Already in 2026, the gap between vulnerability disclosure and confirmed exploitation has reduced from a week to a single day. The majority of exploited vulnerabilities are being weaponized before they are even publicly disclosed. Attackers are now operating with very few constraints to their ability to find novel attack vectors and weaponize them within hours.
This is the reality of the real-time era of cybersecurity, which requires a fundamental shift in how most organizations think about their security posture. For years security teams have focused on closing the gap between breach detection and remediation. The new gap to worry about is the exposure window, and making sure you close it before attackers do.
Preemptive Threat Exposure Management (PTEM) was built to close that gap.
The Macro Shift: From Reactive to Preemptive
The cybersecurity industry is undergoing a structural transformation, driven by three converging pressures that have made traditional, reactive security programs no longer fit for purpose:
1. The speed of exploitation
Exploitation timelines have collapsed. Threat actors now weaponize newly discovered vulnerabilities within hours of publication, and in many cases before they have even been made public. Security teams that once had weeks to assess, prioritize, and patch are now operating in a window measured in hours. Patch-and-respond was never designed for this pace, and the gap between exposure and exploitation continues to shrink.
2. The expanding attack surface
The external attack surface has expanded beyond what most organizations can see, let alone manage. Cloud adoption, SaaS proliferation, shadow IT, and an increasingly interconnected supply chain mean that the traditional network perimeter has dissolved entirely. Assets are being spun up and decommissioned constantly, third-party dependencies introduce exposures outside direct control, and forgotten or misconfigured infrastructure routinely becomes an attacker’s entry point. As more assets are discovered, organizations are faced with a dizzying backlog of issues that all need to be addressed.
3. The Threat Intelligence Problem
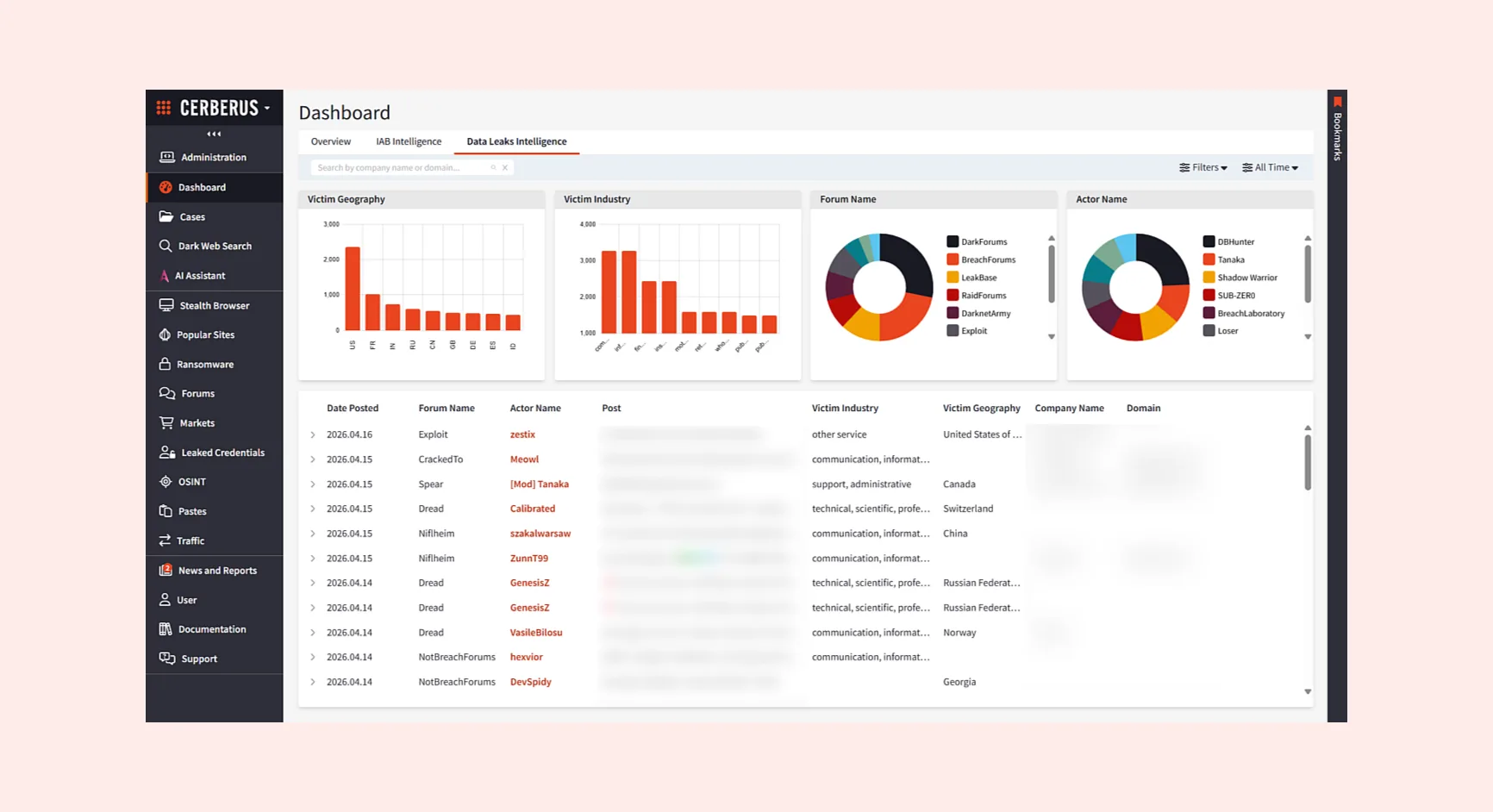
Most security programs optimize for what may be vulnerable, not what attackers are actually targeting. This is perhaps the most consequential gap of all. Cybercriminals conduct extended reconnaissance, discuss targets, and trade access on dark web forums. They share exploit code, sell stolen credentials, and signal intent well before a campaign launches. Defenders operating without visibility into these channels are making prioritization decisions blind.
The cumulative result is that defenders are perpetually operating behind attacker decision cycles. The industry’s answer has been a fundamental paradigm shift: from periodic, asset-centric vulnerability management to continuous, adversary-informed exposure management. Truly preemptive security was previously an ambitious goal for most organizations, but now it has become imperative.
