A ransomware leak site is a dark web platform operated by a ransomware group where stolen data is published if a victim refuses to pay the ransom. These sites serve as a pressure tactic, threatening reputational and regulatory damage to force payment. Paradoxically, they also create a source of intelligence that security professionals can monitor and analyse.
There’s no doubt the ransomware landscape is constantly evolving. In this blog, we discuss how the intelligence hidden in ransomware leak sites can give organizations the information they need to secure and protect their assets.
Key Takeaways
- Ransomware is accelerating. The second half of 2025 saw a 30% increase in victims listed on ransomware leak sites compared to 2024, alongside a 5% rise in active ransomware groups – underscoring the need for continuous vigilance.
- Leak sites are an intelligence goldmine. The very platforms ransomware groups use to pressure victims inadvertently expose their tactics, targeting preferences, and operational tempo – giving security teams actionable data to work with.
- Dark web monitoring enables proactive defence. Rather than waiting for an attack to occur, organisations can use ransomware intelligence to identify emerging threats, spot supply chain exposures, and close vulnerabilities before they are exploited.
- Attack Surface Management amplifies intelligence. Combining dark web intelligence with ASM creates a powerful feedback loop – enabling teams to quickly map a ransomware group’s known TTPs against their own exposed assets and prioritise remediation accordingly.
- Breach analysis benefits everyone in the supply chain. When a partner or supplier is hit by ransomware, third parties often receive little detail about what was compromised. Direct access to breach analysis can help affected partners understand their own exposure and act quickly to limit downstream damage.
- An intelligence-driven approach is now essential. Treating ransomware as an isolated incident is no longer viable. Organisations that combine continuous monitoring, dark web intelligence, and exposure management are far better positioned to protect their critical assets.
Update April 2026
The second half of 2025 has seen new heights in terms of ransomware victims, with 30 percent increase in victims listed by ransomware leak sites compared to 2024. As well as an increase in the number of victims, the Threat Intelligence team at Searchlight Cyber has also seen a rise in the number of active ransomware groups (a 5 percent increase on H1 2025.)
So what does this mean for organizations and how can insights from the dark web help security teams outpace ransomware groups, and aid remediation after an attack has happened?
Gathering intelligence from ransomware groups
One of the quirks of the ransomware model is that while other cybercriminals seek to avoid the limelight, ransomware actors require it. Sometimes they have to post on the dark web, for example to recruit affiliates or to buy initial access that they can exploit. Other times, groups actively court publicity – either for their own egos or to apply pressure on their victims.
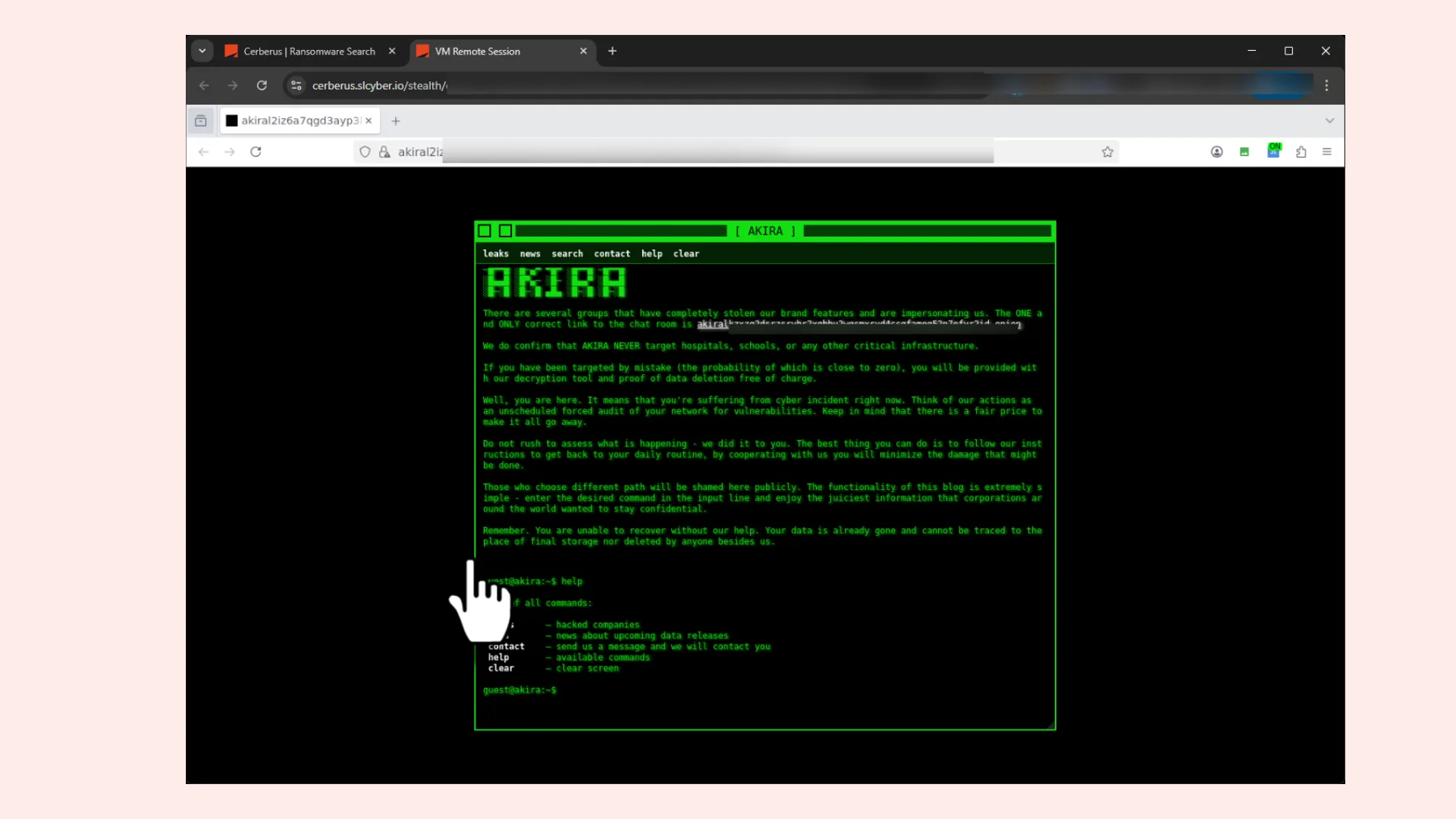
