This week’s cybersecurity and dark web news stories discuss LeakBase shut down, significant ShinyHunters campaign, and a powerful kit targeting iOS.
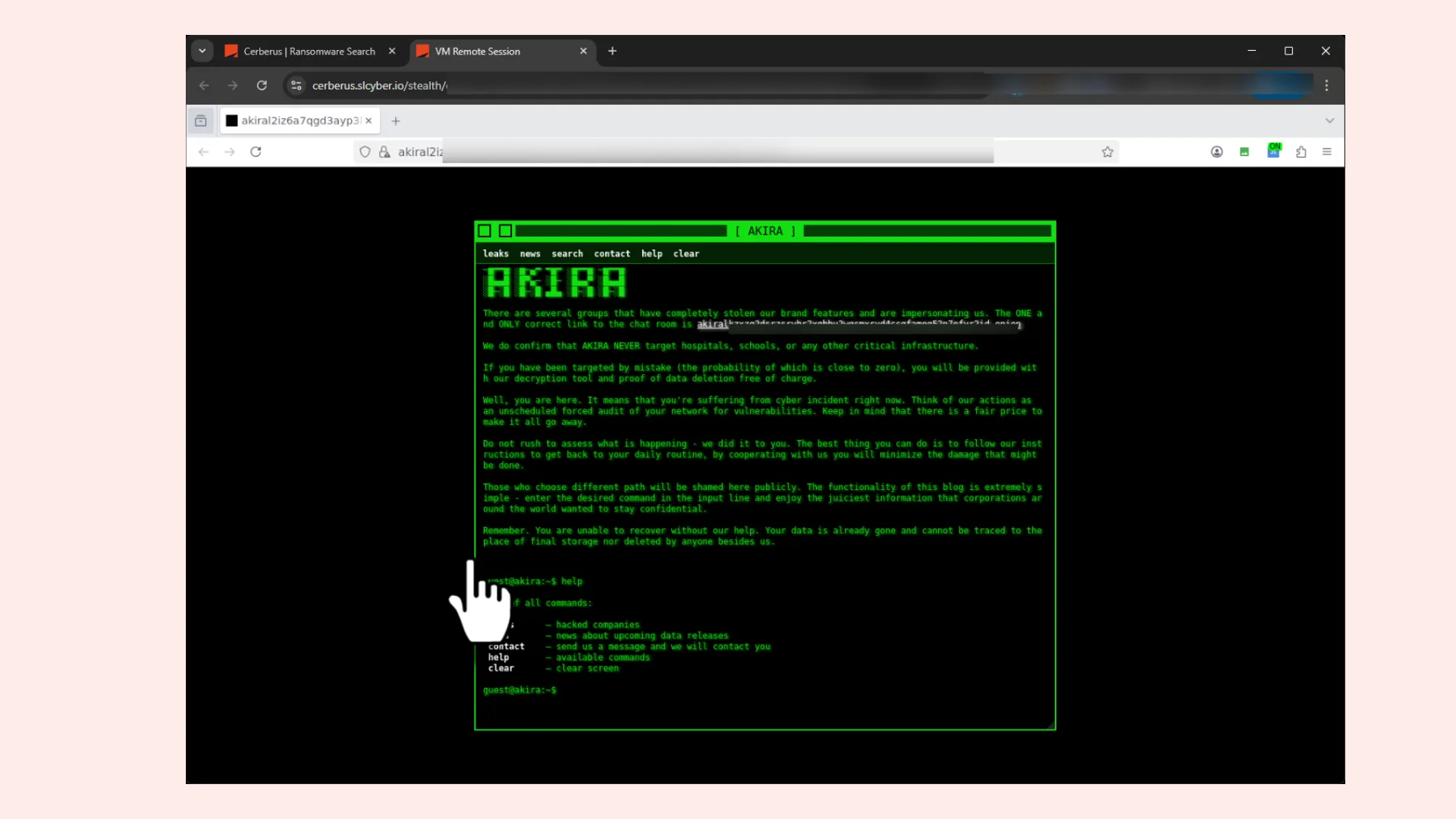
Global Law Enforcement Shuts Down Major Cybercrime Hub LeakBase
U.S. and European authorities have successfully seized and shut down LeakBase. Billed as one of the world’s most expansive forums for illicit activity, the site served as a primary marketplace for stolen passwords, banking credentials, and sophisticated hacking tools.
