This week’s cybersecurity and dark web news stories discuss ShinyHunters claiming responsiblity for data breach, critical cPanel vulnerability identified, and Akira ransomware being responsible for nearly 50% of cyber insurance claims.
Canvas Breach Exposes Millions of Students as ShinyHunters Claims Attack
Instructure, the company behind the widely used Canvas learning management system, has confirmed a data breach affecting users across thousands of schools and universities worldwide.
The attack was disclosed on April 30 and caused disruption to API-dependent tools. By May 3, Instructure had contained the incident and restored access to its Canvas Data 2 platform. The company confirmed that the exposed data includes names, email addresses, student ID numbers, and messages between users – though it states there is no evidence passwords, financial information, or government identifiers were compromised.
The ShinyHunters extortion group has claimed responsibility, alleging nearly 9,000 schools worldwide were affected and that data belonging to 275 million individuals — including students, teachers, and staff – was stolen, along with private messages. The group also claims Instructure’s Salesforce instance was compromised and says it holds 3.65 terabytes of stolen data.
ShinyHunters warned Instructure to make contact by May 6 or face a public data leak, along with “several annoying digital problems.” Experts have noted the attack follows a pattern of targeting third-party vendors rather than individual institutions, allowing attackers to reach thousands of schools through a single compromise.
