This week’s cybersecurity and dark web news stories discuss French government data breach, North Korean hackers targeting Web3 with new attack chain, and M3RX’s sudden spike in ransomware activity.
France’s Identity Document Agency Hit by Massive Data Breach
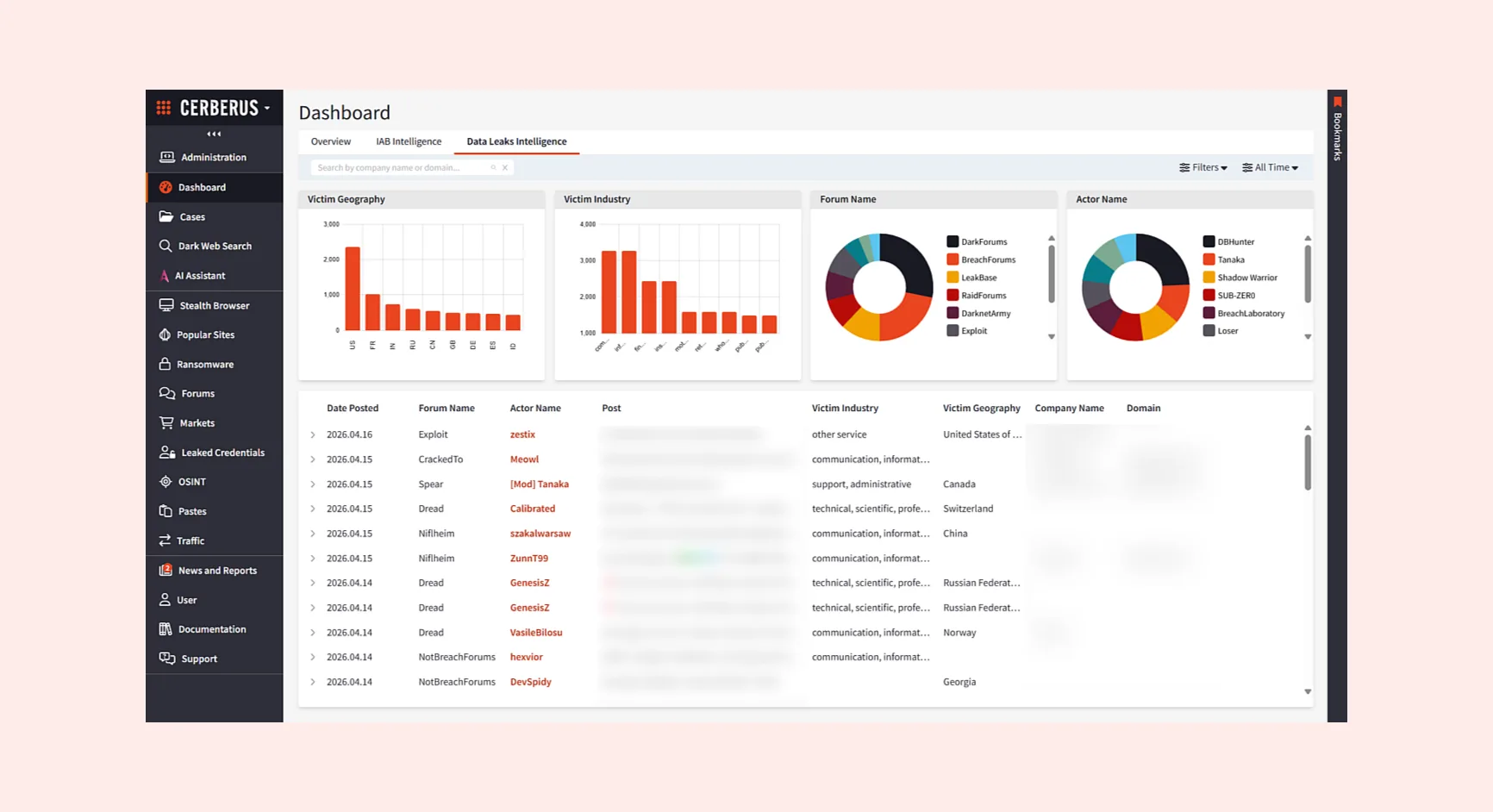
France’s national identity document agency has confirmed a significant data breach after a threat actor appeared on criminal forums advertising stolen citizen data for sale.
