Cyber threat intelligence is the systematic process of gathering, analyzing, and applying information about cyber threats, adversaries, and their attack methods to strengthen an organization’s security defenses. It transforms raw threat data into actionable insights that help security teams detect and prepare for attacks before they happen, shifting from reactive defense to proactive threat prevention.
This blog covers everything you need to know about cyber threat intelligence. You’ll learn how CTI platforms change raw data into useful insights and discover frameworks that structure threat analysis. We’ll also explore critical questions to ask when you select a vendor to strengthen your defenses.
Key Takeaways
- Understanding cyber threat intelligence fundamentals and implementation strategies will help you transform your security operations from reactive defense to proactive threat prevention.
- CTI transforms raw threat data into actionable intelligence through a six-phase lifecycle: planning, collection, processing, analysis, dissemination, and feedback
- Four types of threat intelligence serve different audiences: strategic (executives), tactical (SOC teams), operational (incident response), and technical (automated systems)
- MITRE ATT&CK, Cyber Kill Chain, and Diamond Model frameworks provide structured approaches to analyze adversary behavior and strengthen defenses
- When selecting CTI vendors, prioritize comprehensive coverage, real-time updates, seamless tool integration, and collaborative features over basic indicator feeds
- AI-driven automation and TTP-based detection are replacing traditional IOC hunting, enabling predictive threat analysis and autonomous response capabilities
The shift toward collective defense and intelligence sharing creates stronger early warning systems, while agentic AI handles routine analysis so human analysts can focus on strategic threat hunting and complex investigations. CTI has evolved from a niche security function into a $37 billion market. State-sponsored cyberattacks surged 150% in 2025 alone, and threat actors work faster than ever. Around 30% of incidents now involve supply chain weaknesses. Your security teams need useful intelligence to preempt attacks rather than respond to them.
Understanding cyber threat intelligence fundamentals
What CTI is and why it matters
Cyber threat intelligence is the process of collecting, analyzing, and applying data on cyber threats, adversaries, and attack methodologies to strengthen your organization’s security posture. CTI platforms process raw threat data into practical insights that help you detect and prepare for threats before they materialize.
CTI transforms your security approach from reactive defense to proactive threat mitigation. You gather information about current cybersecurity threats and perform analytics on this data to learn usable intelligence that minimizes cyber risk and manages threats across attack surfaces of all types. This change matters because threat actors constantly refine their techniques. Traditional defense methods no longer provide adequate protection.
The value extends beyond detection. CTI provides context about threat actors’ motivations and methods, which helps your security teams anticipate threats, improve defense programs, and reduce potential damages while improving incident response. Organizations equipped with proper threat intelligence can allocate resources more effectively to meet the most relevant cyber threats to their industry.
Types of threat intelligence
CTI comes in four distinct categories, each serving different audiences and timeframes:
Strategic intelligence provides a high-level overview of the threat landscape for CISOs, executives, and board members. This intelligence helps decision-makers understand how threats and tactics change over time, informing risk management strategies and security investments. Strategic intelligence answers business questions about where to invest and which risks are growing over months to years.