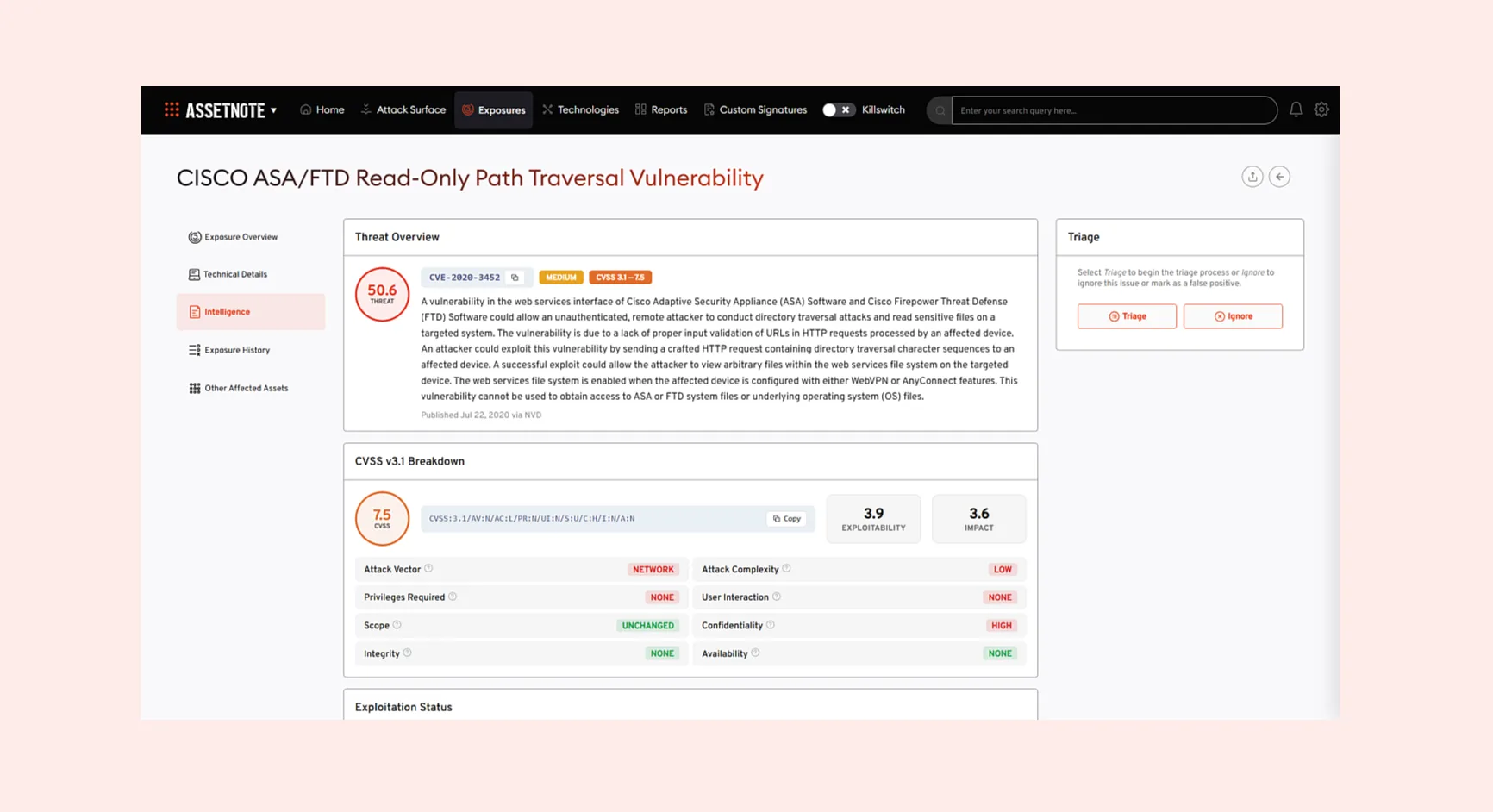
Critical cPanel Flaw Weaponised Against Government and MSP Networks
A critical authentication bypass vulnerability in cPanel is being actively exploited by an unknown threat actor targeting government, military, and managed service provider networks across Southeast Asia and beyond.
The activity, detected by Ctrl-Alt-Intel on May 2, involves the abuse of CVE-2026-41940, a flaw in cPanel and WebHost Manager (WHM) that can allow remote attackers to bypass authentication and gain elevated control of the control panel.
Attacks have originated from a single IP address and focused primarily on government and military domains in the Philippines and Laos, as well as MSPs and hosting providers in Canada, South Africa, and the US, using publicly available proof-of-concept exploits.
The threat actor is also using the AdapdixC2 command-and-control framework alongside tools such as OpenVPN and Ligolo to maintain persistent access and pivot into internal networks. Researchers noted that the attacker exfiltrated a substantial volume of Chinese railway-sector documents from one victim.
Separately, Censys found evidence the vulnerability was being weaponised by multiple parties within 24 hours of public disclosure, including deployments of Mirai botnet variants and a ransomware strain called Sorry. The Shadowserver Foundation recorded around 44,000 compromised IP addresses conducting scanning and brute-force attacks on April 30, a figure that had dropped to roughly 3,500 by May 3.
