In this blog we explore the exponential gap between the expansion of an organization’s attack surface and the limited capacity of its security team to keep pace.
Ask any CISO how their attack surface has changed in the last three years. The honest answer is always some version of the same thing: it has exploded.
The perimeter that once only included a firewall, a datacenter, and a known set of devices no longer exists. In its place is a sprawling, dynamic, and often obscured landscape of cloud assets, SaaS applications, remote endpoints, third-party APIs, and shadow IT that expands faster than any team can track manually.
This is not a failure of security teams. It is a structural problem that comes with the pace of modern digital transformation. And until organizations accept that reality, their security strategies will remain permanently on the back foot.
How have attack surfaces grown?
Consider what a typical organization adds to its environment:
- Dozens of new cloud workloads spun up by development teams, many without security review.
- New SaaS applications approved through business units, bypassing IT.
- Thousands of new API endpoints exposed as microservices proliferate.
- An expanding list of third-party vendors, each carrying their own attack surface into your supply chain.
- New remote or hybrid employees connecting from unmanaged devices on unsecured networks.
Against this backdrop, the average security team has grown by a fraction of the rate. And the tools teams rely on, largely built for the old perimeter model, are not designed to handle this level of distributed exposure.
What is Attack Surface Management and why is it critical now?
Attack Surface Management (ASM) is the continuous process of discovering and prioritising every internet-facing asset an organization owns or operates, including those it doesn’t know about.
The word continuous is critical. Traditional vulnerability management operates on a point-in-time basis: scan, report, remediate, repeat. But in an environment where new assets are being created daily, a scan from last month tells you almost nothing about your current exposure. By the time you act on it, the environment has changed dramatically.
ASM approaches this differently. Rather than scheduled assessments, continuous ASM monitors your external attack surface continuously, flagging new exposures, misconfigurations, and shadow assets in real time. It answers the question attackers are already asking: “What can I see, and what can I exploit?”
How are attack surfaces expanding?
Cloud Adoption and Multi-Cloud Sprawl
Cloud infrastructure has fundamentally changed the speed at which new assets come online. In a traditional data centre, provisioning a new server took days and required change management approval. In the likes of AWS or Azure, a developer can spin up a new workload in minutes, often without security involvement.
The result is an asset inventory that changes faster than any manual process can track. Misconfigured buckets, exposed cloud storage, publicly accessible databases, and forgotten test environments are among the most common entry points attackers exploit today, and they are almost always the result of cloud sprawl without adequate visibility.
SaaS Proliferation and Shadow IT
The average enterprise now uses over 50 SaaS applications. Many are sanctioned and managed, but many more are not. Employees routinely adopt tools without IT approval. Everything from collaboration platforms to file sharing services to AI writing assistants, which all represent a potential data exposure or account compromise risk.
Shadow IT is not a new problem, but its scale is new. And unlike legacy shadow IT challenges, today’s unsanctioned tools often integrate deeply with core business data, creating exposure pathways that are difficult to detect without dedicated ASM tooling.
Third-Party and Supply Chain Risk
Your attack surface does not end at your own infrastructure. Every vendor, partner, and supplier with access to your systems or data extends your exposure. The SolarWinds, MOVEit, and Log4Shell incidents were reminders that attackers are well aware of this and actively exploit third-party pathways to reach well-defended targets.