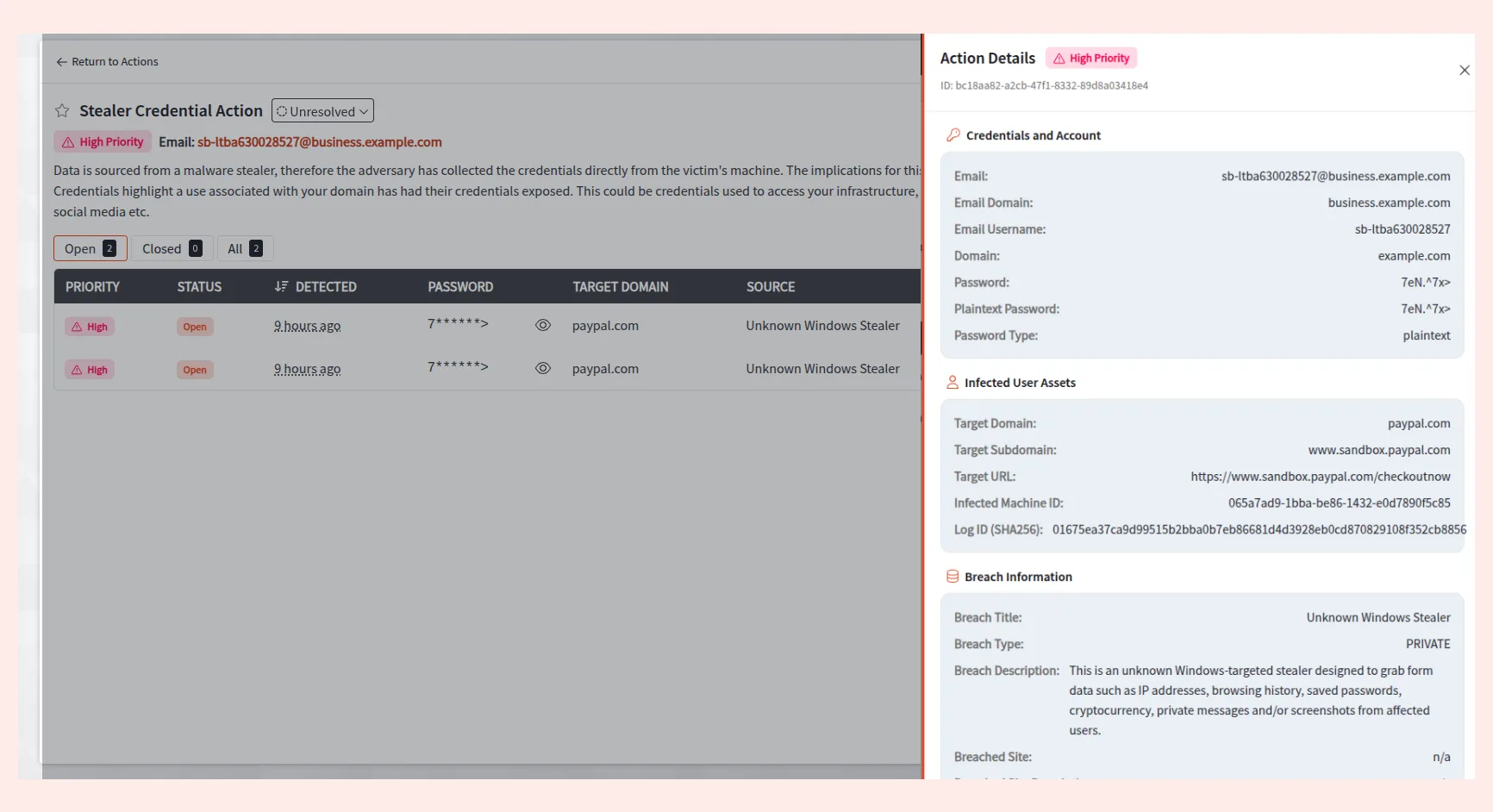
Tactical intelligence focuses on immediate indicators of compromise (IOCs) such as malicious IP addresses, URLs, file hashes, and domain names. Security operations teams and SOC analysts use this technical information to detect and respond to active threats quickly. Tactical intelligence is automated and machine-readable, meaning you can integrate it into security tools via data feeds or API integrations. This intelligence has the shortest shelf life and remains relevant for hours to days.
Operational intelligence delivers immediate information about specific attack campaigns and threat actors. It reveals the who, why, and how behind attacks by providing insights into adversary capabilities and infrastructure. SOC managers and incident response teams use operational intelligence to conduct more targeted cybersecurity operations and personalize their response strategies. Human analysis converts this data into digestible formats that remain useful for weeks to months.