What is Preemptive Exposure Management (PEM)?
Gartner formally crystallized this shift with its June 2025 research on Preemptive Exposure Management (PEM), positioning it as the evolution of Continuous Threat Exposure Management (CTEM), and one of the most significant emerging frameworks in enterprise security.
CTEM itself was already named a Gartner Top Strategic Technology Trend, built around a five-stage framework: Scoping, Discovery, Prioritization, Validation, and Mobilization. Its core principle was straightforward but powerful: continuously identify and validate which exposures are actually exploitable, not just theoretically risky, and focus remediation effort accordingly. Gartner research suggested that organizations aligning their security investments to a CTEM program would be three times less likely to suffer a breach.
Where CTEM introduced the principle of continuous discovery and validation, PEM introduces the principle of prediction and prevention; using AI, intelligent attack simulation, and automated red teaming to anticipate how attackers will move through an environment before they get the chance. Rather than waiting for an intrusion to detect attacker behavior, PEM simulates it: modelling attack paths, validating choke points, and identifying which exposures present the most realistic routes to critical assets.
This is a genuine leap over reactive vulnerability management. And while simulating attacker behavior may be a sufficient proxy for understanding attacker intent, what if the actual attacker activity was visible in real-time to inform your preemptive cybersecurity strategy?
The Missing “T”: Why Real Threat Context Changes Everything
Most PEM approaches answer one question: “Could an attacker exploit this?” They do so by simulating attacker behavior; running automated attack paths, modelling adversary techniques, and validating exploitability. That is enormously valuable. But it is still a model of attacker capability, not a window into attacker intent.
Preemptive Threat Exposure Management answers a more urgent question: “Is an attacker actually targeting this right now?”
That single word, Threat, represents a shift in how exposure prioritization works. And it is the reason Searchlight Cyber adds the T.
Searchlight Cyber brings together two capabilities that, individually, are best-in-class, and together, are uniquely powerful. Our Attack Surface Management (ASM) platform continuously maps your external attack surface, discovering and monitoring every internet-facing asset across your known and unknown infrastructure. And our threat intelligence platform, one of the most comprehensive in the industry, monitors the clear, deep and dark web, including the closed cybercriminal forums, chats and marketplaces where attacker activity affecting your organization can be observed long before an attack is launched.