The Agence Nationale des Titres Sécurisés (ANTS) – which operates under the French Ministry of the Interior and manages official documents including driver’s licences, national ID cards, passports, and immigration documents – detected the attack on April 15, 2026. The following day, a threat actor using the moniker ‘breach3d’ claimed responsibility on hacker forums, alleging possession of up to 19 million records.
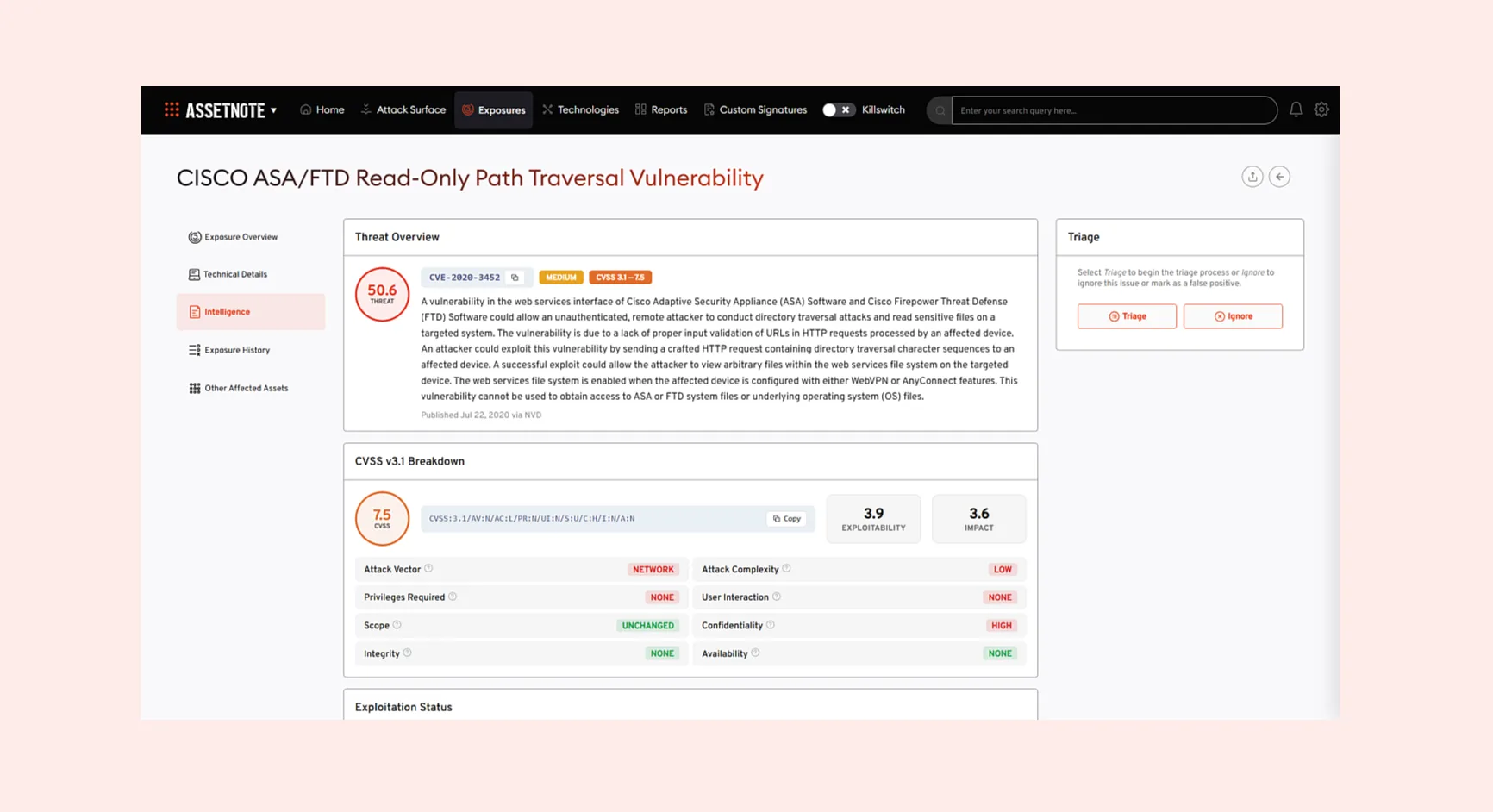
Security researchers noted that the attacker described the underlying vulnerability as elementary – characterised as “really stupid” – with technical analysis pointing toward an Insecure Direct Object Reference flaw on the ANTS API. That type of vulnerability allows an attacker to access another user’s data simply by manipulating a parameter in a request, requiring no sophisticated tooling.