Ransomware groups employ a variety of Tactics, Techniques, and Procedures (TTPs) to maximise their leverage over victims. A particularly effective and very common tactic is the establishment and operation of public-facing extortion or leak sites. These dedicated platforms serve as a pivotal component of their multi-pronged pressure campaigns, primarily designed for public shaming. By publishing sensitive data stolen from compromised organizations, these sites aim to amplify the psychological and reputational pressure on victims, thereby increasing the likelihood of a ransom payment.
Because of the “public” information that ransomware groups share on the dark web to extort payment, it allows cybersecurity professionals to use dark web monitoring tools such as Searchlight Cyber to delve under the surface of their operations and use the intelligence to form part of their cybersecurity resilience plans.
The strategic importance of monitoring these extortion and leak sites cannot be overstated. For cybersecurity professionals, incident response teams, and intelligence analysts, consistent surveillance of these platforms offer invaluable insights.
Using the intelligence ransomware groups provide
What information can organizations glean from the activity of ransomware groups?
Gauging activity levels of ransomware groups
The volume and frequency of new victim postings on these sites serve as a barometer of a ransomware group’s operational tempo and success. Spikes in activity can indicate new campaigns, successful breaches, or shifts in targeting strategies. Conversely, a lull might suggest a group is regrouping, retooling, or facing disruption.
Monitoring for third-party or supply chain compromises
Beyond direct victims, these sites often inadvertently reveal details about third-party organizations that have been impacted through supply chain attacks. If a victim’s data includes information pertaining to their partners, suppliers, or clients, it can alert those entities to potential compromise, even if they were not the primary target of the initial ransomware attack. This proactive monitoring enables affected third parties to initiate their own incident response protocols, mitigating potential downstream damage.
Identifying trends in victimology and sector targeting
Analyzing the sectors and geographies of organizations appearing on leak sites, analysts can identify emerging trends in victimology, understand preferred sector targeting by specific groups, and anticipate future attack vectors.
Understanding the scope of data exfiltration
While the leak sites showcase a subset of stolen data, the nature of the published information can provide clues about the extent and type of data exfiltrated during a successful ransomware operation. This information helps victims understand the potential impact on their data privacy and regulatory compliance obligations.
Tracking ransomware group evolution and attribution
Over time, the content, design, and even the language used on these sites can offer clues about the evolution of ransomware groups, their affiliations, and assist in attribution efforts. Changes in TTPs visible through leak site activity can help track new variants or emerging threat actor groups.
Coupling ransomware intelligence with Attack Surface Management
Dark web intelligence becomes even more powerful when paired with Attack Surface Management (ASM). ASM gives organizations a clear view of their exposed assets and vulnerabilities. When combined, they create a powerful feedback loop that enables defenders to prioritize and act on the threats that matter most.
