute leaked databases and combolists in the wake of data breaches, often acting as a backup when traditional forums are disrupted.
- Promote ransomware activity, either through group chats associated with ransomware groups or by reposting links to victims and data leaks from Tor‑hosted sites.
- Amplify hacktivist campaigns and politically motivated operations, including DDoS attacks and influence operations against high‑profile events or national targets.
For organisations concerned about physical security and disinformation; for example around global events like the Olympics, these channels can serve as an early‑warning layer for threats, calls to action, or targeting chatter that may never appear on traditional dark‑web forums but still have real‑world impact.
Telegram also continues to host carding and refund communities, where actors sell compromised card data, offer refund‑as‑a‑service, and share techniques to manipulate merchants’ margins and chargeback processes. For many retailers and financial services organisations, this activity translates directly into loss and fraud‑driven operational risk, even when their own environment has not been directly breached.
What good Telegram monitoring looks like
Understanding why Telegram matters is only half the equation. The harder question is whether your threat intelligence solution has the access and focus to turn Telegram signals into the right level of intelligence for your requirements. From our experience, effective monitoring of illicit Telegram activity has four core characteristics:
1. Consider intelligence requirements and levels of intelligence
The most operationally significant activity on Telegram concentrates in gated communities – private groups where access is earned, brokered, or invitation‑only. Monitoring that relies primarily on public channel visibility may just be skimming the surface and missing critical pieces of data or intelligence. This data may eventually end up in publicly accessible sources, but access to gated communities could enable you to identify a threat and take action far earlier. A tight focus on the most impactful, active groups is essential if you want to detect real threats rather than accumulate screenshots.
2. Continuous review
Telegram is a high‑velocity environment. Channels spin up and disappear, posts are published and deleted, and stealer logs are bought, sold, and resold in hours rather than days. Snapshot investigations can’t keep pace with that tempo. The overall aim of intelligence is to develop an understanding in order to effectively inform and influence your decision-making process. This understanding is based on foresight (identifying and anticipating what may happen) in addition to insight (understanding why something has happened or is happening), meaning that the ability to follow the intelligence principle of continuous review is a key factor in Telegram threat intelligence.
3. Scraping and archiving
Posts get deleted, channels go dark, and content is routinely edited or removed when operators sense exposure or platform enforcement. If your Telegram monitoring doesn’t automatically scrape and archive what it collects, preserving what was posted, when, and by whom, then you’re not building an intelligence asset; you’re building a revocable snapshot. For effective investigations, takedown support, and fraud response, permanence is key.
4. Optimized for signal, not just volume
More Telegram data is not the only goal. The goal is access to high‑signal sources that improve specific decisions: whether to trigger an incident response, whether to escalate a credential exposure to your fraud team, or whether a threat against your organisation or sector is credible. That requires enrichment, correlation, and structure, turning raw posts and log dumps into entities, timelines, and alerts that map to your risk model, rather than a huge, unsearchable archive.
How Searchlight Cyber approaches Telegram monitoring
Searchlight’s approach to Telegram monitoring is built around exactly these principles. Our platform ensures breadth of collection while prioritizing high‑value sources from private groups on both the dark web and Telegram, investing in gaining and maintaining access to closed communities rather than simply embedding bots in public channels and collecting data on request.
Crucially, we scrape and archive Telegram data continuously, ensuring that even deleted posts remain searchable within the platform. That means when an investigation begins or an incident escalates; whether it’s a stealer‑log exposure, a ransomware threat, or chatter about your brand in a high‑risk group, the evidence you need is already there.
Telegram is increasingly functioning as an operational front line of cybercrime, particularly for the stealer log ecosystem.
If you’d like to see how this telemetry can strengthen your threat intelligence program, speak to our team here: Book a demo.