ANTS has since confirmed that 11.7 million accounts were materially compromised. The threat actor’s claim of 18 – 19 million records likely reflects the total size of the database accessed, including records that may not correspond to active accounts. Confirmed stolen fields include full names, dates and places of birth, email addresses, home addresses, and phone numbers. Scanned identity documents were not affected.
ANTS notified France’s data protection authority, the CNIL, in line with GDPR requirements, filed a report with the Paris Public Prosecutor, and alerted ANSSI, the national cybersecurity agency. The Office anti-cybercriminalité (OFAC) has been brought in to lead the technical investigation.
Citizens are urged to be alert to phishing attempts. The combination of fields stolen creates a ready made profile for social engineering and identity fraud – full names, dates of birth, addresses, and phone numbers together allow attackers to craft convincing messages referencing accurate personal details, raising the success rate of phishing attempts well above generic spam. This breach is not France’s first: in February, officials disclosed unauthorised access to part of the national FICOBA bank-account registry, and in January 2026, the OFII immigration office confirmed foreign nationals’ data had been stolen via a subcontractor.
North Korean Hackers Target Web3 with Sophisticated New Attack Chain
Security researchers have published a detailed account of a full-lifecycle intrusion against a North American Web3 company, attributed with high confidence to BlueNoroff – a financially motivated subgroup of North Korea’s Lazarus Group.
The attack began with a Calendly invitation sent to the victim from an attacker impersonating a reputable figure in the Fintech legal space. The meeting was scheduled approximately five months in advance. Once confirmed, the calendar invite was covertly modified to replace the original meeting link with a typo-squatted Zoom URL.
When the victim clicked the link, they were directed to a convincing fake Zoom interface, but the deception ran far deeper than a spoofed login page. The HTML lure captured the victim’s live webcam feed via the browser’s getUserMedia API and streamed it in real time to attacker infrastructure. The fake meeting was populated with pre-recorded footage of prior victims, AI-generated portrait images, and deepfake composite videos – creating a self-reinforcing pipeline in which each successful compromise generated material to make the next attack more convincing.