Technical intelligence involves detailed analysis of threats, including malware signatures, exploit code, and network packet patterns. This granular intelligence feeds your intrusion detection systems and EDR platforms, helping you understand how to detect, analyze, and respond to threats at the technical level.
The role of CTI in modern security operations
CTI has become the backbone of effective Security Operations Centers (SOCs). Cyber threats continue to grow more sophisticated, and your SOC needs intelligence to separate benign anomalies from genuine threats. Arming your SOC and incident response teams with operational threat intelligence helps them make timely decisions to prevent system downtime, thwart data theft, and protect intellectual property.
CTI improves your security capabilities through continuous data collection and analysis. It drastically improves early detection and response times by providing immediate tracking of tactics and techniques used by known and emerging threats. Your SOC can act proactively with advanced knowledge of how threats evolve and where attackers might attempt to gain access.
You lower response times and reduce false positives by integrating threat intelligence into your security infrastructure. This allows your security team to focus on what matters. Understanding the cyber threat landscape enables you to identify the most relevant threats targeting your business and make faster decisions. Your infrastructure addresses these attack vectors effectively.
How cyber threat intelligence works
The six-phase CTI lifecycle
CTI platforms that work well operate through a structured six-phase lifecycle that refines your threat intelligence capabilities without pause. This iterative framework will give your security teams the ability to gather relevant data, transform it into usable insights, and adapt to evolving threats.
Planning and Direction: establishes your intelligence priorities by defining what assets need protection and what threats matter most to your organization. You identify Priority Intelligence Requirements (PIRs) that guide all downstream activities. This phase answers questions like which threat actors target your industry and what attack surface vulnerabilities exist in your infrastructure.
Collection: gathers raw data from multiple sources to address your defined requirements. Your teams pull information from internal network logs, security device telemetry, threat data feeds, dark web forums, and open-source intelligence. The breadth of collection matters. Too little visibility creates blind spots while unfocused data overwhelms analysts with noise.
Processing: transforms collected information into a standardized, machine-readable format. Raw data gets normalized into consistent schemas like STIX/TAXII, deduplicated to remove overlaps, and enriched with additional context from external sources. This stage converts disparate formats including XML, JSON, PDF, and CSV into usable intelligence that your security tools can consume.
Analysis: applies human expertise and analytical techniques to processed data and identifies patterns, trends, and relationships that reveal threat actor TTPs. Analysts assess the potential impact on your organization, determine likelihood of attacks, and generate practical recommendations. This phase answers your PIRs and produces finished intelligence reports.
Dissemination: delivers analyzed intelligence to the right stakeholders in appropriate formats. Technical teams receive tactical IOCs to block threats right away, while executives get strategic briefings on business risks. The intelligence flows into your SIEM, SOAR, firewalls, and EDR platforms for automated response.
Feedback: closes the loop by evaluating whether the intelligence met stakeholder needs and improved security metrics. This assessment refines future requirements and collection strategies without pause.
