Post
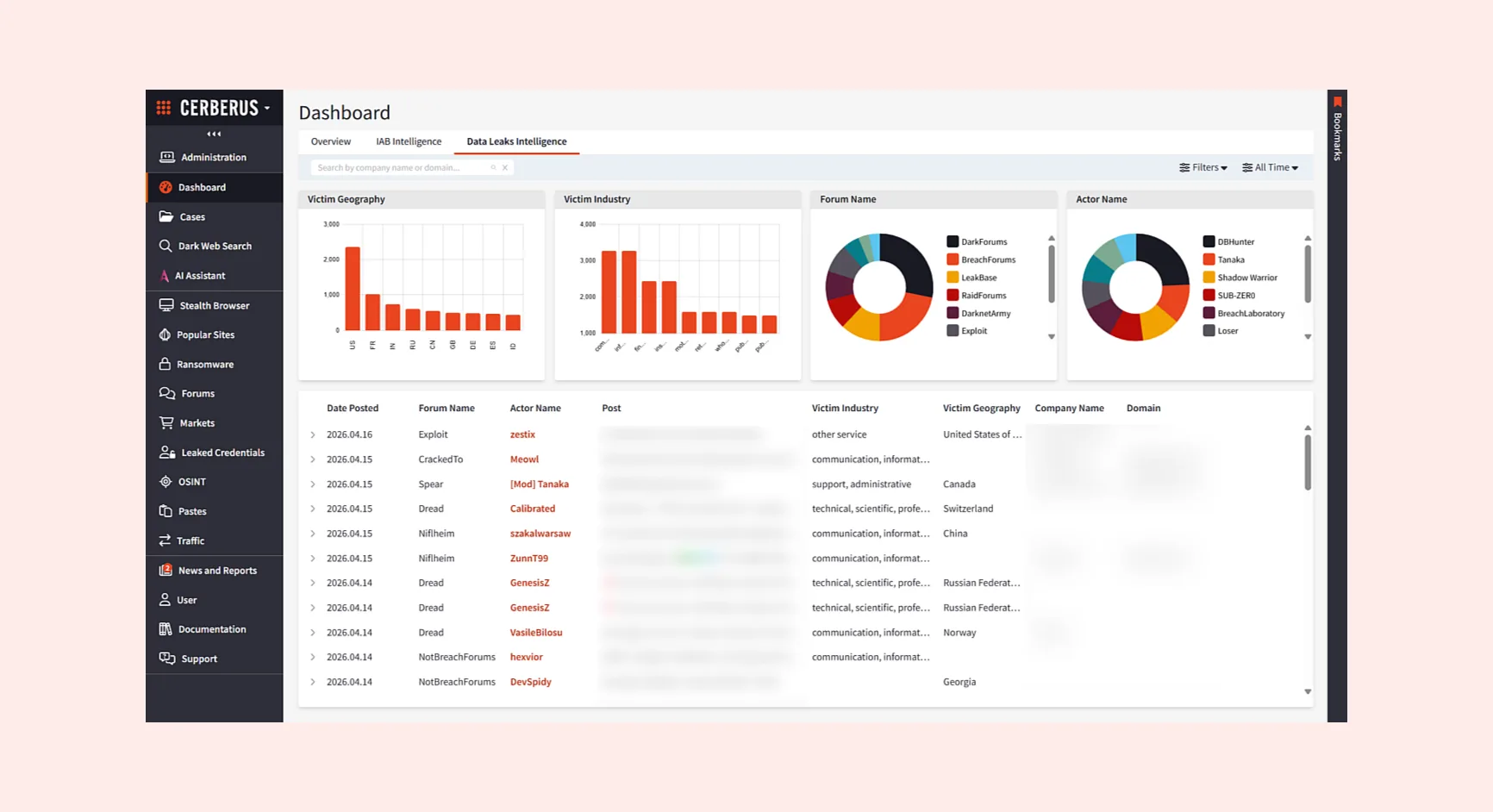
Users can now benefit from built-in third-party tooling, intuitive browser extensions, and optimized performance to support even more investigation use cases.
