This week’s cybersecurity and dark web news stories discuss the Vercel data breach, Indonesian authorities phishing network Take Down, and the ransomware groups in conflict.
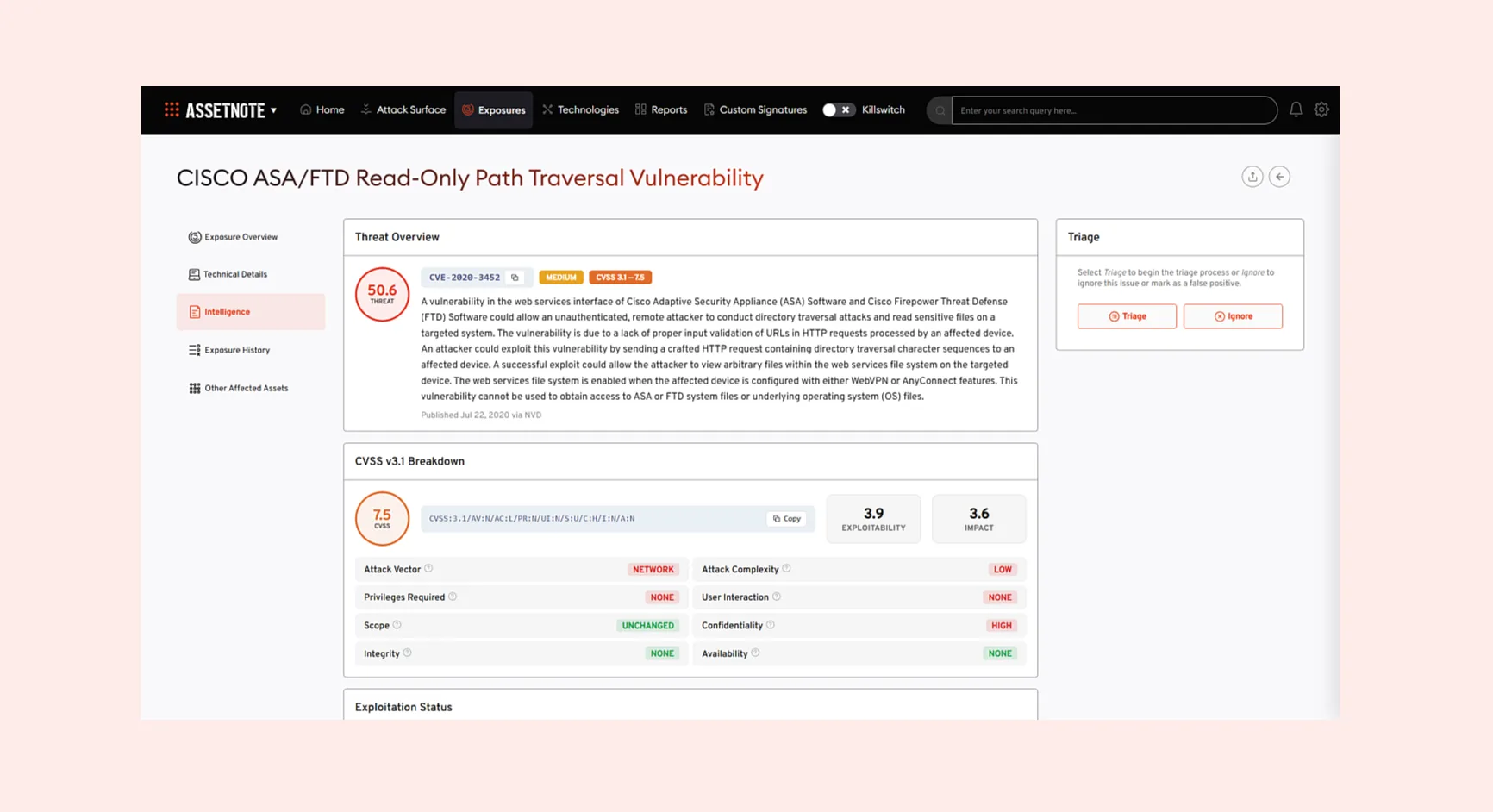
Vercel Confirms Security Breach Traced to Third-Party AI Tool
Cloud deployment platform Vercel has disclosed a security incident in which attackers gained unauthorised access to internal systems — with the breach originating not from Vercel itself, but from a small AI productivity tool used by one of its employees.
The attacker compromised Context.ai, a third-party tool, and used that access to take over the employee’s Google Workspace account. From there, they were able to reach Vercel environments and access environment variables that had not been marked as “sensitive.”
Vercel has moved to reassure customers on two fronts. Environment variables designated as sensitive are stored in a way that prevents them from being read, and the company says it has no current evidence those values were accessed. In collaboration with GitHub, Microsoft, npm, and Socket, Vercel’s security team has also confirmed that no published npm packages were tampered with.
However, the incident carries a wider warning. Vercel has published the OAuth app identifier linked to Context.ai as an indicator of compromise, noting the tool’s Google Workspace integration may have affected hundreds of users across multiple organisations. Vercel is working with Mandiant and law enforcement as the investigation continues.
Customers have been advised to rotate non-sensitive environment variables immediately and enable multi-factor authentication.
FBI and Indonesian Police Smash $20 Million Phishing Operation
US and Indonesian law enforcement have jointly dismantled a global phishing network responsible for targeting more than 17,000 victims and attempting over $20 million in fraud – in what officials are calling a first-of-its-kind operation between the two countries.
At the heart of the scheme was the W3LL phishing kit, a tool sold for approximately $500 that enabled criminals to deploy convincing replica login pages. Beyond stealing usernames and passwords, the kit captured session data that allowed attackers to bypass multi-factor authentication entirely.