Data sources for detailed coverage
Detailed threat intelligence requires diverse data sources working together. Your CTI program should combine:
Internal sources: including SIEM logs, XDR telemetry, SOC team observations, and customer or supply chain data that reveal your threat exposure
Open-source intelligence (OSINT): from security blogs, news articles, social media, and public forums that provide early threat indicators
ISACs and government agencies: offering sector-specific intelligence through trusted collaboration and information sharing
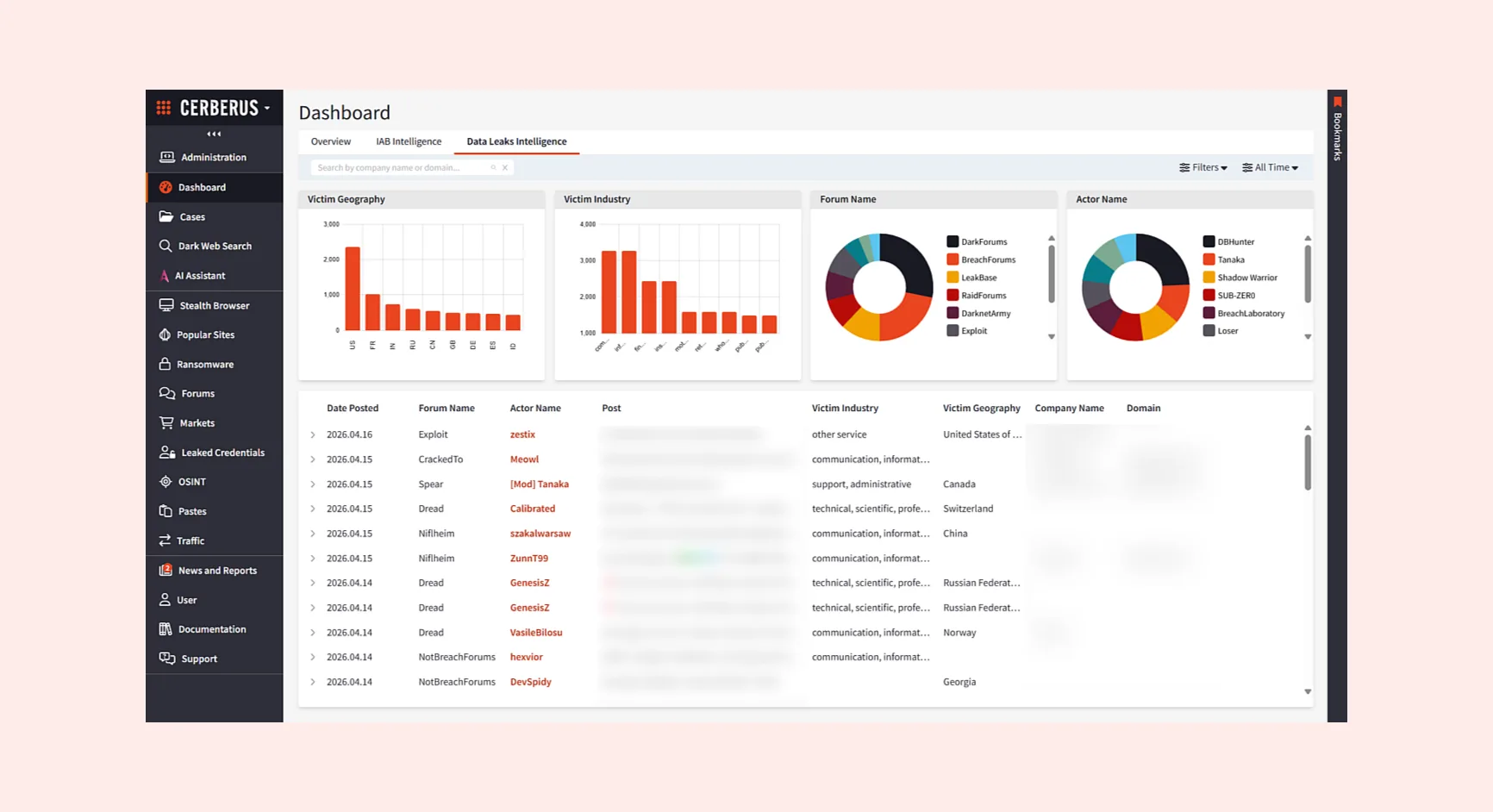
Dark web and deep web intelligence: monitoring underground forums, paste sites, and closed communities where threat actors coordinate attacks and trade stolen credentials
From raw data to practical intelligence
The transformation from raw data to practical intelligence addresses a pain point in security operations. Analysts investigate siloed alerts one by one without visibility into how incidents connect. They subscribe to generic feeds lacking context and are forced to open 20+ tabs, read through paragraphs of unstructured text, and copy-paste actor names, victim details, and CVEs into spreadsheets by hand. This process is slow and error-prone, producing incomplete pictures.