By overlaying a ransomware group’s TTPs with ASM, security teams can quickly identify whether their external attack surface includes the kind of assets ransomware groups are currently exploiting. This allows for faster detection of misconfigurations, outdated services, or exposed credentials that could serve as initial access points.
For example, if intelligence indicates a ransomware group is exploiting a specific VPN vulnerability, ASM can surface any related assets in an organization’s environment, enabling security professionals to patch, segment, or decommission them before they become an open door for ransomware groups.
Similarly, if a ransomware group is pivoting toward a new industry, organizations can align their exposure management and incident response plans accordingly.
Instead of responding to ransomware incidents after they occur, defenders can close the gaps that attackers are actively scanning for, reducing the attack surface before it’s exploited.
The benefits of ransomware breach analysis and intelligence
For victims of a ransomware attack
In 2025, Searchlight Cyber opted to automate the downloading and processing of breached ransomware victim information, thereby unlocking extensive opportunities from an intelligence and security standpoint. This information can empower end-users with the capability to conduct queries, facilitating security and intelligence operations, and aiding communication strategies during incident response scenarios.
For the organization directly experiencing a ransomware breach, the immediate aftermath is often chaotic. Robust incident response processes are fundamental for mitigating damage and facilitating recovery. A key aspect of this involves meticulously identifying what files have been extracted by the ransomware and gaining a comprehensive understanding of the threat actor’s movements and presence within the breached system.
Understanding “what was actually leaked?” goes beyond a simple inventory. It demands an in-depth assessment of the type of data compromised and, critically, the sensitivity of its content. Was it personal identifiable information (PII), intellectual property, financial records, or highly confidential strategic documents?
This detailed knowledge is paramount for effective remediation activities. Knowing precisely what information has been leaked enables targeted efforts to secure remaining systems, revoke compromised credentials, and notify affected individuals or entities.
For third-parties, suppliers, and business partnerships
While the direct victim grapples with the immediate aftermath, the ripple effects of a ransomware attack often extend far beyond their organizational boundaries.
The real security and intelligence benefit of having access to the breached content emerges for those who are a partner or third party to the victim. In scenarios where a business relation has been breached, it is unfortunately common for the affected third parties not to receive a detailed account as to what precisely the threat actor has managed to compromise.
This lack of transparency, though sometimes unavoidable for the victim due to ongoing investigations or legal constraints, can leave partners in a precarious position. The compromised data could contain highly sensitive documents and confidential content directly related to the third party’s operations, intellectual property, or even their own customers.
Conducting thorough breach analysis gives organizations, and their third parties, a clearer picture of what data has been exposed and how it could be leveraged by attackers. This level of insight is critical as it enables affected parties to respond quickly, contain potential downstream risks, and strengthen their defenses before ransomware groups can exploit the breach further.
Using intelligence to protect critical assets
As ransomware continues to evolve, organizations can no longer afford to treat these attacks as isolated incidents. By combining dark web intelligence, Attack Surface Management, and continuous monitoring, security teams can gain the visibility needed to understand both the ransomware landscape and their own exposure within it. This intelligence-driven approach empowers defenders to act earlier, protect critical assets, and reduce the ripple effects of ransomware, not just for their own organization, but across their entire supply chain.
Haven’t read our new ransomware in H2 2025 report? DOWNLOAD our report to learn more about the development of the ransomware landscape this year.
By monitoring ransomware leak sites and dark web forums, security teams can identify which sectors and geographies are being targeted, which vulnerabilities ransomware groups are actively exploiting, and whether any of your own data or credentials have already been exposed. This allows for pre-emptive action rather than reactive damage control.
ASM is the process of continuously identifying and monitoring all of an organisation’s externally exposed assets – such as systems, services, and credentials – that could be exploited by attackers. When combined with ransomware intelligence, ASM allows security teams to check whether their environment contains the specific weaknesses a ransomware group is known to target, enabling faster and more focused remediation.
Yes. Supply chain attacks mean that sensitive data relating to your organisation – contracts, communications, intellectual property – may have been exfiltrated from a partner’s systems without you being directly targeted. Ransomware breach analysis can reveal whether your data was included in a leak, allowing you to respond appropriately rather than remaining unaware of the exposure.
The data exfiltrated varies depending on the victim, but commonly includes personally identifiable information (PII), financial records, intellectual property, strategic documents, and credentials. Understanding exactly what was taken is critical for regulatory compliance, notifying affected individuals, and determining what remediation steps are needed.
Speed is critical. The moment data is published, it becomes accessible to other threat actors who may use it for follow-on attacks such as phishing, fraud, or further extortion. Organisations should initiate incident response protocols immediately – assessing what was leaked, revoking compromised credentials, notifying relevant parties, and working to close any vulnerabilities that enabled the initial breach.