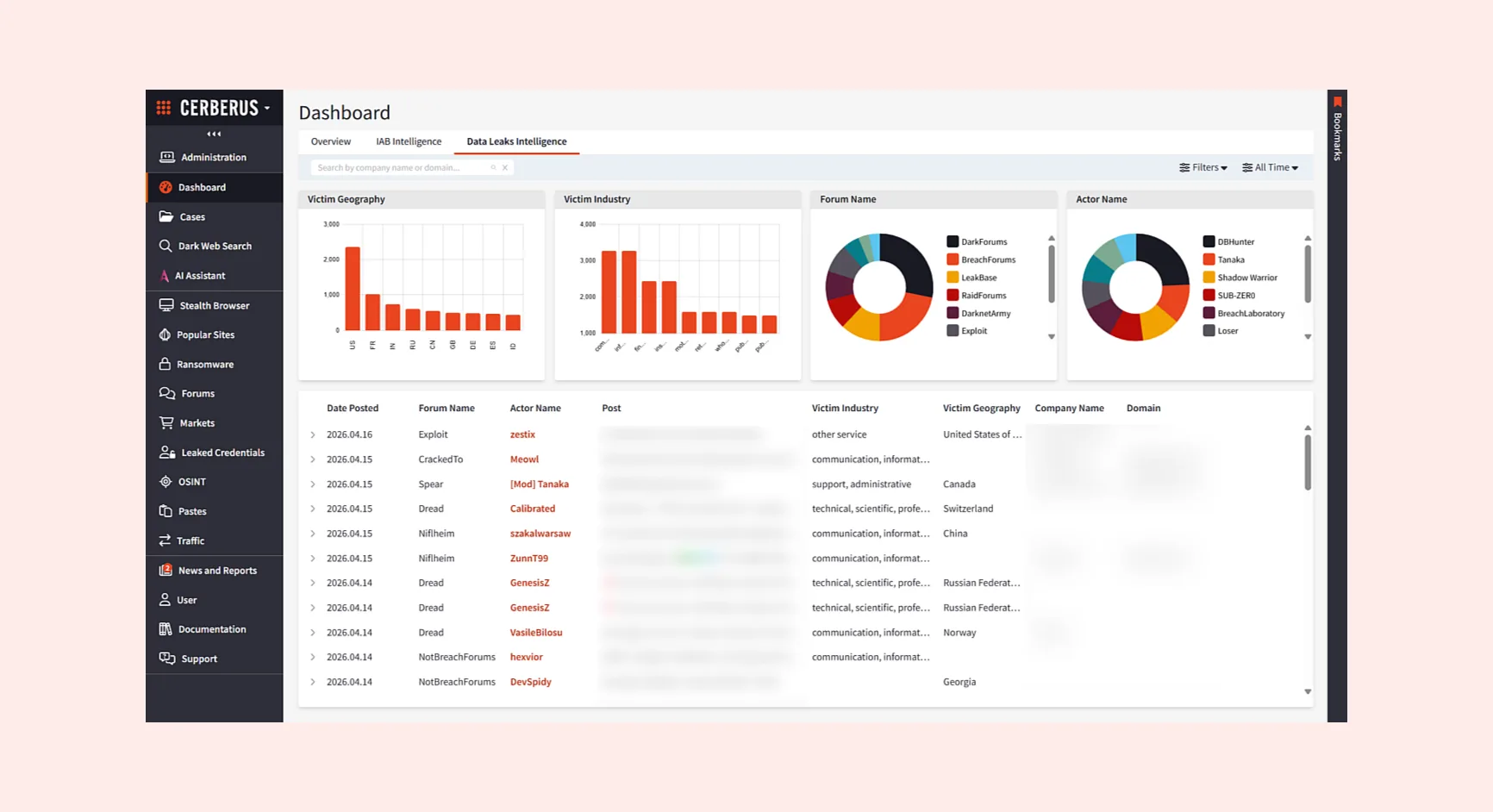
Most organizations have limited visibility into the security posture of their supply chain. Yet a compromise at a payroll provider, a logistics partner, or a niche software vendor can be as damaging as a direct attack. In addition to shadow IT; the assets you don’t know about, organizations need to gain control over ‘shadow exposure’: the hidden, unmanaged, or poorly understood security risks inherent in known and authorized third-party software and enterprise systems.
Remote Work and Endpoint Proliferation
The shift to hybrid work permanently expanded the attack surface in ways many organizations have not fully reckoned with. Employees now connect from home networks, personal devices, and public Wi-Fi, each of which introduces risk that did not exist in an office-first model.
VPN infrastructure, remote desktop services, and web-facing authentication portals have all become high-value targets. The attack surface now includes not just your systems, but the network paths through which your employees connect to them.
What does good ASM look like?
Effective Attack Surface Management gives security teams continuous, accurate visibility into everything exposed externally, with enough context to prioritise action intelligently.
The core components of a mature ASM program are:
- Continuous external asset discovery: Automated identification of all internet-facing assets, including unknown and shadow assets, refreshed in near-real time.
