What Actually Makes a Vulnerability Dangerous
Not all vulnerabilities are created equal. The fact of the matter is, your security team can’t patch everything – and they shouldn’t have to.
Traditional vulnerability management treats every high CVSS score like a five-alarm fire. Your team scrambles to patch theoretical weaknesses while actual threats slip through unnoticed.
Exploitability: The Factor that Matters
A vulnerability without working exploit code is academic. Your priority queue should start with one simple question: Can attackers actually use this weakness right now?
Vulnerabilities become genuinely dangerous when proof-of-concept code circulates publicly, or when weaponized exploits appear in active campaigns. A critical-rated vulnerability without exploit code can wait. A medium-severity flaw with reliable exploitation tools demands immediate attention.
Searchlight Cyber’s Attack Surface Management tracks exploit availability across public repositories and underground forums automatically. You’re only alerted to exposures that can actually be exploited, eliminating hours of manual research into whether working exploits exist.
Network Exposure: Location Determines Everything
A vulnerability in your internal development environment poses different risk than the same flaw in your internet-facing web server. Network position determines attacker access.
Internet-exposed assets carry higher risk than systems protected behind firewalls and network segmentation. Your DMZ web server matters more than an isolated test environment. Attack Surface Management platforms map your entire external footprint, identifying which vulnerable assets sit exposed versus those protected behind access controls.
Data Sensitivity: Know What You’re Protecting
Systems processing payment data, health records, or personally identifiable information require faster remediation. Compliance frameworks like PCI DSS and HIPAA mandate specific patching timelines based on data sensitivity.
Your vulnerability management approach must account for what each system handles. A SQL injection flaw in your customer payment portal demands different urgency than the same vulnerability in an internal wiki.
Compensating Controls: Credit Your Existing Defenses
Web application firewalls, intrusion prevention systems, and other security controls reduce exploitability. A SQL injection vulnerability behind a properly configured WAF poses less immediate risk than the same flaw in an unprotected application.
Most vulnerability scanners ignore existing defenses, flagging every potential weakness regardless of protective controls already in place. Modern tools account for your security stack before raising alarms.
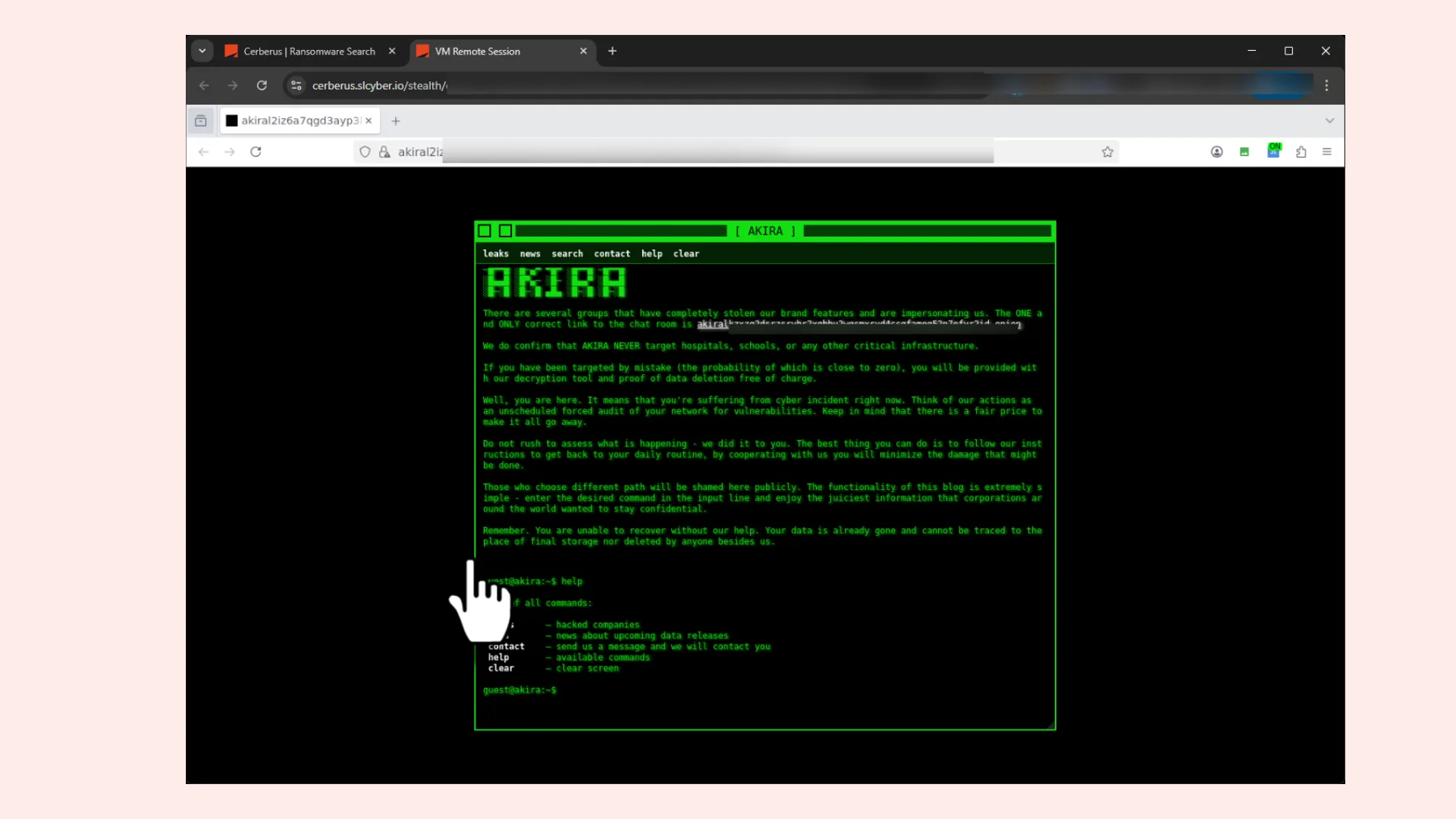
Threat Actor Patterns: Follow the Money
Attackers follow predictable patterns, targeting specific technologies during campaigns. A vulnerability actively exploited by ransomware groups demands attention, even with moderate severity scores. Weaknesses ignored by threat actors can receive lower priority despite theoretical danger.
Ransomware groups weaponizing Citrix vulnerabilities? Your Citrix infrastructure becomes priority one. Banking trojans targeting specific database versions? Those database patches move to the front of the queue.
What’s important is that your ASM takes real-time, relevant threat intelligence into account. You receive pre-filtered, pre-prioritized findings instead of raw scanner output – only vulnerabilities that genuinely threaten your environment based on actual risk calculations.