Many organizations naturally focus their defenses on the moment a ransomware attack hits – negotiations, backups, restoration, and business continuity. While these are essential, they are reactive.
By the time incident response and recovery plans are activated, ransomware gangs have already gained access, established persistence, and exfiltrated sensitive data. Damage has already been done.
The truth is that if your ransomware defense strategy focuses at the point of attack, you’re already behind.
How ransomware defenses start late
Ransomware is highly visible at the point of impact. Systems lock, operations halt and incident response plans jump into action – ultimately becoming a crisis. But the stages that precede encryption are a lot quieter and easier to overlook.
Security programs traditionally center on detection and response inside the network perimeter. They focus on alerts triggered by malware execution or suspicious internal activity. Before that point, however, attackers are identifying exposed services, harvesting credentials, and testing access from outside.
By the time the ransomware attack is detected, it’s a fully fledged and established foothold. This creates an imbalance where defenders optimize for containment and ransomware gangs optimize for access.
What does the ransomware chain actually look like?
Most ransomware attacks follow a similar pattern and progression:
- Reconnaissance: Threat actors scan for exposed assets, vulnerable applications, and misconfigurations.
- Initial access: Compromised credentials, unpatched vulnerabilities, or exposed remote services provide initial access to threat actors who then go on to perform ransomware attacks.
- Persistence and privilege escalation: Attackers embed themselves and expand control.
- Lateral movement: Critical systems and data stores are identified.
- Data exfiltration: Sensitive data is staged and stolen.
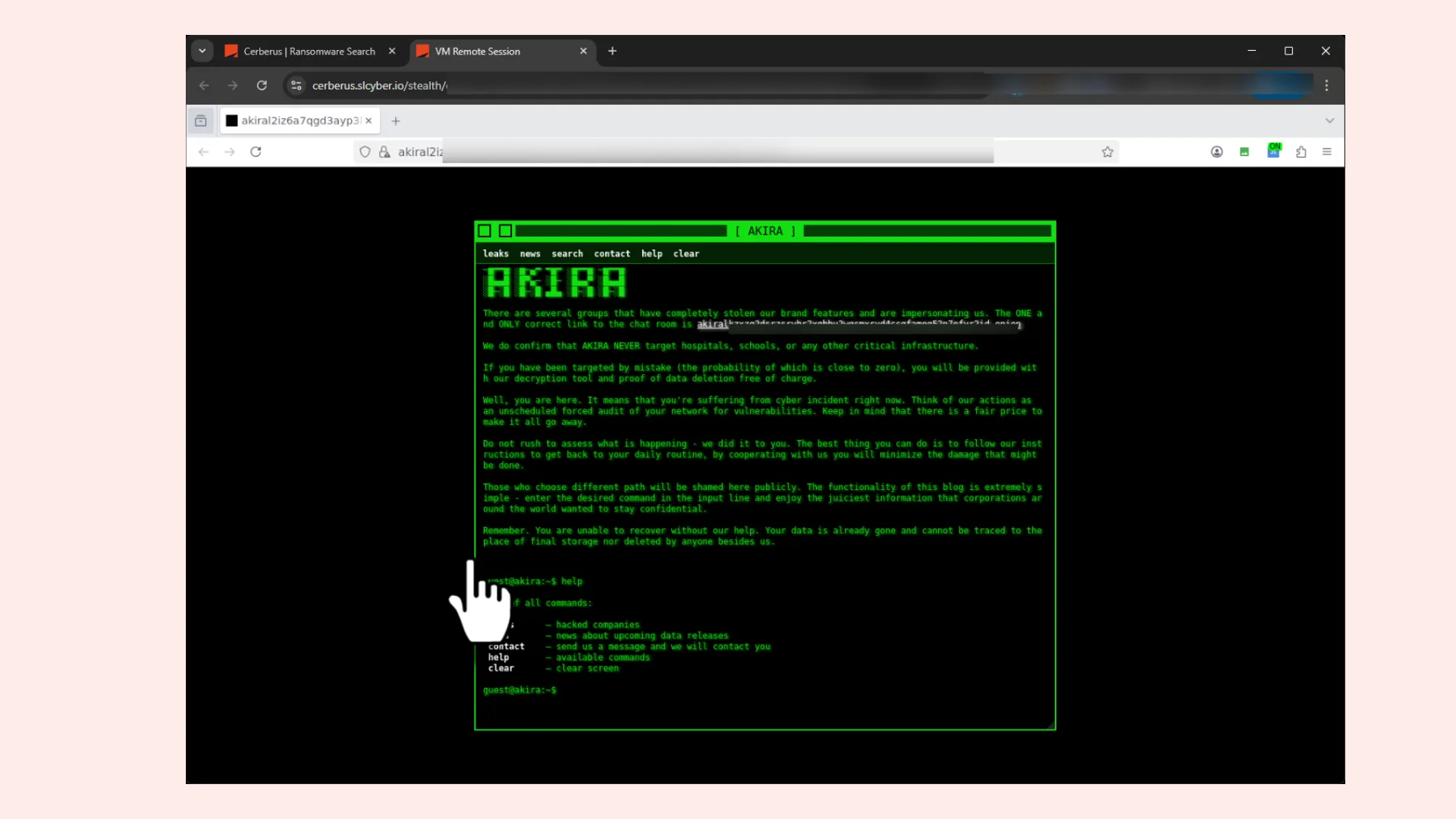
- Encryption and extortion: The final leverage is applied. But it may not just stop here, because attackers can use multiple extortion to maximize the likelihood of payment, often making traditional backup-and-restore strategies insufficient.