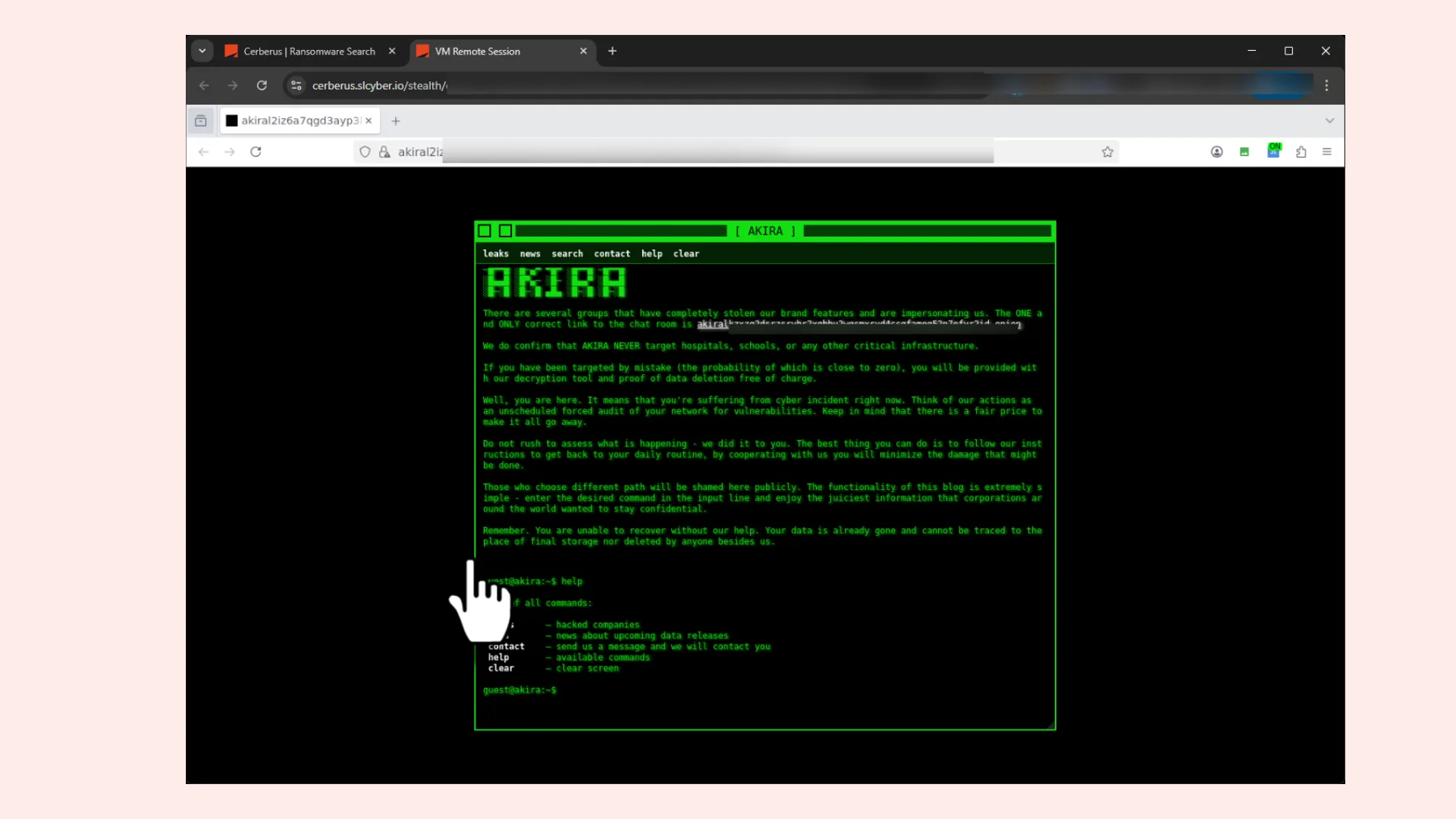
One Ransomware Gang Now Behind Half of All Cyber Insurance Claims
A single ransomware group exploiting a single firewall brand is now responsible for nearly half of all cyber insurance claims, according to a major new industry report.
At-Bay’s 2026 InsurSec Report, drawn from more than 6,500 claims and 100,000 policy years, concludes that ransomware has entered an infrastructure-driven phase – attackers are no longer hunting by industry or company size, but by the network appliances their targets run.
The Akira ransomware group accounted for more than 40% of ransomware claims – the highest concentration of any single strain on At-Bay’s books – with SonicWall appliances present in 86% of its attacks. SonicWall topped the list of most-targeted VPNs for the first time, linked to 27% of ransomware claims overall. Akira’s average ransom demand reached $1.2 million.
Small businesses are bearing the brunt of the surge. Companies under $25 million in revenue saw claim frequency jump 21% and severity surge 40% to $422,000. Average ransomware claim severity rose 16% overall to $508,000.
Perhaps the most striking finding for security buyers: 60% of Akira victims had endpoint detection and response tools deployed and were still breached. Only organisations pairing EDR with round-the-clock managed detection and response escaped full encryption. On a more positive note, ransom payments were avoided in 68% of cases, and where paid, final figures came in 62% below initial demands.