In this blog, we explore why ransomware leak data creates security risks far beyond the organization that was directly attacked and why visibility into that leaked data is critical for every business in the supply chain.
In 2025, our data showed 7,458 victims appearing on ransomware leak sites, a record high. But that number only tells part of the story. Because when a ransomware group publishes stolen files, the damage doesn’t stop at the immediate and obvious victim. Supplier contracts, client records, shared credentials, and financial documents are just some of the information exfiltrated from one organization, which routinely contains data belonging to dozens of others. Companies who were never targeted, never breached, and in many cases, never even told.
The reality of modern ransomware is that an exposure may have nothing to do with the strength of your own defenses.
The leaked file problem not enough people are talking about
When ransomware groups publish stolen data, either to pressure victims into paying or after negotiations break down, they typically release it in the form of file trees – structured directories containing hundreds or thousands of documents pulled directly from the victim’s environment.
Those files don’t exist in isolation. With today’s complex and interlinked supply chains, organizations hold data that belongs to their entire ecosystem, ranging from supplier invoices and contracts, and customer account information.
When that data is published on a leak site, every organization represented within it is implicated, whether they know it or not.
The disclosure gap: why most affected organizations never find out
There is no reliable mechanism that compels a ransomware victim to notify the suppliers, partners, or customers whose data appeared in their leaked files. Regulatory frameworks focus primarily on the breached organization itself and voluntary disclosure to third parties can be inconsistent. According to the National Bureau of Economic Research, only 10.5 percent of worldwide ransomware incidents are disclosed by victims.
The result is a significant disclosure gap and the majority of organizations affected by ransomware incidents in their supply chain learn about their exposure late, often through their own investigations, media reporting, or in some cases, direct contact from the threat actors.
What kind of data is exposed in a ransomware leak?
The contents of ransomware leak data vary, but commonly include:
Commercially sensitive documents: Contracts, pricing agreements, tender responses, and partnership terms that may reference an organization directly.
Personal and customer data: Names, contact details, account numbers, and in some cases payment or identity information shared with the breached vendor.