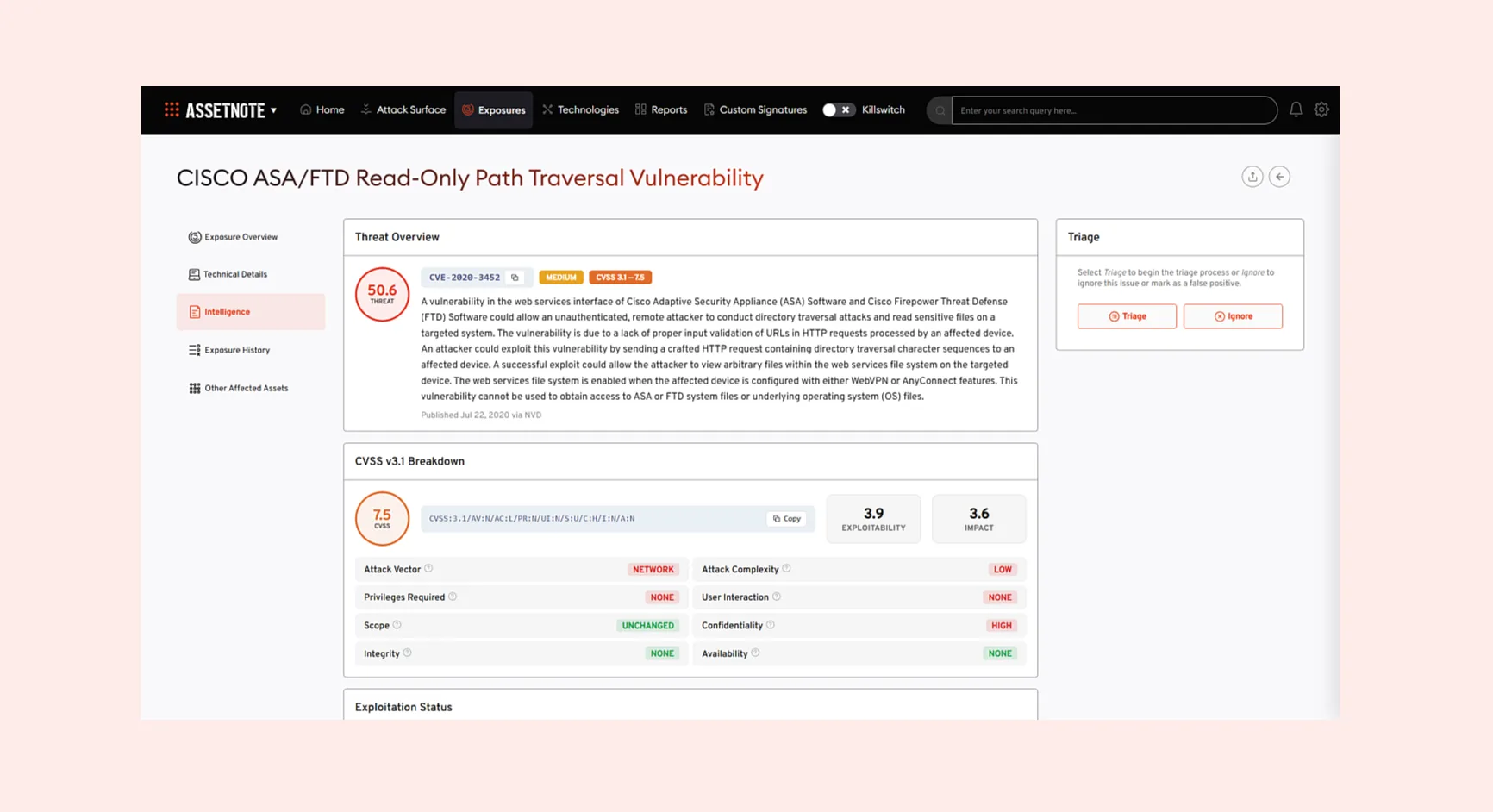
- Risk-based prioritization:Not just flagging exposures, but prioritizing them based on exploitability, asset criticality, and the context of real attacker activity, so teams focus effort where it matters most.
- Integration with vulnerability management: Connecting ASM data to remediation workflows so findings translate into action, not just reports.
- Third-party monitoring: Extending visibility beyond your own perimeter to track the security posture of key suppliers and partners.
- Attack path analysis: Modelling how discovered exposures could be chained together to reach critical assets, helping prioritize based on actual risk rather than theoretical severity.
Shifting to preemptive cyber defense
The traditional defensive perimeter is gone, replaced by a dynamic, complex attack surface that grows faster than any manual effort can track. This is why ASM is no longer optional, but a necessity to preempt and prevent cyberattacks. By adopting continuous, automated ASM, organizations gain the real-time visibility and risk-based prioritization needed to address exposures in cloud sprawl, shadow IT, and the software supply chain. This allows security teams to move from a reactive, perpetual game of catch-up, to proactive, preemptive cyber operations, ensuring they are addressing exposures before their adversaries can exploit them.