The difference this creates in practice is significant. Consider two scenarios:
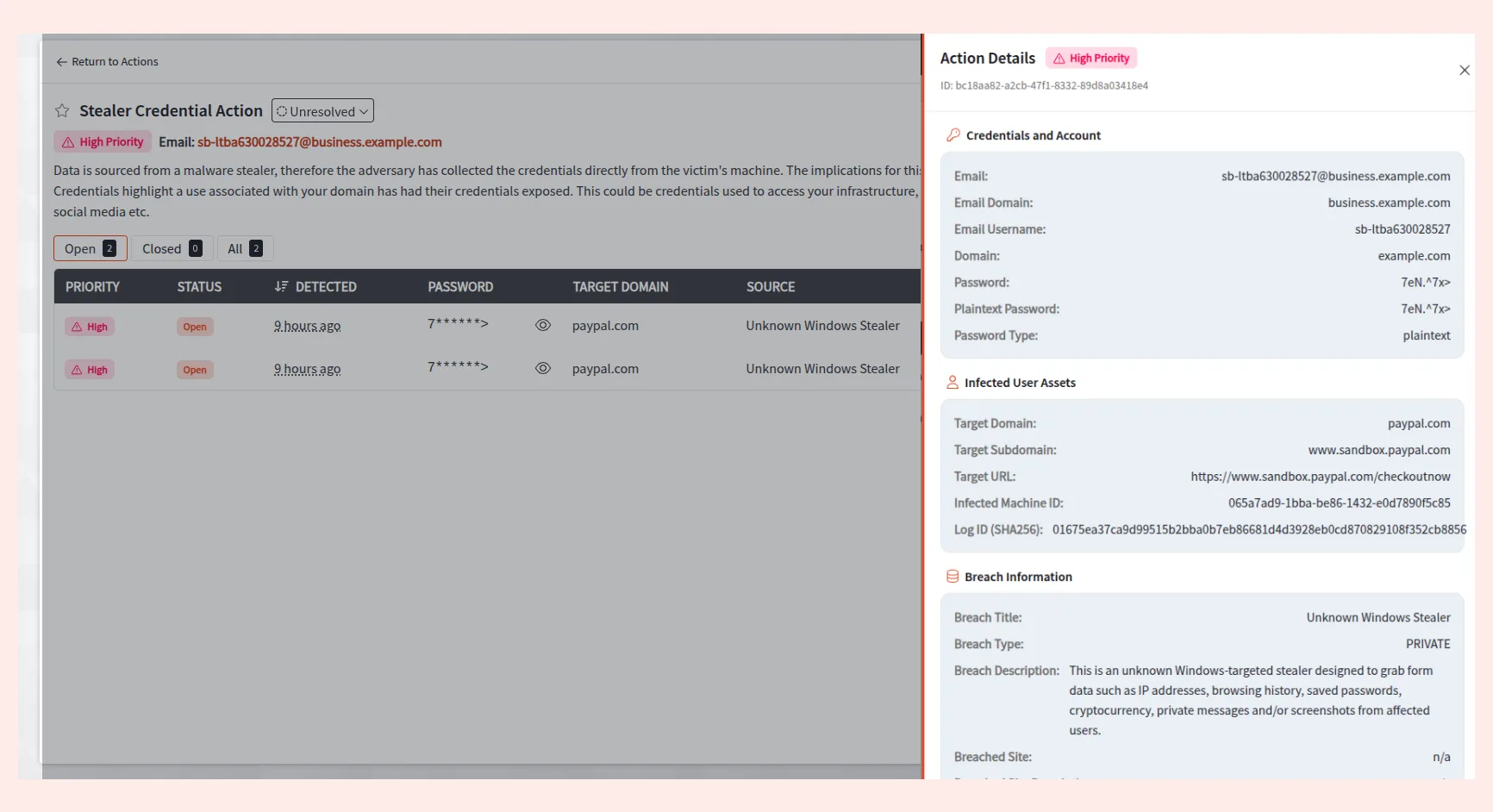
A standard ASM platform scans your environment, identifies an exposed RDP service on a legacy server, and flags it as a high-severity finding based on CVSS score and proof of exploitability. It is on a list of hundreds of similar findings awaiting remediation.