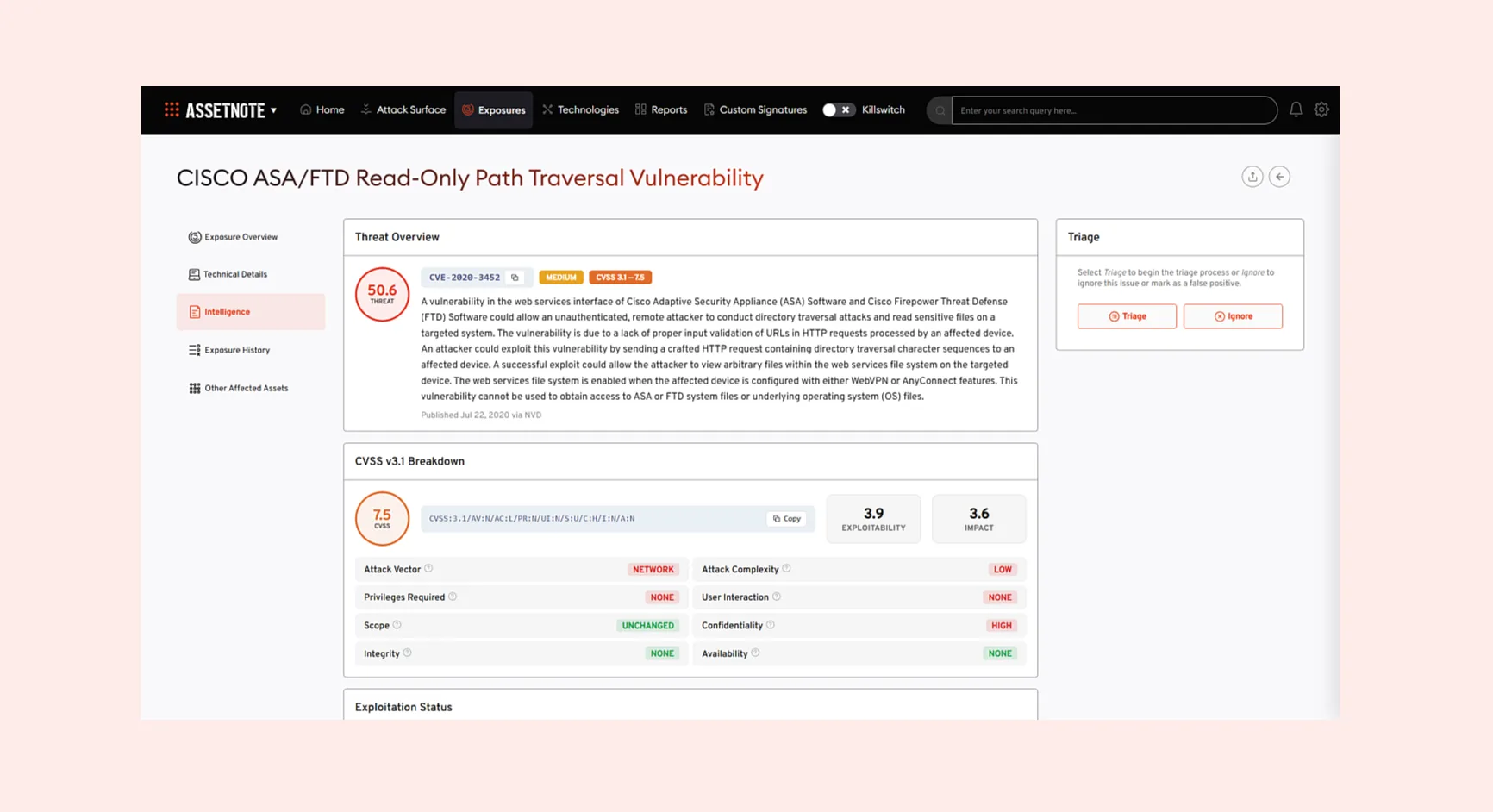
Credentials and access details: Shared login information, API keys, VPN configurations, or system documentation that could provide a route into an organization’s environment.
Internal communications: Emails or messages that reveal operational details, personnel information, or security posture relevant to your business.
Financial records: Invoices, bank details, purchase orders, or budget documents that could be used for fraud or social engineering.
The presence of any of these in a leak does not require your systems to have been touched. It only requires that your supplier holds the data.
What can cybercriminals do with that data?
Leaked data has significant downstream value, and criminal groups will exploit it well beyond the initial attack. Exposed credentials can be tested against other services through credential stuffing. Financial details enable invoice fraud and business email compromise. Personal data feeds identity theft and targeted phishing campaigns. And sensitive commercial information can be used for extortion, sold to competitors, or leveraged in follow-on attacks.
Critically, file trees from leak sites also reveal organizational structure, system names, and operational detail, intelligence that makes future attacks more targeted and more convincing. Organizations appearing in a supplier’s leaked files doesn’t just represent a historical risk, but it can represent ongoing exposure.
How do you know if you’ve been implicated?
Manually monitoring every ransomware leak site is not a practical security strategy for most organizations. Although leak data is publicly accessible, obtaining and processing the file-tree structures and data behind them is highly time-consuming, and the window to act can be short. Before having the right tooling in place, teams must manually identify the source and review ransomware files to check for any mention of their organization, a process that could take hours, with files sometimes removed from leak sites before analysis has even finished.
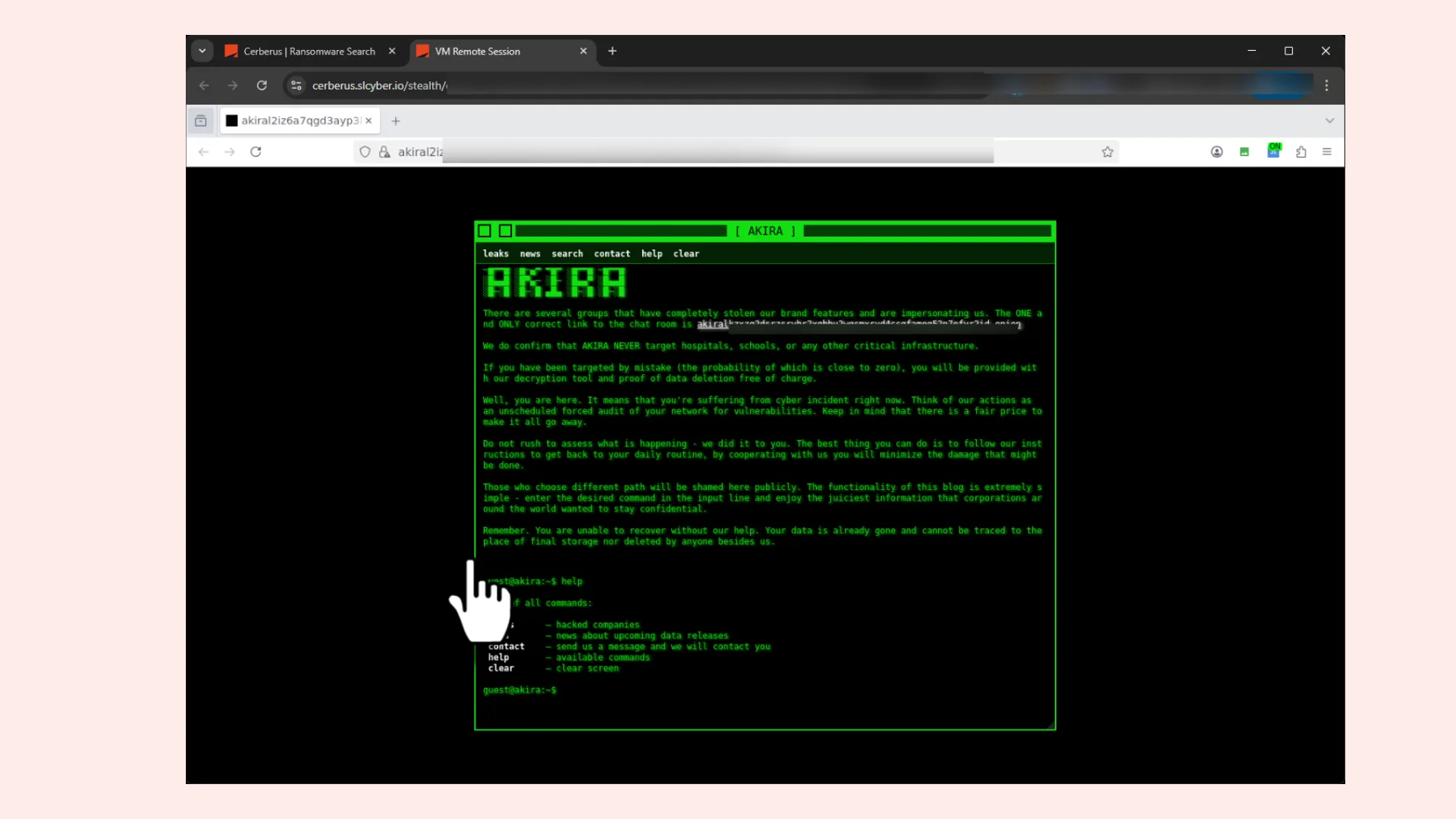
This is the visibility gap that our dark web investigation tool Cerberus’ Ransomware File Explorer is built to close. The Ransomware File Explorer securely downloads and indexes ransomware leak-site file-tree data into Cerberus, enabling preemptive detection of compromised files and accelerating incident response even when your organization is not the primary victim.
Using the Ransomware File Explorer teams can search and set alerts to identify file names that may contain sensitive documents, files, and intellectual property belonging to their organization. Keyword alerting can be configured around organization-specific variables, meaning teams are notified as soon as relevant material appears in newly indexed leak data, rather than discovering it days or weeks later.