Analysis of over 950 files from the attacker’s hosting server revealed that operator activity, when mapped to Korean Standard Time, was concentrated during standard DPRK business hours, Monday through Friday – consistent with a state-directed workforce on a regular schedule.
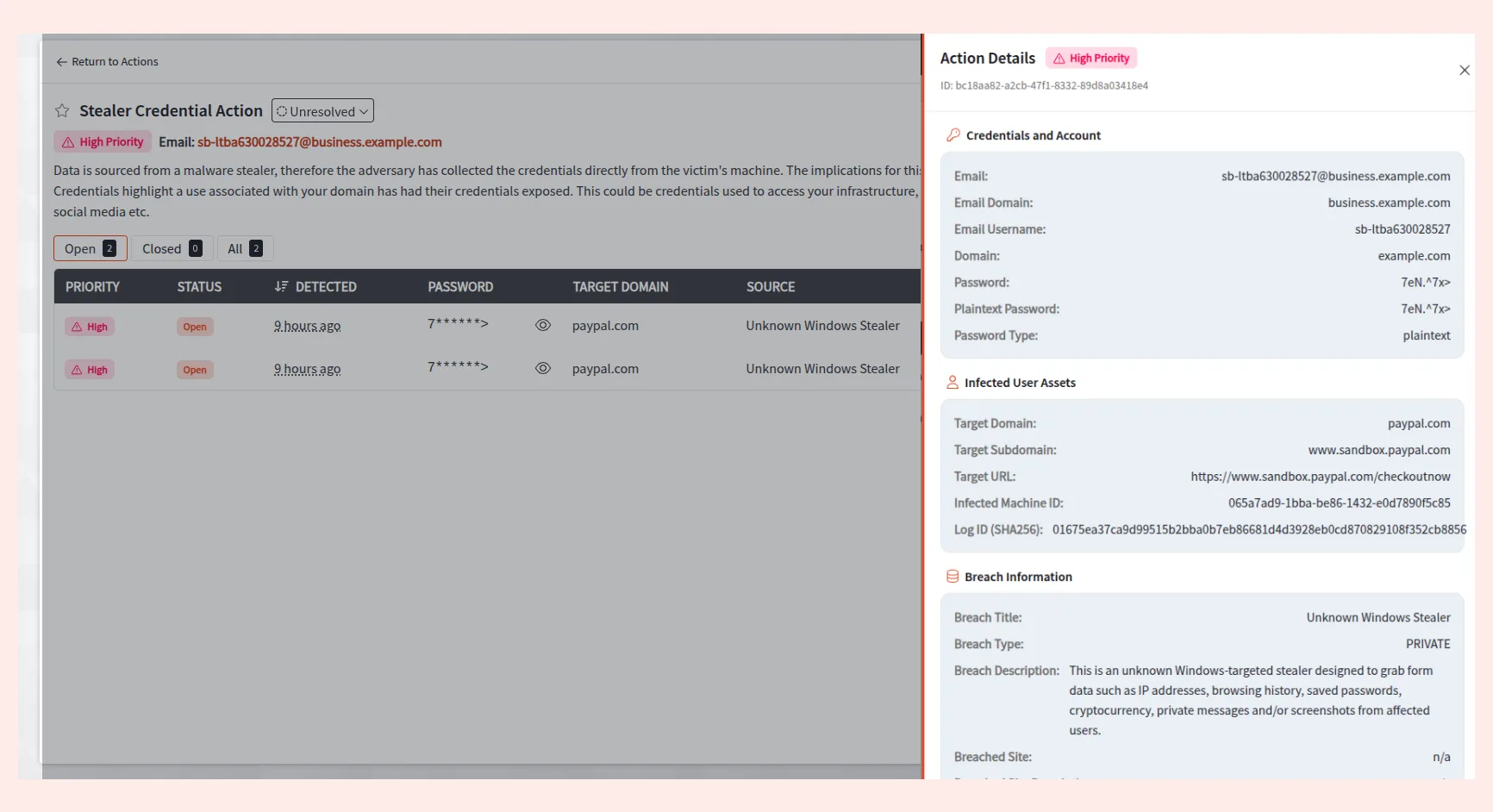
Eight seconds after the victim entered the fake meeting, a ClickFix-style prompt appeared claiming the Zoom SDK needed updating. Clicking it silently injected a PowerShell payload into the clipboard, which – once pasted and executed – established a C2 beacon, stole Telegram session data, harvested credentials from Chrome, Edge, and Brave, and injected an AES-encrypted browser stealer targeting cryptocurrency wallet extensions. The entire sequence from initial click to full system compromise completed in under five minutes.
Arctic Wolf identified 100 additional targets whose compromised media was hosted on attacker infrastructure, spread across more than 20 countries. CEOs and founders accounted for 45% of the target set, and 80% of identified targets operated in cryptocurrency, blockchain finance, or adjacent investment sectors.
M3RXDLS Dominates as Groups Hit Seven New Victims in 24 Hours
Ransomware activity remained steady on April 26, 2026, with seven newly confirmed victims across a broad range of industries and geographies in a single 24-hour window.
M3RXDLS was the most active group, accounting for five of the seven victims and affecting organisations across Switzerland and Australia. Brain Cipher claimed one victim in the UK construction sector, while Medusa – a persistent threat to healthcare – claimed optical firm Walman Optical in the United States.
The victim distribution showed no concentrated geographical or sector-specific campaign. Targeted industries included healthcare services, information technology, civil engineering, performing arts, automotive services, and medical devices – suggesting a distributed, opportunistic approach rather than a coordinated strike against critical infrastructure.
Year-to-date figures paint a sobering picture: 3,234 ransomware victims have been reported in 2026, with Q1 alone accounting for 2,622 of those. Q2 is tracking at a slower but consistent pace, with 613 victims recorded so far this quarter.
The Medusa group’s continued targeting of the healthcare sector is a recurring theme in recent reporting. Analysts note that while no new campaigns or CVEs were publicly disclosed in this reporting period, the absence of public news should not be read as a pause in activity. Ransomware operations frequently maintain a covert posture, and the lack of public reporting may simply reflect a quiet disclosure cycle rather than any reduction in real-world threat activity.