A PTEM approach starts in the same way, but it also surfaces intelligence from a dark web forum where a threat actor has posted that they hold valid credentials for a VPN endpoint at an organization matching yours, perhaps even naming your company explicitly, and signalling intent to monetize access. Suddenly, that exposed server goes from being one of hundreds of abstract vulnerabilities to the most important thing your security team works on today.
This is the operational difference when factoring in real attacker activity. PEM gives you a model of the threat. PTEM gives you the threat itself.
The Industry Direction
Gartner’s framing of PEM as a strategic priority reflects a broader industry consensus that has been building for several years: exposure management must be continuous, intelligence-driven, and oriented around the adversary’s perspective.
The industry is converging on preemptive, AI-augmented, continuously validated exposure management as the standard operating model for mature security organizations.
Where we believe PEM is evolving is through the role of real-world threat intelligence as a prioritization layer. Most vendors entering the PEM space are doing so through the lens of attack simulation: automated red teaming, AI-driven attack path modelling, and breach and attack simulation (BAS). These are legitimate and valuable capabilities.
But when attacker intent is directly observable, through dark web monitoring, real time intelligence into closed cybercriminal forums, and dark web traffic analysis, this is a critical source of context for exposure prioritization. PTEM is about combining the best of both worlds: simulated and real-world attacker perspective, unified into a single exposure management workflow.
Preemptive cybersecurity has been Searchlight’s driving philosophy from the beginning. The capabilities needed to make preemptive security a reality are here already.
How PTEM Works: The Searchlight Cyber Approach
Searchlight Cyber’s PTEM offering operationalizes this through three integrated stages:
1. Attack Surface Visibility (ASM)
Our ASM platform continuously maps your external attack surface, cataloguing internet-facing assets, subdomains, exposed services, cloud infrastructure, and third-party exposure across your ecosystem. This goes beyond known asset inventories to surface shadow IT, decommissioned but still-active infrastructure, and newly exposed assets that appear on an hourly basis. Our approach to ASM also provides the next critical step in exposure validation and prioritization. It doesn’t just discover vulnerabilities, it proves they’re exploitable before they ever become an alert. Every alert comes with a working proof-of-concept (POC), ready for your team to move straight to remediation and reduce your window of exposure.
2. Attacker Reality (Threat Intelligence)
This is what makes PTEM different. Our threat intelligence platform continuously monitors the clear, deep, and dark web for criminal activity targeting your organization. We detect, prioritize, and alert you to active threats against your organization specifically, so you can zero in on what matters and remediate risks before the attack begins. This includes compromised credentials being sold, data and access being advertised, infrastructure being profiled, and threat actor communications that indicate targeting intent. It is the layer that converts theoretical exposure into evidence-based, intelligence-backed threats for remediation.
3. Preemptive Action
ASM findings and dark web intelligence signals provide a comprehensive view of threat exposure. Rather than attempting to prioritize based on CVSS scores alone, PTEM focuses on real threats based on the intersection of exploitability and observed attacker intent. The result is a focused, actionable remediation plan anchored in what real threat actors are actually doing, not what they theoretically could do.
Remediation workflows are equipped with the full context of the threat; which actor, which campaign, what intelligence underlies the prioritization decision. This means security teams can remediate with speed and confidence, and security leaders can communicate these preemptive actions to the business in terms of real, evidenced threat activity rather than abstract risk scores.
Why PTEM is the New Gold Standard
PEM represents a genuine and important evolution in how the industry thinks about exposure management. Moving from periodic vulnerability scanning to continuous, simulation-validated exposure management is a significant step forward, and a strategic priority.
Our PTEM approach is built on the convergence of the two most powerful capabilities in modern proactive security: comprehensive external attack surface visibility, and real-world threat intelligence drawn from the environments where attackers actually operate. Together, they deliver something neither can achieve alone: the ability to see your organization through the eyes of a real adversary, acting on actual intent rather than theoretical risk.
For organizations facing sophisticated, targeted threats, ransomware operators, nation-state actors, and financially motivated initial access brokers, that is the difference between being prepared and being breached.
The industry is moving toward intelligence-driven, continuous, preemptive exposure management. Searchlight Cyber’s PTEM platform is that vision, delivered today.