The operation was supported by an online marketplace, W3LLSTORE, which handled the sale of more than 25,000 compromised accounts between 2019 and 2023. After the marketplace closed, the criminal network migrated to encrypted messaging platforms and continued operating, targeting thousands more victims through 2024.
Indonesian National Police detained the alleged developer, identified only as G.L., and seized key domains tied to the operation. FBI Atlanta Special Agent in Charge Marlo Graham described the platform as “a full-service cybercrime platform,” adding that the bureau would continue working with international partners to protect the public.
Authorities say the takedown marks a significant blow to the broader phishing-as-a-service ecosystem.
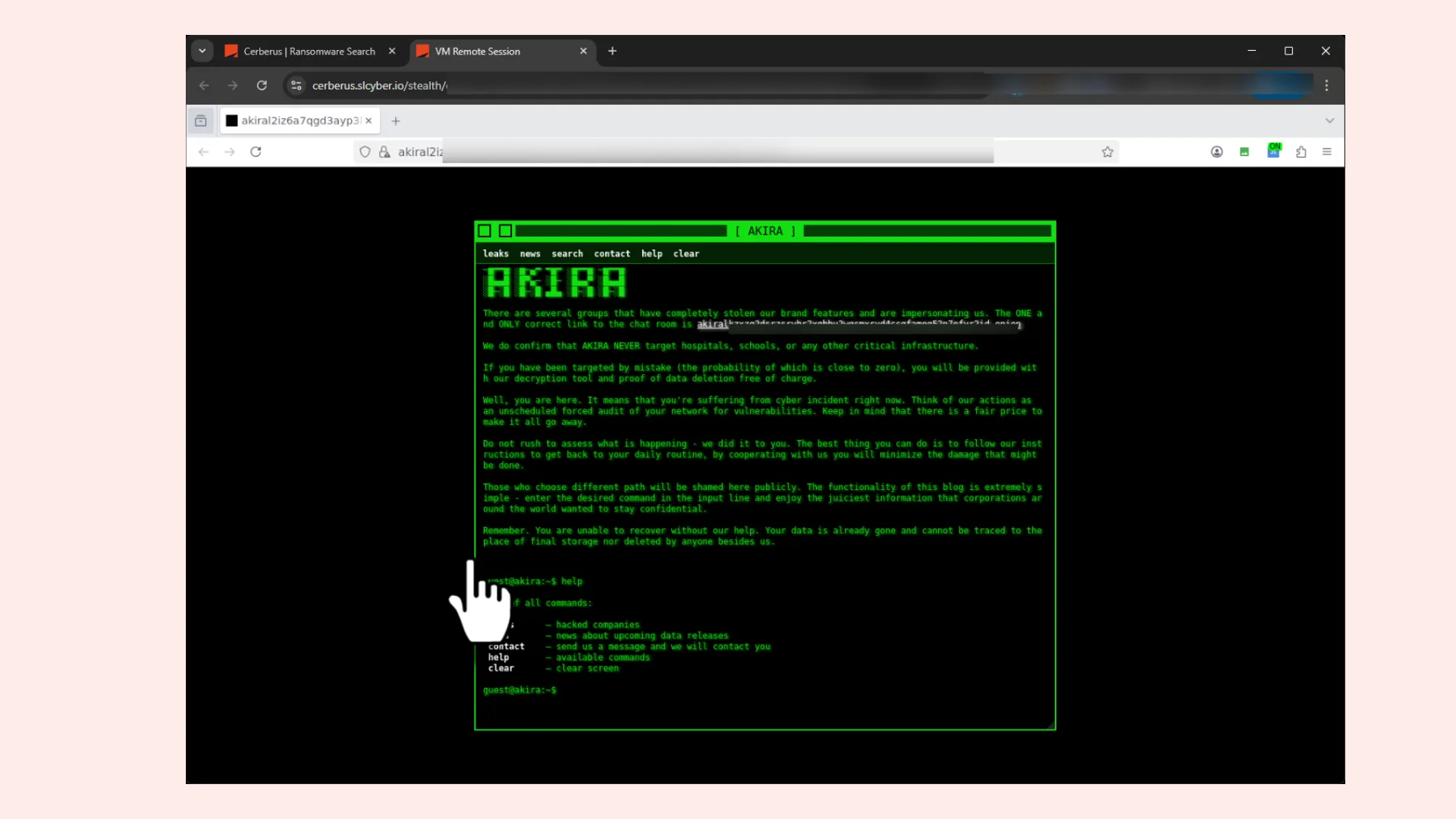
Ransomware Gang 0APT Turns Its Extortion Tactics on Rival Criminals
In an unusual development on the dark web, ransomware group 0APT has threatened to expose the identities of members of a rival gang – applying the same double-extortion tactics typically reserved for corporate victims.
Dark web monitors spotted 0APT’s move on Sunday, with the group threatening to reveal the identity photos, names, and locations of those affiliated with fellow gang Krybit unless payment was received. A sample of allegedly stolen data was leaked as a warning.
The operation drew immediate scrutiny for its apparent hypocrisy. 0APT’s own post described Krybit as a group posing “significant risks to cybersecurity and data privacy worldwide” – a characterisation that observers noted applied equally to 0APT itself.
Security researchers who examined the leaked files found plaintext credentials belonging to Krybit operators, cryptocurrency wallet addresses, and no evidence of any ransoms ever having been paid – casting doubt on the rival group’s operational standing.
0APT launched in January 2026 and is considered a credible threat with genuine technical capability, though its early victim claims were assessed as likely inflated. Krybit, by contrast, appears to have only emerged within the past few weeks.
Krybit’s website is currently offline. The episode echoes similar criminal infighting seen in 2025, when DragonForce attacked and ultimately absorbed rival operation RansomHub.