Critically, Cerberus automatically gathers and indexes this information, making it searchable permanently, even if the file tree is later deleted from the dark web. That permanence matters as threat actors frequently remove leak site content, and without an indexed record, the window to identify and respond to exposure can close before most teams are even aware an incident occurred.
The practical value of this kind of early detection was demonstrated during testing, when Searchlight’s Threat Intelligence team used the Ransomware File Explorer to identify a database containing over 300GB of personal data records belonging to a major sportswear manufacturer, and preemptively alert them to the potential breach. That organization was not the primary ransomware victim, but their data was breached, and without visibility into the leaked file trees, they would not have known.
Ransomware attacks are on the rise. Don’t get caught in the blast radius
Our recent ransomware research found that not only are ransomware victims at an all time high, but the rate of growth in victims is increasing year on year faster than ever before. Criminal groups are increasingly sophisticated in their operations and indiscriminate in their targeting. Organizations with strong internal defenses are not immune, and are increasingly likely to be affected through their supply chain, not just directly.
The question security leaders need to ask is no longer just “could we withstand a ransomware attack?” rather “would we know if one of our suppliers was hit, and our data appeared in the files they leaked?” In most organizations today, the honest answer is no.
Gaining visibility into leak sites, file trees, and the data that criminal groups are actively publishing is no longer an advanced security capability. It’s a fundamental one. Because in the 2026 ransomware landscape, the blast radius is growing, and the organizations that fare best will be those who know they’re caught up in it before further damage is done.
If you want to learn more about how Cerberus and the Ransomware File Explorer can help protect your organization, FIND OUT MORE or BOOK A DEMO.
Bio
Luke Donovan is Head of Threat intelligence at Searchlight Cyber. Luke’s background is in military intelligence and security within the British Army, where he served in Afghanistan, Libya, and the Middle East, supporting counter-terrorism and narcotics efforts. He later transitioned to the cyber sector and now leads our expert team of threat intelligence analysts at Searchlight.