Advanced CTI platforms automate this transformation by ingesting massive volumes of data from clear, deep, and dark web sources. These systems extract, associate, and deduplicate entities like malware families, leaked credentials, CVEs, and threat actors. They turn noisy inputs into clear intelligence. Automated normalization will give you data from multiple feeds that can be compared and analyzed the same way.
Enrichment adds context by integrating with tools to provide threat actor attribution, first-seen data, and relationships among indicators. Processed intelligence pushes to your security stack for blocking, alerting, and response. This reduces Mean Time to Respond while lowering false positives. Your analysts focus on strategic analysis rather than administrative tasks, helping you preempt attacks before they materialize.
Frameworks and methodologies for CTI
MITRE ATT&CK framework
MITRE ATT&CK is a knowledge base available worldwide that documents adversary tactics and techniques drawn from ground observations. The framework organizes threat actor behavior into matrices covering Enterprise, Mobile, and ICS environments. The Enterprise Matrix alone contains 14 distinct tactics ranging from Reconnaissance through Impact.
ATT&CK stands apart because of its granular depth. Each tactic breaks down into specific techniques and sub-techniques that show exactly how attackers accomplish their goals. Initial Access has techniques like phishing and exploiting public-facing applications. Defense Evasion details 47 different techniques attackers use to avoid detection. The framework provides descriptions, mitigation strategies, and detection methods for each technique. This makes it useful for your security teams.
MITRE Corporation updates ATT&CK with input from the cybersecurity community. This ensures it reflects current threat intelligence and research. Your teams can use it to hunt threats, develop detection capabilities, simulate attacks, and create common language to share intelligence across organizations.
Cyber Kill Chain
Lockheed Martin developed the Cyber Kill Chain. It breaks cyberattacks into seven sequential stages: Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control, and Actions on Objectives. The framework assumes adversaries must progress through all phases to succeed. You only need to block them at any single stage to break the chain.
This linear approach helps you understand where attacks stand and implement targeted defenses at each phase. Improved monitoring detects information gathering attempts during Reconnaissance. Intrusion detection systems stop malicious code execution in the Exploitation phase. The model proves especially effective against advanced persistent threats where adversaries invest time in planning and surveillance.
Diamond Model of Intrusion Analysis
The Diamond Model examines intrusions through four interconnected components: Adversary, Infrastructure, Capability, and Victim. This model emphasizes relationships between elements, unlike sequential frameworks. Adversary-infrastructure relationships reveal how attackers establish operations. Victim-capability connections expose specific tactics used against targets.
This framework excels at attribution and visualizing complex attack scenarios. Analysts used the Diamond Model to examine the LAPSUS$ ransomware group. They identified the group’s infrastructure (open-source tools, Telegram, underground forums), capabilities (social engineering, DDoS attacks, credential dumping), and victims (telecommunications and technology companies).
Applying frameworks to ground threats
These frameworks work best in combination. The Cyber Kill Chain provides high-level attack progression. MITRE ATT&CK delivers granular technique details. The Diamond Model maps relationships to help with attribution. Your SOC can structure red team exercises using the Kill Chain while detecting specific ATT&CK techniques, then apply the Diamond Model for post-incident analysis and threat actor profiling.
Selecting the right cyber threat intelligence vendor
Evaluating vendor capabilities and coverage
Choosing the right CTI vendor determines whether your security team stays ahead of threats or reacts to incidents constantly. Feed coverage is the foundation of effective threat intelligence operations. Your vendor should total data from commercial providers, open-source feeds, government sharing programs like CISA, ISACs, and internal threat research [1]. Platforms that rely solely on indicators fail in sophisticated threat environments [1]. Seek solutions that integrate multiple intelligence forms and allow navigation through and distribution of data to technical and non-technical stakeholders [1].