The takedown has provided investigators with huge amounts of intelligence. According to law enforcement officials, the seized database contains over 142,000 registered members and more than 215,000 private messages, offering a rare look into the communications of active cybercriminals.
Since its inception in 2021, LeakBase had grown into a massive archive of compromised data. The site hosted hundreds of millions of account credentials, credit card numbers, and sensitive banking routing information, facilitating a surge in account takeovers and cryptocurrency theft worldwide.
This is the latest takedown targeting sites that trade in stolen credentials, which are increasingly used to break into people’s accounts and steal data and cryptocurrency.
Europol confirmed that the operation was truly global, involving approximately 100 enforcement actions. This included targeted measures against 37 of the forum’s most active users. The FBI finalized the shutdown on Wednesday by redirecting the site’s domain to agency-controlled servers.
Visitors to the site are now met with an official seizure notice. FBI cyber official Brett Leatherman told The Record that the investigation has already led to 13 arrests and dozens of suspect interviews. With the forum’s entire database now in the hands of the police, more enforcement actions are likely on the horizon.
Salesforce Experience Cloud Sites Targeted in Major Data breach
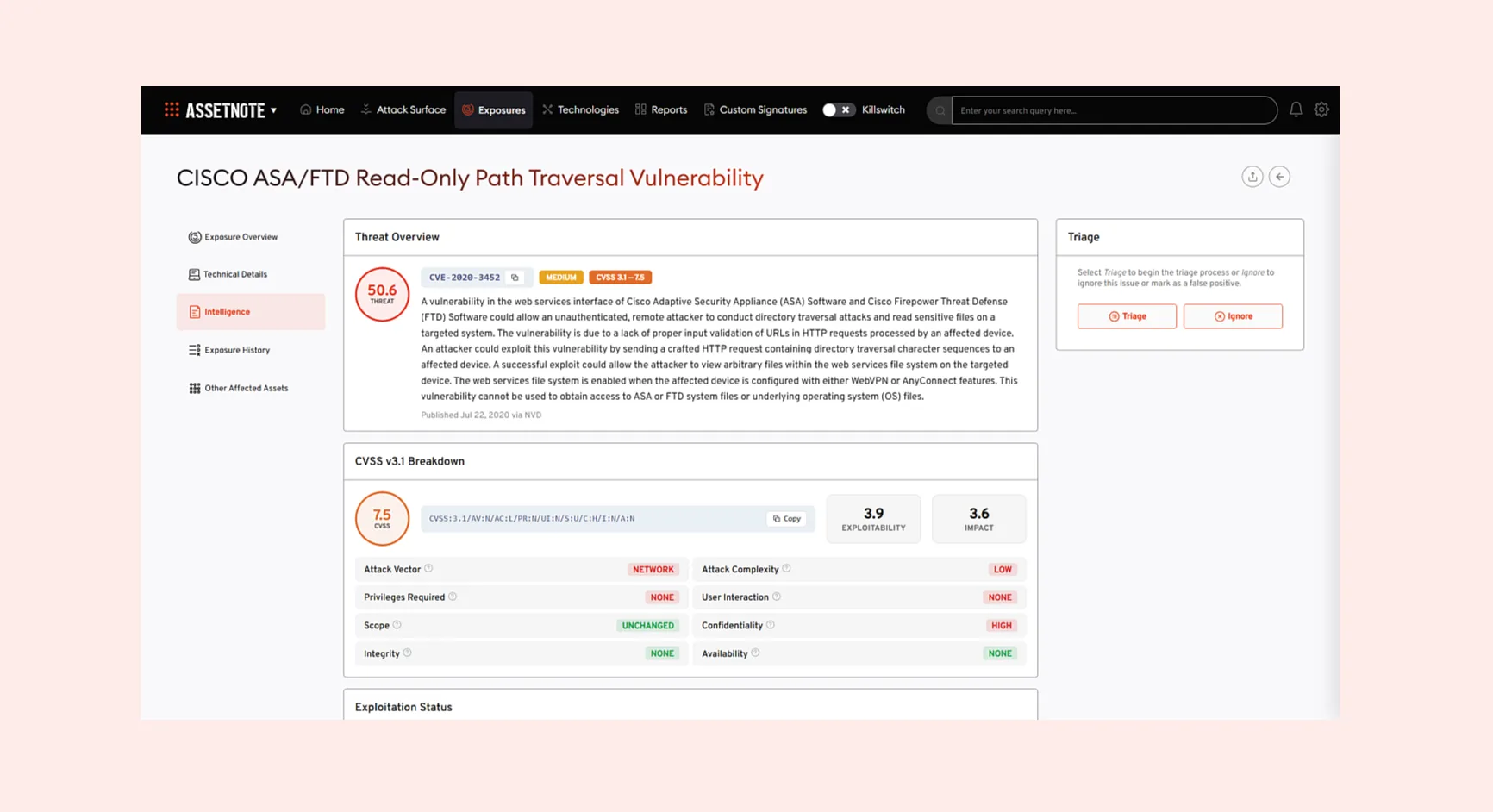
A notorious threat group is reportedly exploiting misconfigured guest permissions to siphon data from high-profile organizations.
The extortion group known as ShinyHunters has claimed responsibility for a massive data theft campaign targeting Salesforce customer data. Speaking with reporters, a spokesperson for the group alleged they have successfully exfiltrated information from nearly 400 websites and approximately 100 high-profile companies, including AMD, Sony, and Salesforce itself.