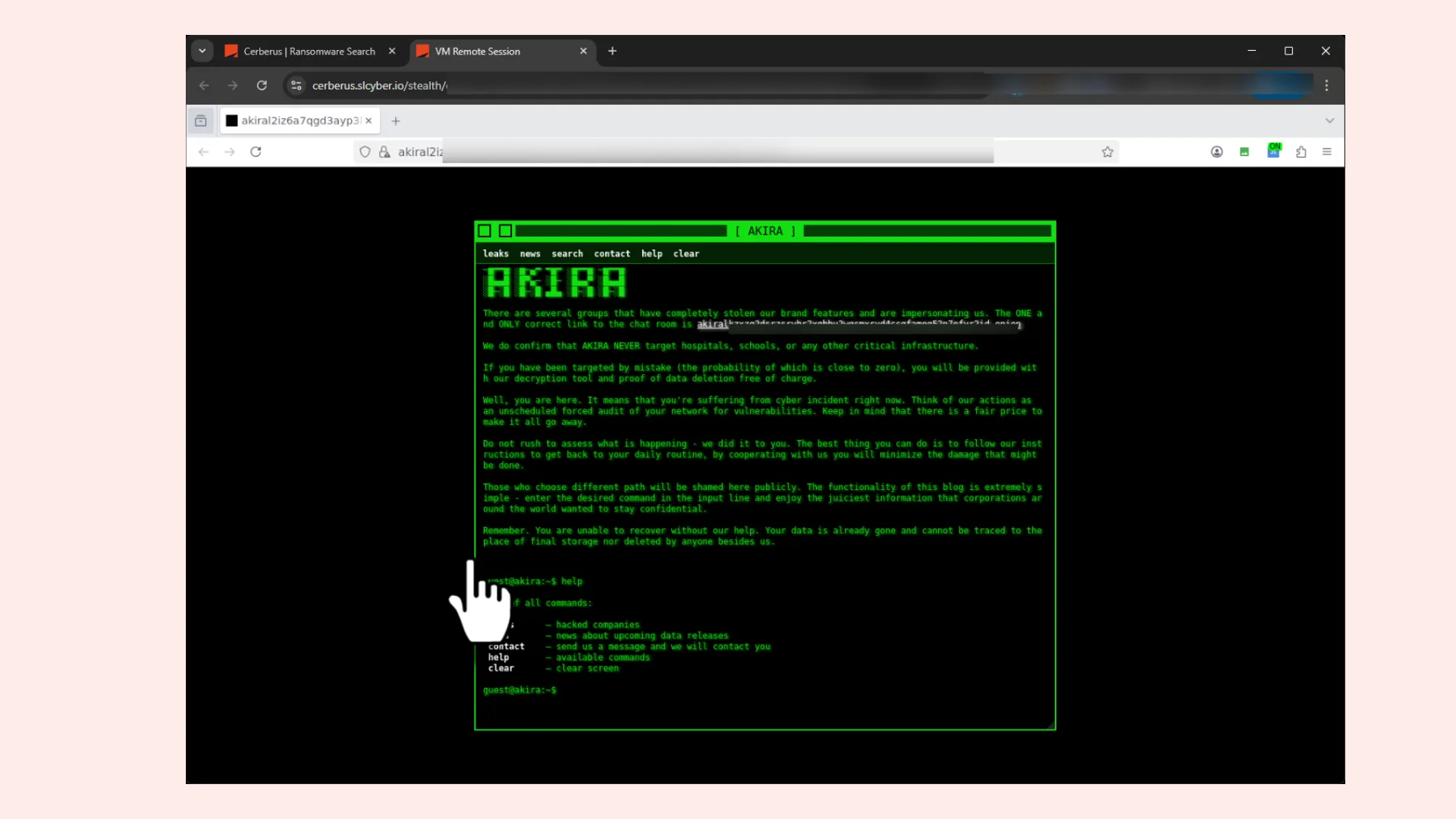
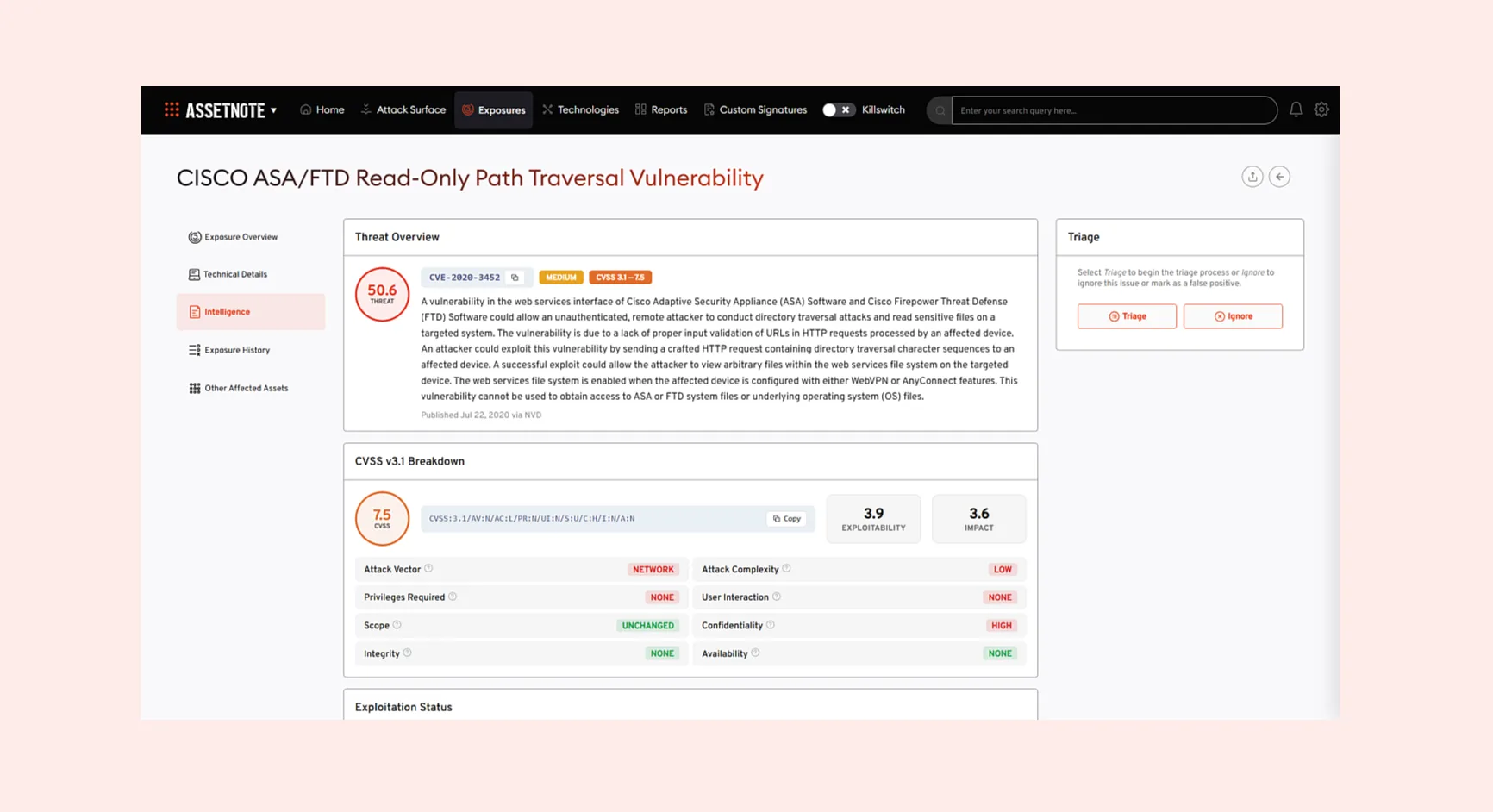
Searchlight’s Stealth Browser, a secure virtual machine used by cyber professionals to directly access the dark web, has just been updated. Now faster, it also features a broad range of new built-in investigative tooling, making it a more complete environment for secure intelligence gathering.
New third-party investigative tooling added to the Stealth Browser
As part of the latest update, users can now benefit from built-in access to third-party tooling to progress from initial discovery to active intelligence gathering within the virtual environment.
Data analysis and evidence handling
- LibreOffice – a full office suite for safely opening and reviewing documents, spreadsheets, and files within the secure VM environment
- SQLite – a lightweight database tool for querying and analysing exfiltrated SQL datasets and application data such as browser history or credential stores
Communication and browser tooling
- Discord – a widely used platform for monitoring communities, gathering intelligence, and communicating across investigations
- Firefox – a general-purpose browser for accessing clearnet sources alongside dark web investigation workflows
- Rocket Chat – a self-hosted messaging platform used across criminal and threat actor communities
- Telegram – an encrypted messaging application frequently used by threat actors and a key source of CTI
- Tor Browser – enables direct, anonymised access to .onion sites for dark web investigation
- Tox Chat – a decentralised, peer-to-peer encrypted messaging protocol used in cybercriminal contexts
Performance and security
- Beyond new tooling, the browser’s core has been refined to be faster and more responsive, ensuring stability during resource-heavy operations.
These enhancements make the Stealth Browser a more complete and unified environment, where you can find, download, and triage evidence while maintaining a strict, attribution-controlled security posture.