The ransomware attack itself is the headline but it’s the last step in a long chain of opportunity. Organizations that only invest in response capabilities are effectively preparing for stage six, when the early stages provide a golden opportunity for disruption.
Where ransomware actually begins
Ransomware begins with exposure. Exposed RDP ports, misconfigured cloud storage, forgotten subdomains, leaked credentials circulating in dark web forums, and vulnerabilities disclosed weeks ago but still unpatched.
These are not sophisticated zero-day exploits, they are weaknesses that are visible from the outside.
Attackers operate at scale and automate reconnaissance across thousands of organizations simultaneously. They do not need to target you specifically, they only need to discover that your environment presents an opportunity and open door.
This is where many defenses fall short. Internal asset inventories rarely reflect the true external attack surface and shadow IT proliferates. Cloud deployments expand rapidly, third-party integrations create new pathways, making the digital pathway grow faster than security visibility.
If you can’t see what attackers see, you can’t meaningfully reduce risk.
How early visibility disrupts ransomware operations
The most effective way to stop ransomware is not to improve recovery speed, but to reduce the number of viable entry points.
Continuous exposure monitoring enables organizations to identify exposed assets as soon as they appear. Vulnerability insights allows security teams to prioritize real-world flaws actively being exploited by ransomware groups and credential monitoring reveals potential compromise before it’s weaponized.
When exposure is detected and remediated quickly, attackers are forced to move on. This “shift left” approach disrupts ransomware at the reconnaissance and initial access stages. Instead of containing damage after impact, organizations deny adversaries the opportunity to establish a foothold in the first place.
Even if initial access occurs, early detection of suspicious activity, such as authentication attempts or unexpected external communication, limits the attacker’s ability to escalate privileges or exfiltrate data.
In practical terms, early visibility shortens the attack lifecycle, removing time and time is the attackers greatest advantage.
The role of threat intelligence
Thousands of vulnerabilities are disclosed each year, but only a fraction are actively exploited by ransomware operators. Similarly, not every leaked credential will be used in a targeted campaign.
Threat intelligence provides the context required to prioritize effectively.
By tracking ransomware groups, their preferred access vectors, and their targeting patterns, organizations can align remediation efforts with real-world threat activity. If a group is exploiting a specific VPN vulnerability at scale, that issue becomes urgent. If initial access brokers are selling credentials tied to your domain, investigation becomes immediate. Threat intelligence turns a broad exposure management strategy into a focused defensive posture.
Instead of reacting to incidents, organizations can anticipate them.
Why shifting left is now a requirement
For years ransomware and cybersecurity resilience has centered on recovery, backups, incident response playbooks, and negotiation strategies. These remain essential components of cyber resilience, but resilience without prevention is incomplete.
The financial and operational impact of ransomware extends beyond downtime. Data exfiltration introduces regulatory exposure and reputational damage. Public disclosure erodes trust and repeated incidents signal systemic weaknesses.
As ransomware groups professionalize and industrialize their operations, defenders must do the same. Shifting left is not a theoretical concept, it’s a strategic necessity:
- Continuously mapping and monitoring the attack surface.
- Identifying and remediating exposed assets quickly.
- Tracking credential leaks and initial access activity.
- Aligning vulnerability prioritization with active threat campaigns.
- Detecting early-stage attacker behavior before escalation.
This approach reframes ransomware defense from crisis management to risk reduction.
Recovery answers the question “How quickly can we bounce back?” but prevention answers the more important one “How do we stop this from happening at all?”
The organizations that will outpace ransomware are not those that recover fastest after encryption, but those that make encryption difficult enough to achieve in the first place.
Ransomware is not inevitable. But exposure left unmanagement makes it more predictable.
To learn more about the ransomware landscape and how organizations can use dark web data to preempt ransomware attacks, download our new ransomware report.
Bio
Luke Donovan is Head of Threat intelligence at Searchlight Cyber. Luke’s background is in military intelligence and security within the British Army, where he served in Afghanistan, Libya, and the Middle East, supporting counter-terrorism and narcotics efforts. He later transitioned to the cyber sector and now leads our expert team of threat intelligence analysts at Searchlight.