Data collection frequency and timeliness
Timeliness separates applicable information from stale data. Determine how often vendors harvest content from sources relevant to your needs based on your requirements [2]. You need dissemination on an hourly or daily basis if you’re identifying breached credentials to prevent unauthorized access [2]. Delays increase the probability of malicious activity occurring before you can respond [2]. Up-to-the-minute alerting capabilities determine response speed to emerging threats, with platforms monitoring indicators relevant to your organization and providing notifications when new threats surface immediately [3].
Platform usability and team collaboration
A platform that delivers the best dataset becomes worthless if your team won’t use it daily [2]. Secure, well-laid-out collaboration matters because threat intelligence is a team effort. Your platform should define granular access controls for shared intelligence and support collaboration with teams, external partners, ISACs, and MSSPs [4]. Visualizations improve threat understanding, with features like ATT&CK visualizers and threat graphs that enable analysts to learn about threats quickly [5].
Integration with existing security tools
API support enables integration with your security infrastructure. Modern operations rely on automated data sharing between tools [3]. Uninterrupted connections with SIEM, SOAR, EDR, firewalls, and vulnerability management tools ensure threat intelligence flows into operational processes effectively [1][5].
Questions to ask potential CTI providers
#1 Can the vendor fulfill your intelligence gaps?
To determine if a vendor can fulfill your intelligence gaps, it’s crucial to understand your specific goals and needs. Start by asking yourself what you aim to achieve with your cyber threat model. Are there particular dark web threats targeting your industry or region that you need to combat? Are you primarily focused on protecting IP and brand reputation, or are you aiming to stop cyber attacks before they start? Once you have these answers, you’ll understand the different types of intelligence your organization needs from a vendor to answer your team’s questions.
#2 How regularly does the vendor collect data?
Based on your intelligence requirements, how often does the vendor harvest content from sources which will help you respond to the requirement? Information and intelligence gathered from the dark web needs to be timely. If you are interested in identifying breached credentials to mitigate the possibility of unauthorized access you will want this information disseminated to you rapidly, potentially on an hourly or daily basis. Delays will increase the probability of malicious activity occurring.
#3 Does the vendor have sufficient coverage of my focus area?
Every provider has a different dark web dataset, and not one dataset will likely be perfect for your needs. The needs of a company in the manufacturing sector in India for example will be very different to an American software company.
#4 How quickly is data made available?
The speed at which data is made available to your team is critical for timely threat detection and response. With that in mind, you should look for a security vendor who is able to provide you with real-time intelligence updates to avoid leaving your organization vulnerable to fast emerging threats.
#5 Is the vendor compliant with your organization’s legal requirements?
Where does the vendor host its content and services? Are they compliant from a legal, policy, and contact standpoint?
#6 Does the vendor offer access to unstructured or structured data?
There is a difference between unstructured data (information) and structured data (intelligence). Understanding whether the cyber threat intelligence provider disseminates, or makes available, information or intelligence, will impact the amount of organic processing needed and the skillset required by your team. Ask the vendor whether the information they provide makes it possible for cyber threat intelligence teams to answer the critical “So what?” question effectively.
#7 How intuitive is the tool and user experience?
You can have the best dataset in the world, however if the tool isn’t easy to use and your team won’t actively use it day in, day out then you’ll be wasting valuable time and resource. To counter the risk of purchasing a tool that nobody uses and doesn’t get renewed after a year, ask the vendor if they offer a trial period to gather feedback from other key stakeholders and users within your organization.
#8 Does the vendor’s platform allow users to collaborate?
To fulfill your intelligence requirements, you will likely need to gather information from various sources – some in-house and some from your vendor(s). Ideally, you want to visualize all this dark web data in a single view. Depending on the size and structure of your company, you may not have a tool to consolidate all of the information you’re collecting. That’s why the ability to add comments, assessments, or recommendations to harvested dark web information can be useful. Lastly, the ability to assign or prioritize harvested content among your team will enable better management of your data.
#9 What format is the intelligence provided in?