The campaign centers on Salesforce Experience Cloud sites. Salesforce recently issued a security warning regarding a “known threat actor group” actively scanning for public-facing sites that are vulnerable to unauthorized access. According to Salesforce, the issue is not a flaw in the platform but rather a result of guest user profiles being “inadvertently configured with overly broad permissions.”
The attackers are reportedly using a modified version of a free scanning tool originally developed by Mandiant. While the original tool was designed to help admins detect misconfigurations, the threat actors have repurposed it to automate the exploitation and extraction of sensitive records, such as names and phone numbers. These details are often used in follow-up social engineering and voice phishing attacks.
Salesforce continues to urge customers to review their guest user access settings and follow official guidance to safeguard their data. We will continue to update this story as more organizations respond to requests for comment.
New iOS Exploit Kit “Coruna” Targets iPhones Globally
Google’s Threat Intelligence Group has uncovered “Coruna,” a sophisticated iOS exploit kit capable of compromising iPhones running iOS 13 through 17.2.1. Featuring five exploit chains and 23 vulnerabilities, the toolkit has transitioned from targeted surveillance to broader financially motivated attacks against cryptocurrency users.
How the Attack Works
The Coruna attack lifecycle typically follows a four-stage process:
- Initial Delivery: Users are lured via malicious websites or watering-hole attacks.
- Browser Exploitation: Attackers leverage WebKit vulnerabilities to gain entry.
- Privilege Escalation: The exploit gains system-level control.
- Payload Deployment: Spyware is installed to monitor communications and steal credentials.
Just how many other victims Coruna may have hit, including Ukrainians who visited websites infected with the code by the suspected Russian espionage operation, remains unclear. Google have not commented beyond its published report and Apple did not immediately provide comment on Google or iVerify’s findings.