Many cyber threat intelligence providers deliver their intelligence in the form of static reports. The challenge with these reports is that they’re out of date the minute they’re published, not to mention they can be hard to integrate into your other systems. Additional questions you should ask are whether the vendor offers access to an online portal, platform, or access via native integrations or an API.
#10 How open is the vendor to accepting data source requests?
There will be times when new data sources emerge or a source which you feel will be beneficial to answering your requirements. Intelligence is only ever going to be as good as the information which feeds it. Is the vendor willing to accept data collection requests, or are you going to be stuck with the ones on initial offer?
The future of CTI: trends shaping 2026
Agentic AI and automated threat response
AI has become the most important driver of change in cybersecurity. Survey respondents identified it as the main force shaping defense strategies, with 94% agreement[7]. Agentic AI systems act autonomously and understand context. They make decisions and respond to threats without human intervention. These systems don’t just support analysts.
The systems filter alerts and prioritize incidents. They investigate threats without human help, while human analysts focus on strategic thinking and complex investigations that require business context.
This move creates collaborative SOCs where AI handles large-scale data correlation and repetitive response steps. The systems maintain consistent pattern analysis across millions of events without fatigue. Humans confirm findings and refine strategies. They make decisions about response severity. AI-native systems draft incident summaries and cluster related events. They surface likely root causes for analyst confirmation.
Collective defense and intelligence sharing
Cyber threat actors work together across borders and share tools and tactics to scale attacks. Collective defense counters this by uniting organizations across sectors through transparent communication. Communities that openly exchange threat intelligence detect threats faster and respond with greater confidence. Shared indicators of compromise and attack pattern analysis strengthen early warning capabilities. Organizations learn about emerging threats through these exchanges.
TTP-based detection over IOCs
Behavioral detection outperforms traditional indicator hunting because TTPs represent core adversary strategies. These strategies are harder to modify than surface-level elements like IP addresses or file hashes. The Pyramid of Pain model places TTPs at the top—disrupting them forces adversaries to change entire strategies. Behavioral detection recognizes activity patterns like privilege escalation and lateral movement before encryption occurs. This enhances precision and minimizes false positives.
Predictive adversary behavior analysis
Predictive systems analyze behavioral patterns to forecast attacker activity and stop threats early. AI maps activity to known attack techniques and progression paths. The systems show what attackers will do next. Risk levels update as behavior changes, and defenses escalate before damage occurs. Healthcare providers using predictive models have identified ransomware campaigns during reconnaissance. They prevented encryption events that could disrupt patient care.
Conclusion
Cyber threat intelligence has transformed from reactive monitoring into proactive defense that stops attacks before they materialize. Threat actors accelerate their campaigns and supply chain vulnerabilities expand your attack surface. Useful CTI provides the context your security teams need to anticipate threats rather than simply respond to them.
Prioritize platforms that deliver detailed coverage, immediate updates, and uninterrupted integration with your existing security stack as you select a CTI vendor. Review data collection depth and automated enrichment capabilities. Shared features strengthen your SOC’s efficiency.
The right intelligence partner and frameworks give you the ability to move from playing catch-up to being proactive against adversaries that target your organization.
To learn more about CTI and how it can help your organization to understand, detect threat actors, and preempt cyberattacks before they happen, book a demo.
There are four primary types: Strategic intelligence provides high-level threat landscape overviews for executives and decision-makers; Tactical intelligence focuses on immediate indicators like malicious IPs and file hashes for quick detection; Operational intelligence delivers real-time information about specific attack campaigns and threat actor behaviors; and Technical intelligence involves detailed analysis of malware signatures and exploit code for automated defense systems.
Behavioral detection focuses on tactics, techniques, and procedures (TTPs) that represent core adversary strategies, which are much harder for attackers to change than surface-level elements like IP addresses or file hashes. This approach recognizes activity patterns such as privilege escalation and lateral movement before damage occurs, providing better precision and fewer false positives compared to traditional indicator-based detection.